67
4
Planning
Once the decision is made that a security assessment will be performed, careful
planning must be done to ensure that it is smooth and efficient. Good planning will
save time and yield better results. Planning for the security assessment refers to
logistic aspects such as scheduling with the client, specifically the subject matter
experts who will participate in the security assessment. The key task in this phase,
which will influence the scheduling and resources, is the scope definition process.
You must be able to define what you are going to do in the security assessment so
that you can properly plan the time and resources to complete the assessment.
The key activities in the planning phase of the security assessment are listed
below and will be discussed in detail in this chapter:
• Defining the scope
• Staffing
• Kickoff meeting
•Development of the project plan
• Setting the expectations of the client
DEFINING THE SCOPE
The scope should define and put some boundaries around your work. Defining the
scope (Figure 4.1) is one of the most important steps in a security assessment because
it influences everything else you do. This is especially the case in larger organizations
where there is much to review but less so in smaller companies where virtually every
part of the business will be part of the scope. Developing the scope should be a two-
way conversation between yourself and the client. Although the client might have
some ideas about the scope, you should also use your own expertise to offer advice
to the client on defining the scope.
Implications that you must think about as the scope is being developed include:
•
Time and resources required to complete the assessment
— You will need
to schedule the right number of resources with the right skill sets.
•
Upcoming changes to the business that might affect the scope
— If certain
changes in the business are upcoming, they might affect the scope and
thus, should be considered.
Being clear on the scope of the security assessment is ultimately beneficial for
everyone. From the perspective of the party performing the assessment, it is impor-
tant in planning and also in meeting the expectations of the client. From the per-
spective of the client, it provides a clear idea of the work to be performed.
AU1706_book.fm Page 67 Tuesday, August 17, 2004 11:02 AM
68
A Practical Guide to Security Assessments
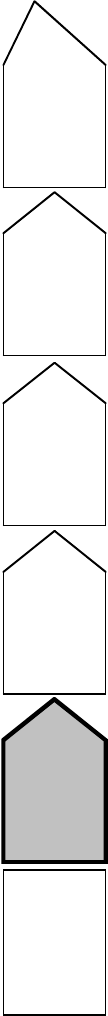
FIGURE 4.1
Define scope.
Planning
Define scope
Staffing
Kickoff meeting
Develop project
plan
Set client
expectations
AU1706_book.fm Page 68 Tuesday, August 17, 2004 11:02 AM
Planning
69
If the scope of the security assessment is not clearly defined right in the begin-
ning, it can be very detrimental to the entire assessment process because of the gap
between the work performed and the client’s expectations. How do we close the gap
and ensure that everyone is on the same page as it relates to the security assessment?
Essentially, the scope has to be defined in enough detail so that everyone understands
it. One major mistake that is sometimes made is to define the scope at such a high
level that there is too much room for interpretation, resulting in inconsistent views
of the scope of work.
To properly define the scope, you must first understand what the business drivers
are for the security assessment. This will probably not be clear until you discuss
with the client why a security assessment is desired in the first place. Security
assessments may be conducted for a variety of reasons. By having a clear under-
standing of the reasons for the assessment, you will be able to work with the client
to develop the scope and set their expectations. You will find that you end up guiding
the client in the scope definition process by discussing the business drivers.
Business drivers can vary and can include such things as regulatory concerns or
significant changes that have taken place in the environment. Using business drivers,
you can help the client “put a box” around what needs to be in the scope of work.
This is probably the most critical aspect of defining the scope and where the actual
scope is defined.
Once the scope is defined, the next step is to agree to a set of standards or
benchmarks that will be used in the assessment. These can be the clients’ own
security policies and procedures, specific laws such as the Health Insurance Porta-
bility and Accountability Act (HIPAA), or a set of external standards such as Inter-
national Standards Organization (ISO) 17799. It could also be a combination of
standards. You should offer your expertise in helping to determine what standard
would be appropriate.
Once the scope is defined and the standards are agreed to, you must manage to
the agreed-upon scope. One of the most significant issues you deal with is “scope
creep,” which is essentially changing the scope of the work once it has begun. The
changes can include increasing or completely changing the scope. Both of these
problems can lead to an unsuccessful assessment.
Four important aspects of scope definition are:
• Business drivers
• Items to include in the scope
• Standards
• Managing the scope
In the subsequent sections, each of these aspects of scope definition will be discussed
in greater detail.
B
USINESS
D
RIVERS
As stated earlier, understanding the business drivers or reason for the security
assessment is critical in defining the scope. It will not only affect the scope from a
coverage perspective, it will also affect the approach in terms of what standards are
AU1706_book.fm Page 69 Tuesday, August 17, 2004 11:02 AM
70
A Practical Guide to Security Assessments
selected as benchmarks and the nature of the content of the final report. Business
drivers can vary greatly and are dependent on a number of factors including:
• Management’s attitude on the importance of information security
• The risk environment in which the company operates
• Changes happening in the business (e.g., significant employee turnover,
merger or acquisition)
• Security-related events that may have taken place — e.g., an incident in
which systems were compromised
The business drivers for the assessment will help determine how wide or narrow
the scope is and what type of information the client is seeking. The main business
drivers you will see when conducting security assessments include:
• The client is taking a proactive approach to security.
•Regulatory concerns have prompted the assessment.
• The client wants to justify additional funds for information security
initiatives.
•A security incident has occurred.
• Disgruntled employees have been terminated.
• Changes have occurred in the information technology (IT) environment.
•A merger or acquisition is under consideration or has occurred.
Each of these business drivers is discussed in detail below.
Proactive Approach to Security
This is the ideal scenario for any company. Companies that are proactively looking
at their information security programs probably have some part of an information
security program already in place, but because of changes in the business or because
they have not reviewed security in some time, they want to determine how well their
information security program is addressing the risks facing them. In this scenario,
clients want to know where they can improve and what steps they need to take on
a short-term and long-term basis to ensure their environment is secure — i.e., a
security roadmap that will help them identify and prioritize security-related initia-
tives. These clients are likely to have an assessment done on a regular basis, where
each assessment builds on the one previously performed. These clients will also
likely want to look at most of the environment in the first assessment and then focus
on specific areas in future periodic assessments.
From a scope perspective, these clients want to look at everything. They tend
to be cautious and want to make sure that their information security program is
adequate. As a result, it can be challenging to effectively scope this type of assessment.
Regulatory Concerns
HIPAA, the Gramm–Leach–Bliley Act (GLBA) and other laws have forced compa-
nies to have information security programs. Companies can face significant fines if
AU1706_book.fm Page 70 Tuesday, August 17, 2004 11:02 AM
Planning
71
these requirements are not adequately addressed. With the breadth of some of these
requirements, companies often do not know where to start, so an assessment is
performed to determine what needs to be done to become compliant with a given
law or regulation. In fact, for both HIPAA and GLBA, part of the legislation includes
a requirement to conduct a risk analysis. Clients having an assessment conducted
based on regulatory concerns want to know the specific steps to take to achieve
compliance. You will definitely use the law or regulation to help define scope and
as a standard against which to measure the information security program.
The deliverable resulting from this type of security assessment should be a set
of findings, risks, and recommendations that will identify security initiatives to help
achieve compliance with the law or regulation that is relevant to the client’s industry.
Because the client is most concerned with achieving compliance, the findings should
map back to specific parts of the law or regulation and the recommendations should
help ensure compliance. This type of document is also useful to show to government
auditors who audit for compliance with a given law or regulation.
Justification for Additional Funds for Information Security Initiatives
In companies today, budgets are very tight and most expenditures are questioned,
particularly those for which a solid return on investment (ROI) cannot be shown.
With information security, it is sometimes difficult to justify money because of the
perception that information security initiatives are not necessary. The attitude “noth-
ing has happened, so why spend money for security” often prevails.
Management does not always understand the risks associated with a security
weakness and that spending money proactively to fix something is far cheaper than
letting a security incident take place and dealing with the aftermath. In these cases,
a security assessment can highlight areas of concern and demonstrate what risks are
present in a given environment. The security assessment can also look at the risks
in aggregate and show management the potential impacts of potential security
incidents. This type of exercise helps management see where it might be smart to
invest in securing the assets of the company. Clients who are looking to justify
funding probably have an idea of where they want to spend the money. In these
cases, the assessment may be focused on one or a small set of areas. One thing to
keep in mind is that you should always provide input on where it makes sense to
include or not include items in the scope of work.
Security Incident Has Occurred
For some companies, the importance of information security is not always apparent.
For these companies, if security is not tied to avoiding something tangible, such as
loss of revenue, additional cost, or negative publicity, they do not necessarily see
the value of information security. It sometimes takes a security incident to make them
notice the importance of information security. An incident such as a Web site being
defaced or a network being compromised can immediately raise security awareness.
After the realization that a security incident took place, the next questions from
management are “what other security weaknesses do we have and how do we prevent
AU1706_book.fm Page 71 Tuesday, August 17, 2004 11:02 AM
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
