198
A Practical Guide to Security Assessments
the process of assigning values to the criteria is not an exact science and that some
judgment will be required. The next two sections will discuss each of these concepts
in detail and provide criteria for assigning numerical values to each of the variables.
Business Impact
Business impact is a combination of the potential impact to the business if there is
a security breach and the probability that a security breach could occur. In this
methodology, business impact is calculated without the consideration of any internal
controls or security measures that might be in place. The existing security measures
and internal controls will be accounted for when the “level of control” is determined.
As a result, in determining the business impact, only the probability of a security
breach and the potential impacts of a security breach are examined.
To quantify these characteristics, Table 8.1 and Table 8.2 offer guidance for the
potential impact to the business and the probability that a security breach could
occur. Each table contains guidance for determining a high, medium, or low score
for each of the characteristics. The high, medium, and low scores translate to scores
of 3, 2, and 1 respectively. This numerical value will be used in the calculation of
business impact.
Table 8.1 addresses the potential impacts to the business. This is information
that should have been gathered in previous meetings with business process and
technology owners. If needed, the client subject matter experts should be consulted
with again to thoroughly understand the impacts of the security risks identified.
Table 8.1 lists criteria for assigning numerical values for potential impact to the
business. Note that this is a guideline — it can be modified if needed for a given
client as different clients may have different criteria. Note: When doing this analysis,
finalize this criteria first so that all findings are measured based on the same criteria.
The examples of potential impacts are there to help you determine the best classi-
fication of a given risk.
The criteria above should help you classify impact of your findings in a consistent
manner. Note that a given finding does not have to meet all of the items listed in a
particular category. For example, you could have a finding that you classify as having
a “high” business impact because of the cost to address the security breach even
though an effective workaround exists. You might also classify this risk as a
“medium” because there was an effective workaround. This is where your judgment
comes in and why there is a fair degree of subjectivity to this process. The key is
to apply your judgment as consistently as possible.
Table 8.2 defines the criteria for assigning values to the probability that a breach
could occur. In this methodology, probability is thought of as a high, medium, or
low likelihood that the vulnerability associated with a finding can be exploited. Like
the last one, this is a highly subjective calculation and will require judgment and a
good knowledge of the business. Also, you must apply your judgment consistently
across all findings. This probability combined with the potential impact will be used
to calculate the business impact.
As you can see, both components that determine the business impact are highly
subjective and require judgment. The second component, the probability of a security
AU1706_book.fm Page 198 Tuesday, August 17, 2004 11:02 AM
Risk Analysis and Final Presentation
199
TABLE 8.1
Potential Impact to the Business
Score Potential Impacts
High 3 Significant revenue impact
No effective workaround
Core business processes adversely affected
Permanent loss of customers
Potential litigation
Regulatory fines can result from a security breach
Significant damage to reputation — to the extent that it might cause a loss of
customers
Significant expense to address security breach — e.g., outside consultants required,
major expenses related to data recovery
IT systems unavailable for an extended period of time and contingency plans need
to be invoked to remain operational
Critical data might not be recoverable
Medium 2 From a customer’s perspective, the impact was nothing more than a nuisance
There is a workaround but it is very cumbersome and not sustainable for an extended
period of time
Minimal or no loss of customers
Minimal revenue impact
Minimal damage to reputation
Core business process is minimally affected
Regulatory warning (as opposed to a fine)
Security breach was addressed with internal resources (who were not able to
perform their daily responsibilities for a significant period of time as a result of
the breach)
Critical data is recoverable with significant effort
Low 1 No revenue impact
Effective workaround
Ancillary or back-office processes affected, not core business processes
No impact to customers
No damage to the reputation of the company
Affected business process will be phased out or be radically changed in the short
term
TABLE 8.2
Assigning Values
to Probability
Score
High 3
Medium 2
Low 1
AU1706_book.fm Page 199 Tuesday, August 17, 2004 11:02 AM
200
A Practical Guide to Security Assessments
breach, is extremely subjective but necessary in calculating the potential impact. If the
probability of a given vulnerability being exploited is low, this should be considered
in the overall risk analysis and when making recommendations. In some cases, if
the probability of a particular vulnerability being exploited is low, you may consider
accepting the risk and doing nothing about it. Although the probability could have
been incorporated into the potential impact, it is important enough to consider
separately. In fact, when presenting the findings from a security assessment, one of
the questions you might get is — “What are the chances of that happening and how
has that been incorporated into the risk analysis?”
Another typical question you get is, “Assuming that a security breach did occur,
is there a workaround that can be done so the business process is not disrupted?”
For this reason, workarounds are specifically mentioned in the Potential Impact table.
To make this process work, the importance of applying your judgment in a
consistent manner cannot be stressed enough. One way to help ensure this is to
document your thought process of how you arrived at the values for business impact.
Calculation of Business Impact
To calculate the business impact of a given risk, the scores for the probability and
the potential impacts are multiplied. This product of the two items is the overall
business impact shown below.
Business Impact = Probability
×
Potential Impact to the Business
This result is then combined with the level of control (discussed in the next section)
to determine the priority.
Below is an example of the calculation of business impact:
Scenario:
Company X is an online bookstore that sells books where customers can
order online or call-in orders on the Internet. During a security assessment, technical
security issues were found on critical servers. There were findings related to security
patches not being up to date as well as some weak access controls.
Analysis of Business Impact
Probability —
Based on the findings and some of the recent exploits, there is a
medium chance that a security breach could occur as a result of this finding.
Probability — Medium (2)
Potential Impact to the Business
— Based on the findings, the worst-case scenario
if a security breach were to occur is that the site would be unavailable for a couple
of hours at the most. There would be a minimal loss of revenue, if any, because
online sales are not a significant portion of the sales.
In addition, customers know
that they can call in orders if the Web site is not working. As a result, the potential
impact to the business is medium.
AU1706_book.fm Page 200 Tuesday, August 17, 2004 11:02 AM
Risk Analysis and Final Presentation
201
Potential Impact to the Business — Medium (2)
Business Impact = Probability
×
Potential Impact to the Business
4 = 2
×
2
The ranges for the overall business impact are as follows:
The overall business impact is then 4,
which is a medium-level business impact.
This was calculated by multiplying the probability and the potential impact to the
business.
To illustrate some variations to the example above, let us assume that the client
did not have good management controls and that the lack of security patches could
result in credit card numbers being stolen. In addition, let us assume that these
vulnerabilities were being exploited frequently. Under these circumstances, both the
probability of a security breach and the potential impact to the business are high,
resulting in a score of 9, which is a high level of business impact.
Based on the potential business impact scores, there is only one case of a high
business impact and that is when both components — probability and the potential
impact to the business — are high. This is intentional so as not to dilute the urgency
and importance of business impacts classified as “high.”
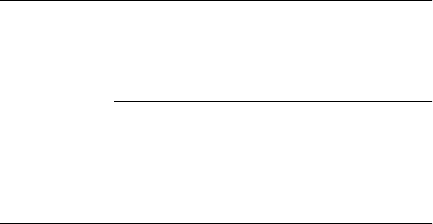
Table 8.3 illustrates the levels of business impact and what the results of various
combinations are.
Level of Control
The level of control is the second aspect in determining overall risk score. In the
first step of determining the risk score, we determined the following information
based on the findings:
TABLE 8.3
Business Impact
Probability
Potential Impact to the Business
Low Medium High
123
High 3 3 — Medium 6 — Medium 9 — High
Medium 2 2 — Low 4 — Medium 6 — Medium
Low 1 1 — Low 2 — Low 3 — Low
Business Impact Range
Low 1 to 3
Medium 4 to 6
High 7 to 9
AU1706_book.fm Page 201 Tuesday, August 17, 2004 11:02 AM
202
A Practical Guide to Security Assessments
• What is the potential impact of a security breach?
• What is the likelihood that the security breach might occur?
Theoretically, the potential impact and the probability are really only half the story.
The other half, which is considered in this section, is the controls or security
measures in place to mitigate the risks associated with the vulnerability.
Consider the example of company having a business-to-business relationship
with a supplier that manages inventory levels of certain items by having access to
company’s systems to view inventory levels. This relationship can shorten the supply
chain by automating the process of replenishing inventory. With this type of a
relationship, companies can save money by making the inventory replenishment
process more efficient and because certain activities that used to be performed by
people are now automated. These relationships, which keep a company competitive,
introduce new security risks into the environment. To mitigate these risks, companies
might implement the following:
• Strict access controls around who can access inventory information
• Log reviews of business-to-business transactions
• Strong password requirements
• Other controls
These measures to mitigate the risk constitute the “level of control,” which is the
subject of this section.
The level of control can range from manual internal control processes such as
log review to system-enforced security measures such as strong password require-
ments. Ideally, security measures should be driven by the amount of risk, which is
a fundamental concept in the security assessment methodology.
The level of control is the second component in determining risk and is defined
as the measures that have been taken by the company to mitigate the risks associated
with vulnerabilities. As with the criteria for the business impact, this is also subjec-
tive. Also, the criteria can be adjusted based on the client and your judgment — you
just need to make sure that you apply your judgment consistently for all findings.
The level of control can be thought of at five levels, which are outlined in Table
8.4. Table 8.4 lists the criteria that should be used in determining the level of control
for a given risk. The level of control should be reviewed for each set of findings and
associated risks. The numerical values range from 1 to 5 with 1 as the best-case
scenario and 5 as the worst-case scenario. The key differences for each level of
control are in italics.
Note the differences as you progress from 1 to 5 in the table. The items listed
in the criteria represent key aspects of information security, some of which were
identified as key components of an information security program (Chapter 3). As
with the business impact, you can add items to these criteria or take away items;
this is again a judgment call on your part. Remember that you need to justify how
you came to your conclusions when you classify these risks.
Some salient points related to the criteria for the level of control that you should
be aware of as you proceed are:
AU1706_book.fm Page 202 Tuesday, August 17, 2004 11:02 AM
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
