170
A Practical Guide to Security Assessments
• What initiatives are being planned for IT? Are any security related?
– Examples of potential initiatives include e-commerce, outsourcing, use
of ASPs (Application Service Providers), and business-to-business
(B2B).
• What concerns does IT management have relative to information security?
– Is IT management concerned about any specific security issues? If
there are any, what is being planned to mitigate the potential risks?
•How is the communication between IT and the rest of the business?
– Are there any liaisons that facilitate communication between IT and
everyone else?
The questions above are a generic set of questions to get you started. You can
add to these questions or take away items that you might already know about. If
you are adding questions, keep in mind that you are dealing with someone from
management — i.e., you are better off keeping your questions high level.
With the information learned in this meeting, you are ready to begin developing
question sets to use when meeting with the specific technology owners. By this time,
you should also have finalized which technology owners you will need to meet with.
Based on how long you will need to develop the question sets, you should tell your
single point of contact to begin setting up the meetings with the technology owners.
DEVELOP QUESTION SETS
FOR TECHNOLOGY REVIEWS
Now you are in a position to develop and finalize the question sets for your meetings
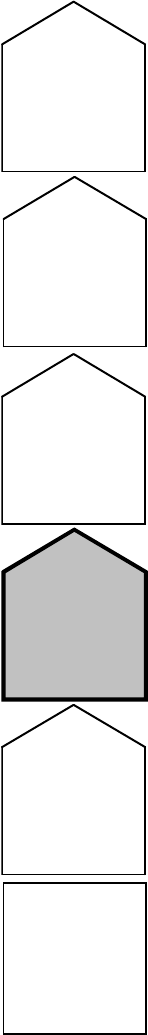
with technology owners (Figure 7.2). Similar to the list of topics and questions
developed for the business process subject matter experts, a similar list should be
developed for the technology owners. The question sets for the technology owners
are as important as the last set. They will help you prepare for the meetings and
help you ensure that all relevant topics are covered.
The structure of the suggested question sets for the technology owners is similar
to that of the question sets for the business process owners. There will be a set of
generic questions that can be asked to all of the technology owners. To develop the
specific questions, you must leverage what you learned from the business process
evaluation, the meeting with IT management, and any information you learned from
the initial research about the company. The answers to these questions along with
the detailed technical review later in this phase will provide you with what you need
to properly evaluate the technology environment from a security perspective.
The generic questions that will be used in the meetings with technology owners
will focus on what technology they are responsible for, how they manage it, how
they secure it, and various other aspects. In addition to that, there will be some
specific questions for the person you are talking to based on that individual’s job
AU1706_book.fm Page 170 Tuesday, August 17, 2004 11:02 AM
Technology Evaluation
171
FIGURE 7.2
Develop question sets for technology reviews.
Evaluate
Technology
Environment
General review of
technology and
related
documentation
Develop
question sets
for
technology
reviews
Meet with
technology owners
and conduct hands
on testing
Analyze
information
collected and
document findings
Status meeting
with client
AU1706_book.fm Page 171 Tuesday, August 17, 2004 11:02 AM
172
A Practical Guide to Security Assessments
function. Below are generic questions that can be used as a starting point, which
can be used in security assessments (this will also be included in the appendices):
•
What technology are you responsible for and what business process does
it support?
With your knowledge of the business, you should have some
perspective on how the technology supports the business. However, the
IT person will be able to give you a different angle on how it supports
the business. In some cases, there might not be a specific business
process — e.g., a server that handles authentication into the network does
not necessarily support a particular business process — it is providing
access so users can do their job. In other cases, the technology owner
might be managing an application that supports a mission-critical business
process.
•
Where does it fit into the overall architecture?
Assuming that a network
topology diagram is in place, you should be able to see where the tech-
nology fits into the IT environment. This is very helpful because it gives
you a visual perspective and highlights the relationships with other parts
of the IT environment. The relationships with other parts of the IT envi-
ronment will likely generate other questions regarding integration points,
transmission of information, and other topics.
•
What are the key dependencies for the technology you manage?
The key
dependencies for any technology are the components that must be func-
tional for the technology in question to work properly. A simple example
is business to commerce (B2C). For B2C to be functional, access to the
Internet is required.
•
What are the security requirements from a security perspective — e.g.,
confidentiality, integrity, and availability? Are these requirements being
met?
From the discussions with the business process owners, you should
have a good sense for what these requirements are. The purpose of this
question is to determine whether the technology owner is aware of the
security requirements and whether those requirements are being met. One
thing to look for here is whether the process and technology owners have
the same perspective on security. If not, you can delve further into how
the different groups communicate with each other.
•
How is the technology secured?
This is a follow-up on the previous
question. When you are talking about how it is secured, a number of
aspects including access controls, physical security, and integrity controls
should be included in the discussion. The methods depend on the tech-
nology. This question will probably lead to a technical discussion, for
which it is important to be prepared to talk at a technical level.
•
How is security enforced?
If security is not enforced, its value is dimin-
ished significantly. Enforcement efforts can be automated or manual. To
the extent that enforcement can be automated, it should be. Other methods
of enforcement include periodic reviews and audits.
•
Does critical data reside on any system you manage? If so, how is it
secured?
From your business process interviews, you should know what
AU1706_book.fm Page 172 Tuesday, August 17, 2004 11:02 AM
Technology Evaluation
173
critical data exists. This is an opportunity to get the perspective of the IT
person, which should hopefully be in line with what you know already.
Once you learn how the information is secured, you can determine whether
the level of security is appropriate based on the criticality of the data.
•
If the systems you manage were not available, how quickly could they be
functional?
With this question, you will have to go through several dif-
ferent scenarios because all system failures are not the same. The goal
with this question is to get a range of times for how long the systems can
be unavailable and whether these ranges are acceptable based on the
availability requirements that the business has. This is one of the areas
where there is often a disconnect between IT and the business. It is both
a communication and a budget issue. For example, there is a big difference
in guaranteeing four-hour maximum downtime and one business day
maximum downtime on a given system. A classic example is e-mail. Many
people will tell you that they cannot do any work without e-mail and that
half a day is about all they can tolerate. When you start looking at what
it costs to meet a half-day maximum downtime requirement, the tolerable
downtime will likely change and other methods of communication such
as the telephone might become more of a viable option.
•
What type of logging and monitoring activities do you perform?
For key
machines or devices, some level of logging and monitoring should be
taking place. For example, for critical servers, does anyone review any of
the event logs or any of the other relevant logs? How much log review
and monitoring activity occurs provides some indication of how proactive
or reactive the company’s security measures are. The level of logging and
monitoring is often a function of how many people the client has to do
the work and the risks that the company faces.
•
Is a formal change management process followed for any changes to the
technology managed?
Whether or not a change management process is
followed is an indicator of how controlled the environment is. If no change
management process is followed, it can lead to more questions depending
on the technology. At a minimum, a lack of a change management process
should be flagged as an issue.
•
Have there been any security incidents with any of the technology you
manage?
This question is the same as what was asked to the process
owners. This is good information because it provides some clues about
what vulnerabilities might exist, what the impacts are, and what manage-
ment did to ensure that it does not happen again. If an incident occurred,
find out the details and ask about how it was handled and what subsequent
steps were taken to prevent it from happening again.
•
Are there any changes planned for the technology you manage? If so,
have the security implications been considered?
Planned changes can
affect your evaluation depending on what they are. Some examples include
a major overhaul of the technology, change in architecture, changes in
organization, merger or acquisition activity, and outsourcing. If any new
initiatives are planned, you should find out if security is (was) considered
AU1706_book.fm Page 173 Tuesday, August 17, 2004 11:02 AM
174
A Practical Guide to Security Assessments
in the planning process. Any changes that the technology owner can talk
about are worth discussing because they will affect your evaluation.
•
Other questions as a result of the information gathered:
These are the
customized questions you will generate based on what you have learned
so far. Some of the specific questions should be detailed questions about
the configuration of the technology being managed and the activities
required to administer it.
The questions above should be modified to the extent you feel necessary. You
can add to these questions and use the question sets in the appendices as a guide.
Although the questions above are general, you might have already gone over much
of this from your other interviews. This is particularly true in smaller environments
where everyone knows what everyone does. In larger environments, it is definitely
worth asking the questions, as you will find cases where little communication occurs
between IT and the business. As a result, there is a gap between what the business
is expecting from a technical security perspective and what is actually being done.
MEET WITH TECHNOLOGY OWNERS
AND CONDUCT DETAILED TESTING
Meeting with the technology owners (Figure 7.3) is the second set of meetings where
you will gather significant information for the security assessment. At this point,
you have a good understanding of the business, what some of the key risks are, and
what the critical technologies are. You are ready to go deeper into the technology
and determine whether the level of security is appropriate. In preparation for the
meetings with the technology owners, two key steps should be taken:
•
Developing the question sets for the meetings
— In the previous step of
the methodology, we discussed the development of the question sets, so
they should be completed. In preparation for meetings with technology
owners, questionnaires should be given to the technology owners in
advance. This allows them to be prepared for the meeting and bring in
any other resources that might be necessary to answer your questions.
When developing the question sets, it is critical to customize the questions
as much as possible. This will help you in spending more meaningful
time with the technology owners. It is important to recognize that tech-
nology owners are involved in day-to-day operations, and in some com-
panies, smaller ones in particular, their time is typically stretched very
thin. It is therefore critical to make the most of your time with them. It
is in everyone’s interest to be as efficient as possible.
•
Preparing the technology owners —
Similar to business process owners,
technology owners must be educated about the security assessment so
that when they are asked questions, they are not caught off guard. One
of the worst things that can happen is going to a meeting and having the
person say to you, “Why are you here?” or “I don’t know anything about
AU1706_book.fm Page 174 Tuesday, August 17, 2004 11:02 AM
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
