Chapter 13
Network Address Translation (NAT)
The following ICND1 exam topics are covered in this chapter:
- Operation of IP Data Networks
- Predict the data flow between two hosts across a network
- IP Services
- Identify the basic operation of NAT
- Purpose
- Pool
- Static
- one-to-one
- Overloading
- Source addressing
- One-way NAT
- Configure and verify NAT for given network requirements
In this chapter, we’re going to dig into Network Address Translation (NAT), Dynamic NAT, and Port Address Translation (PAT), also known as NAT Overload. Of course, I’ll demonstrate all the NAT commands. I also provided some fantastic hands-on labs for you to configure at the end of this chapter, so be sure not to miss those!
It’s important to understand the Cisco objectives for this chapter. They are very straightforward: you have hosts on your inside Corporate network using RFC 1918 addresses and you need to allow those hosts access to the Internet by configuring NAT translations. With that objective in mind, that will be my direction with this chapter.
Because we’ll be using ACLs in our NAT configurations, it’s important that you’re really comfortable with the skills you learned in the previous chapter before proceeding with this one.
When Do We Use NAT?
Network Address Translation (NAT) is similar to Classless Inter-Domain Routing (CIDR) in that the original intention for NAT was to slow the depletion of available IP address space by allowing multiple private IP addresses to be represented by a much smaller number of public IP addresses.
Since then, it’s been discovered that NAT is also a useful tool for network migrations and mergers, server load sharing, and creating “virtual servers.” So in this chapter, I’m going to describe the basics of NAT functionality and the terminology common to NAT.
Because NAT really decreases the overwhelming amount of public IP addresses required in a networking environment, it comes in really handy when two companies that have duplicate internal addressing schemes merge. NAT is also a great tool to use when an organization changes its Internet service provider (ISP) but the networking manager needs to avoid the hassle of changing the internal address scheme.
Here’s a list of situations when NAT can be especially helpful:
- When you need to connect to the Internet and your hosts don’t have globally unique IP addresses
- When you’ve changed to a new ISP that requires you to renumber your network
- When you need to merge two intranets with duplicate addresses
You typically use NAT on a border router. For example, in Figure 13-1, NAT is used on the Corporate router connected to the Internet.
Figure 13-1: Where to configure NAT

Now you may be thinking, “NAT’s totally cool and I just gotta have it!” But don’t get too excited yet because there are some serious snags related to using NAT that you need to understand first. Don’t get me wrong—it can truly be a lifesaver sometimes, but NAT has a bit of a dark side you need to know about too. For the pros and cons linked to using NAT, check out Table 13-1.
Table 13-1: Advantages and disadvantages of implementing NAT
| Advantages | Disadvantages |
| Conserves legally registered addresses. | Translation results in switching path delays. |
| Remedies address overlap events. | Causes loss of end-to-end IP traceability |
| Increases flexibility when connecting to the Internet. | Certain applications will not function with NAT enabled |
| Eliminates address renumbering as a network evolves. |
Types of Network Address Translation
In this section, I’m going to go over the three types of NATs with you:
NAT Names
The names we use to describe the addresses used with NAT are fairly straightforward. Addresses used after NAT translations are called global addresses. These are usually the public addresses used on the Internet, which you don’t need if you aren’t going on the Internet.
Local addresses are the ones we use before NAT translation. This means that the inside local address is actually the private address of the sending host that’s attempting to get to the Internet. The outside local address would typically be the router interface connected to your ISP and is also usually a public address used as the packet begins its journey.
After translation, the inside local address is then called the inside global address and the outside global address then becomes the address of the destination host. Check out Table 13-2, which lists all this terminology and offers a clear picture of the various names used with NAT. Keep in mind that these terms and their definitions can vary somewhat based on implementation. The table shows how they’re used according to the Cisco exam objectives.
Table 13-2: NAT terms
| Names | Meaning |
| Inside local | Source host inside address before translation—typically an RFC 1918 address. |
| Outside local | Address from which source host is known on the Internet. This is usually the address of the router interface connected to ISP—the actual Internet address. |
| Inside global | Source host address used after translation to get onto the Internet. This is also the actual Internet address. |
| Outside global | Address of outside destination host and, again, the real Internet address. |
How NAT Works
Okay, it’s time to look at how this whole NAT thing works. I’m going to start by using Figure 13-2 to describe basic NAT translation.
In this figure, we can see host 10.1.1.1 sending an Internet-bound packet to the border router configured with NAT. The router identifies the source IP address as an inside local IP address destined for an outside network, translates the source IP address in the packet, and documents the translation in the NAT table.
The packet is sent to the outside interface with the new translated source address. The external host returns the packet to the destination host and the NAT router translates the inside global IP address back to the inside local IP address using the NAT table. This is as simple as it gets!
Let’s take a look at a more complex configuration using overloading, also referred to as PAT. I’ll use Figure 13-3 to demonstrate how PAT works by having an inside host HTTP to a server on the Internet.
Figure 13-2: Basic NAT translation
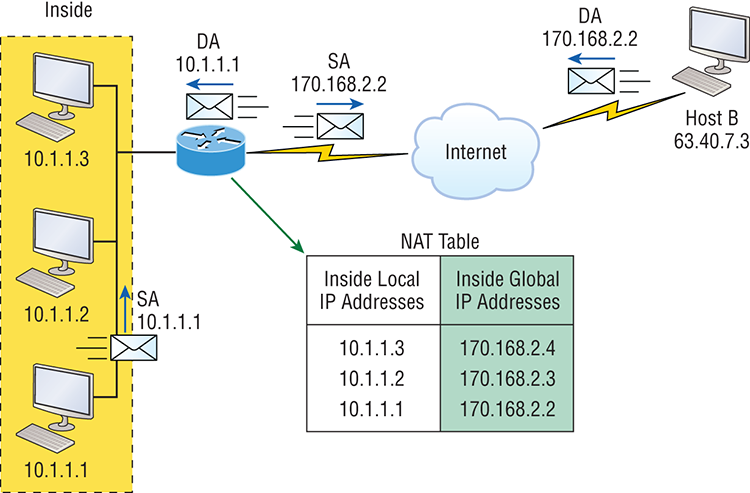
Figure 13-3: NAT overloading example (PAT)
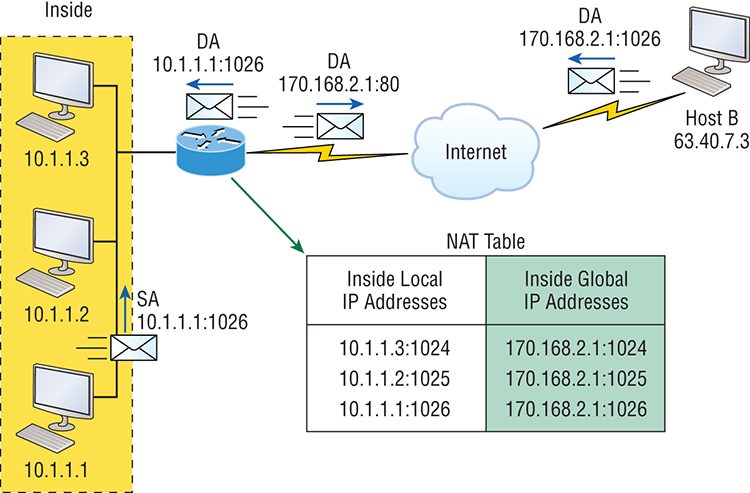
With PAT, all inside hosts get translated to one single IP address, hence the term overloading. Again, the reason we’ve just run out of available global IP addresses on the Internet is because of overloading (PAT).
Take a look at the NAT table in Figure 13-3 again. In addition to the inside local IP address and inside global IP address, we now have port numbers. These port numbers help the router identify which host should receive the return traffic. The router uses the source port number from each host to differentiate the traffic from each of them. Notice the packet has a destination port number of 80 when it leaves the router, and the HTTP server sends back the data with a destination port number of 1026, in this example. This allows the NAT translation router to differentiate between hosts in the NAT table and then translate the destination IP address back to the inside local address.
Port numbers are used at the Transport layer to identify the local host in this example. If we had to use real global IP addresses to identify the source hosts, that’s called static NAT and we would run out of addresses. PAT allows us to use the Transport layer to identify the hosts, which in turn allows us to theoretically use up to about 65,000 hosts with only one real IP address!
Static NAT Configuration
Let’s take a look at a simple example of a basic static NAT configuration:
ip nat inside source static 10.1.1.1 170.46.2.2
!
interface Ethernet0
ip address 10.1.1.10 255.255.255.0
ip nat inside
!
interface Serial0
ip address 170.46.2.1 255.255.255.0
ip nat outside
!In the preceding router output, the ip nat inside source command identifies which IP addresses will be translated. In this configuration example, the ip nat inside source command configures a static translation between the inside local IP address 10.1.1.1 to the outside global IP address 170.46.2.2.
Scrolling farther down in the configuration, we find an ip nat command under each interface. The ip nat inside command identifies that interface as the inside interface. The ip nat outside command identifies that interface as the outside interface. When you look back at the ip nat inside source command, you can see that the command is referencing the inside interface as the source or starting point of the translation. You could also use the command like this: ip nat outside source. This option indicates the interface that you designated as the outside interface should become the source or starting point for the translation.
Dynamic NAT Configuration
Basically, dynamic NAT really means we have a pool of addresses that we’ll use to provide real IP addresses to a group of users on the inside. Because we don’t use port numbers, we must have real IP addresses for every user who’s trying to get outside the local network simultaneously.
Here is a sample output of a dynamic NAT configuration:
ip nat pool todd 170.168.2.3 170.168.2.254
netmask 255.255.255.0
ip nat inside source list 1 pool todd
!
interface Ethernet0
ip address 10.1.1.10 255.255.255.0
ip nat inside
!
interface Serial0
ip address 170.168.2.1 255.255.255.0
ip nat outside
!
access-list 1 permit 10.1.1.0 0.0.0.255
!The ip nat inside source list 1 pool todd command tells the router to translate IP addresses that match access-list 1 to an address found in the IP NAT pool named todd. Here the ACL isn’t there to filter traffic for security reasons by permitting or denying traffic. In this case, it’s there to select or designate what we often call interesting traffic. When interesting traffic has been matched with the access list, it’s pulled into the NAT process to be translated. This is actually a common use for access lists, which aren’t always just stuck with the dull job of just blocking traffic at an interface!
The command ip nat pool todd 170.168.2.3 192.168.2.254 netmask 255.255.255.0 creates a pool of addresses that will be distributed to the specific hosts that require global addresses. When troubleshooting NAT for the Cisco objectives, always check this pool to confirm that there are enough addresses in it to provide translation for all the inside hosts. Last, check to make sure the pool names match exactly on both lines, remembering that they are case sensitive; if they don’t, the pool won’t work!
PAT (Overloading) Configuration
This last example shows how to configure inside global address overloading. This is the typical form of NAT that we would use today. It’s actually now rare to use static or dynamic NAT unless it is for something like statically mapping a server, for example.
Here is a sample output of a PAT configuration:
ip nat pool globalnet 170.168.2.1 170.168.2.1 netmask 255.255.255.0
ip nat inside source list 1 pool globalnet overload
!
interface Ethernet0/0
ip address 10.1.1.10 255.255.255.0
ip nat inside
!
interface Serial0/0
ip address 170.168.2.1 255.255.255.0
ip nat outside
!
access-list 1 permit 10.1.1.0 0.0.0.255The nice thing about PAT is that these are the only differences between this configuration and the previous dynamic NAT configuration:
- Our pool of addresses has shrunk to only one IP address.
- We included the overload keyword at the end of our ip nat inside source command.
A really key factor to see in the example is that the one IP address that’s in the pool for us to use is the IP address of the outside interface. This is perfect if you are configuring NAT Overload for yourself at home or for a small office that only has one IP address from your ISP. You could, however, use an additional address such as 170.168.2.2 if you had that address available to you as well, and doing that could prove very helpful in a very large implementation where you’ve got such an abundance of simultaneously active internal users that you need to have more than one overloaded IP address on the outside!
Simple Verification of NAT
Okay—as always, once you’ve chosen and configured the type of NAT you’re going to run, which is typically PAT, you must be able to verify your configuration.
To see basic IP address translation information, use the following command:
Router#show ip nat translationsWhen looking at the IP NAT translations, you may see many translations from the same host to the corresponding host at the destination. Understand that this is typical when there are many connections to the same server.
You can also verify your NAT configuration via the debug ip nat command. This output will show the sending address, the translation, and the destination address on each debug line:
Router#debug ip natBut wait—how do you clear your NAT entries from the translation table? Just use the clear ip nat translation command, and if you want to clear all entries from the NAT table, just use an asterisk (*) at the end of the command.
Testing and Troubleshooting NAT
Cisco’s NAT gives you some serious power—and it does so without much effort, because the configurations are really pretty simple. But we all know nothing’s perfect, so in case something goes wrong, you can figure out some of the more common culprits by running through this list of potential causes:
- Check the dynamic pools. Are they composed of the right scope of addresses?
- Check to see if any dynamic pools overlap.
- Check to see if the addresses used for static mapping and those in the dynamic pools overlap.
- Ensure that your access lists specify the correct addresses for translation.
- Make sure there aren’t any addresses left out that need to be there, and ensure that none are included that shouldn’t be.
- Check to make sure you’ve got both the inside and outside interfaces delimited properly.
A key thing to keep in mind is that one of the most common problems with a new NAT configuration often isn’t specific to NAT at all—it usually involves a routing blooper. So, because you’re changing a source or destination address in a packet, make sure your router still knows what to do with the new address after the translation!
The first command you should typically use is the show ip nattranslations command:
Router#show ip nat trans
Pro Inside global Inside local Outside local Outside global
--- 192.2.2.1 10.1.1.1 --- ---
--- 192.2.2.2 10.1.1.2 --- ---After checking out this output, can you tell me if the configuration on the router is static or dynamic NAT? The answer is yes, either static or dynamic NAT is configured because there’s a one-to-one translation from the inside local to the inside global. Basically, by looking at the output, you can’t tell if it’s static or dynamic per se; but you absolutely can tell that you’re not using PAT because there are no port numbers.
Let’s take a look at another output:
Router#sh ip nat trans
Pro Inside global Inside local Outside local Outside global
tcp 170.168.2.1:11003 10.1.1.1:11003 172.40.2.2:23 172.40.2.2:23
tcp 170.168.2.1:1067 10.1.1.1:1067 172.40.2.3:23 172.40.2.3:23Okay, you can easily see that the above output is using NAT Overload (PAT). The protocol in this output is TCP, and the inside global address is the same for both entries.
Supposedly the sky’s the limit regarding the number of mappings the NAT table can hold. But this is reality, so things like memory and CPU, or even the boundaries set in place by the scope of available addresses or ports, can cause limitations on the actual number of entries. Consider that each NAT mapping devours about 160 bytes of memory. And sometimes the amount of entries must be limited for the sake of performance or because of policy restrictions, but this doesn’t happen very often. In situations like these, just go to the ip nat translation max-entries command for help.
Another handy command for troubleshooting is show ip nat statistics. Deploying this gives you a summary of the NAT configuration, and it will count the number of active translation types too. Also counted are hits to an existing mapping as well any misses, with the latter causing an attempt to create a mapping. This command will also reveal expired translations. If you want to: check into dynamic pools, their types, the total available addresses, how many addresses have been allocated and how many have failed, plus the number of translations that have occurred, just use the pool keyword.
Here is an example of the basic NAT debugging command:
Router#debug ip nat
NAT: s=10.1.1.1->192.168.2.1, d=172.16.2.2 [0]
NAT: s=172.16.2.2, d=192.168.2.1->10.1.1.1 [0]
NAT: s=10.1.1.1->192.168.2.1, d=172.16.2.2 [1]
NAT: s=10.1.1.1->192.168.2.1, d=172.16.2.2 [2]
NAT: s=10.1.1.1->192.168.2.1, d=172.16.2.2 [3]
NAT*: s=172.16.2.2, d=192.168.2.1->10.1.1.1 [1]Notice the last line in the output and how the NAT at the beginning of the line has an asterisk (*). This means the packet was translated and fast-switched to the destination. What’s fast-switched? Well in brief, fast-switching has gone by several aliases such as cache-based switching and this nicely descriptive name, “route one switch many.” The fast-switching process is used on Cisco routers to create a cache of layer 3 routing information to be accessed at layer 2 so packets can be forwarded quickly through a router without the routing table having to be parsed for every packet. As packets are packet switched (looked up in the routing table), this information is stored in the cache for later use if needed for faster routing processing.
Okay, let’s get back to verifying NAT. Did you know you can manually clear dynamic NAT entries from the NAT table? You can, and doing this can come in seriously handy if you need to get rid of a specific rotten entry without sitting around waiting for the timeout to expire! A manual clear is also really useful when you want to clear the whole NAT table to reconfigure a pool of addresses.
You also need to know that the Cisco IOS software just won’t allow you to change or delete an address pool if any of that pool’s addresses are mapped in the NAT table. The clear ip nat translations command clears entries—you can indicate a single entry via the global and local address and through TCP and UDP translations, including ports, or you can just type in an asterisk (*) to wipe out the entire table. But know that if you do that, only dynamic entries will be cleared because this command won’t remove static entries.
Oh, and there’s more—any outside device’s packet destination address that happens to be responding to any inside device is known as the inside global (IG) address. This means that the initial mapping has to be held in the NAT table so that all packets arriving from a specific connection get translated consistently. Holding entries in the NAT table also cuts down on repeated translation operations happening each time the same inside machine sends packets to the same outside destinations on a regular basis.
Let me clarify: when an entry is placed into the NAT table the first time, a timer begins ticking and its duration is known as the translation timeout. Each time a packet for a given entry translates through the router, the timer gets reset. If the timer expires, the entry will be unceremoniously removed from the NAT table and the dynamically assigned address will then be returned to the pool. Cisco’s default translation timeout is 86,400 seconds (24 hours), but you can change that with the ip nat translation timeout command.
Before we move on to the configuration section and actually use the commands I just talked about, let’s go through a couple of NAT examples and see if you can figure out the best configuration to go with. To start, look at Figure 13-4 and ask yourself two things: Where would you implement NAT in this design? What type of NAT would you configure?
Figure 13-4: NAT example
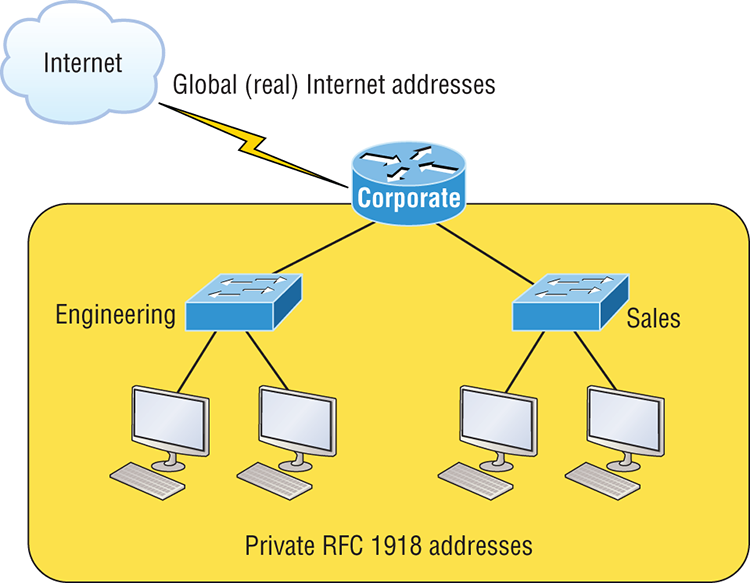
In Figure 13-4, the NAT configuration would be placed on the corporate router, just as I demonstrated with Figure 13-1, and the configuration would be dynamic NAT with overload (PAT). In this next NAT example, what type of NAT is being used?
ip nat pool todd-nat 170.168.10.10 170.168.10.20 netmask 255.255.255.0
ip nat inside source list 1 pool todd-natThe preceding command uses dynamic NAT without PAT. The pool in the command gives the answer away as dynamic, plus there’s more than one address in the pool and there is no overload command at the end of our ip nat inside source command. This means we are not using PAT!
In the next NAT example, refer to Figure 13-5 and see if you can come up with the configuration needed.
Figure 13-5: Another NAT example
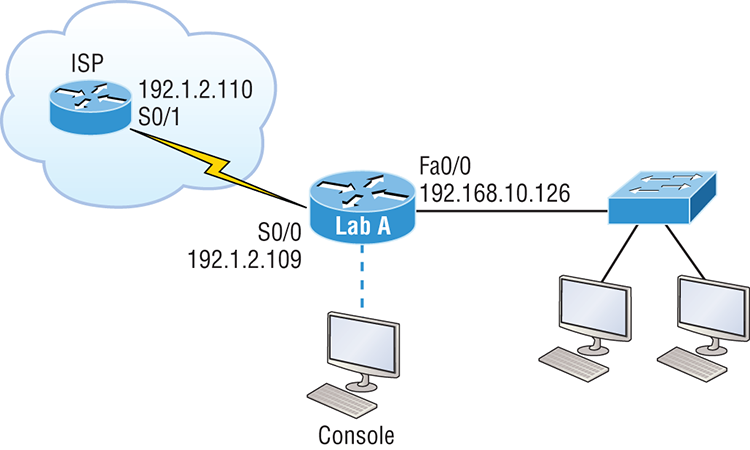
Figure 13-5 shows a border router that needs to be configured with NAT and allow the use of six public IP addresses to the inside locals, 192.1.2.109 through 192.1.2.114. However, on the inside network, you have 62 hosts that use the private addresses of 192.168.10.65 through 192.168.10.126. What would your NAT configuration be on the border router?
Actually, two different answers would both work here, but the following would be my first choice based on the exam objectives:
ip nat pool Todd 192.1.2.109 192.1.2.109 netmask 255.255.255.248
access-list 1 permit 192.168.10.64 0.0.0.63
ip nat inside source list 1 pool Todd overloadThe command ip nat pool Todd 192.1.2.109 192.1.2.109 netmask 255.255.255.248 sets the pool name as Todd and creates a dynamic pool of only one address using NAT address 192.1.2.109. Instead of the netmask command, you can use the prefix-length 29 statement. Just in case you’re wondering, you cannot do this on router interfaces as well!
The second answer would get you the exact same result of having only 192.1.2.109 as your inside global, but you can type this in and it will also work: ip nat pool Todd 192.1.2.109 192.1.2.114 netmask 255.255.255.248. But this option really is a waste because the second through sixth addresses would only be used if there was a conflict with a TCP port number. You would use something like what I’ve shown in this example if you literally had about ten thousand hosts with one Internet connection! You would need it to help with the TCP-Reset issue when two hosts are trying to use the same source port number and get a negative acknowledgment (NAK). But in our example, we’ve only got up to 62 hosts connecting to the Internet at the same time, so having more than one inside global gets us nothing!
If you’re fuzzy on the second line where the access list is set in the NAT configuration, do a quick review of Chapter 12, “Security.” But this isn’t difficult to grasp because it’s easy to see in this access-list line that it’s just the network number and wildcard used with that command. I always say, “Every question is a subnet question,” and this one is no exception. The inside locals in this example were 192.168.10.65–126, which is a block of 64, or a 255.255.255.192 mask. As I’ve said in pretty much every chapter, you really need to be able to subnet quickly!
The command ip nat inside source list 1 pool Todd overload sets the dynamic pool to use PAT by using the overload command.
And be sure to add the ip nat inside and ip nat outside statements on the appropriate interfaces.
Okay, one more example, and then you are off to the written lab, hands-on labs, and review questions.
The network in Figure 13-6 is already configured with IP addresses as shown in the figure, and there is only one configured host. However, you need to add 25 more hosts to the LAN. Now, all 26 hosts must be able to get to the Internet at the same time.
Figure 13-6: Last NAT example

By looking at the configured network, use only the following inside addresses to configure NAT on the Corp router to allow all hosts to reach the Internet:
- Inside globals: 198.18.41.129 through 198.18.41.134
- Inside locals: 192.168.76.65 through 192.168.76.94
This one is a bit more challenging because all we have to help us figure out the configuration is the inside globals and the inside locals. But even meagerly armed with these crumbs of information, plus the IP addresses of the router interfaces shown in the figure, we can still configure this correctly.
To do that, we must first determine what our block sizes are so we can get our subnet mask for our NAT pool. This will also equip us to configure the wildcard for the access list.
You should easily be able to see that the block size of the inside globals is 8 and the block size of the inside locals is 32. Know that it’s critical not to stumble on this foundational information!
Okay, so we can configure NAT now that we have our block sizes:
ip nat pool Corp 198.18.41.129 198.18.41.134 netmask 255.255.255.248
ip nat inside source list 1 pool Corp overload
access-list 1 permit 192.168.76.64 0.0.0.31Since we had a block of only 8 for our pool, we had to use the overload command to make sure all 26 hosts can get to the Internet at the same time.
There is one other simple way to configure NAT, and I use this command at my home office to connect to my ISP. One command line and it’s done! Here it is:
ip nat inside source list 1 int s0/0/0 overloadI can’t say enough how much I love efficiency, and being able to achieve something cool using one measly line always makes me happy! My one little powerfully elegant line essentially says, “Use my outside local as my inside global and overload it.” Nice! Of course, I still had to create ACL 1 and add the inside and outside interface commands to the configuration, but this is a really nice, fast way to configure NAT if you don’t have a pool of addresses to use.
Summary
Now this really was a fun chapter. Come on—admit it! You learned a lot about Network Address Translation (NAT) and how it’s configured as static and dynamic as well as with Port Address Translation (PAT), also called NAT Overload.
I also described how each flavor of NAT is used in a network as well as how each type is configured.
We finished up by going through some verification and troubleshooting commands. Now don’t forget to practice all the wonderfully helpful labs until you’ve got them nailed down tight!
Exam Essentials
Written Lab 13
The answers to this lab can be found in Appendix A, “Answers to Written Labs.”
In this section, write the answers to the following questions:
ip nat pool todd-nat 170.168.10.10 170.168.10.20 netmask 255.255.255.0Hands-on Labs
I am going to use some basic routers for these labs, but really, almost any Cisco router will work. Also, you can use the LammleSim IOS version to run through all the labs in this (and every) chapter in this book.
Here is a list of the labs in this chapter:
I am going to use the network shown in the following diagram for our hands-on labs. I highly recommend you connect up some routers and run through these labs. You will configure NAT on router Lab_A to translate the private IP address of 192.168.10.0 to a public address of 171.16.10.0.

Table 13-3 shows the commands we will use and the purpose of each command.
Table 13-3: Command summary for NAT/PAT hands-on labs
| Command | Purpose |
| ip nat inside source list acl pool name | Translates IPs that match the ACL to the pool |
| ip nat inside source static inside_addr outside_addr | Statically maps an inside local address to an outside global address |
| ip nat pool name | Creates an address pool |
| ip nat inside | Sets an interface to be an inside interface |
| ip nat outside | Sets an interface to be an outside interface |
| show ip nat translations | Shows current NAT translations |
Lab 13.1: Preparing for NAT
In this lab, you’ll set up your routers with IP addresses and RIP routing.
| Router | Interface | IP Address |
| ISP | S0 | 171.16.10.1/24 |
| Lab_A | S0/2 | 171.16.10.2/24 |
| Lab_A | S0/0 | 192.168.20.1/24 |
| Lab_B | S0 | 192.168.20.2/24 |
| Lab_B | E0 | 192.168.30.1/24 |
| Lab_C | E0 | 192.168.30.2/24 |
Lab_A#config t
Lab_A(config)#router rip
Lab_A(config-router)#network 192.168.20.0
Lab_A(config-router)#network 171.16.0.0
Lab_A(config-router)#passive-interface s0/2
Lab_A(config-router)#exit
Lab_A(config)#ip default-network 171.16.10.1Lab_B#config t
Lab_B(config)#router rip
Lab_B(config-router)#network 192.168.30.0
Lab_B(config-router)#network 192.168.20.0Lab_C#config t
Lab_C(config)#router rip
Lab_C(config-router)#network 192.168.30.0ISP#config t
ISP(config)#ip route 0.0.0.0 0.0.0.0 s0ISP#config t
ISP(config)#line vty 0 4
ISP(config-line)#no loginLab 13.2: Configuring Dynamic NAT
In this lab, you’ll configure dynamic NAT on the Lab_A router.
Lab_A(config)#ip nat pool GlobalNet 171.16.10.50 171.16.10.55
net 255.255.255.0Lab_A(config)#access-list 1 permit 192.168.20.0 0.0.0.255
Lab_A(config)#access-list 1 permit 192.168.30.0 0.0.0.255Lab_A(config)#ip nat inside source list 1 pool GlobalNetLab_A(config)#int s0/0
Lab_A(config-if)#ip nat insideLab_A(config-if)#int s0/2
Lab_A(config-if)#ip nat outsideLab_C#telnet 171.16.10.1Lab_B#telnet 171.16.10.1ISP#show usersISP>sh users
Line User Host(s) Idle Location
0 con 0 idle 00:03:32
2 vty 0 idle 00:01:33 171.16.10.50
* 3 vty 1 idle 00:00:09 171.16.10.51
Interface User Mode Idle Peer Address
ISP>Lab_A#sh ip nat translations
Pro Inside global Inside local Outside local Outside global
--- 171.16.10.50 192.168.30.2 --- ---
--- 171.16.10.51 192.168.20.2 --- ---
Lab_A#00:32:47: NAT*: s=192.168.30.2->171.16.10.50, d=171.16.10.1 [5]
00:32:47: NAT*: s=171.16.10.1, d=171.16.10.50->192.168.30.2Lab 13.3: Configuring PAT
In this lab, you’ll configure PAT on the Lab_A router. We will use PAT because we don’t want a one-to-one translation, which uses just one IP address for every user on the network.
Lab_A#clear ip nat translations *
Lab_A#config t
Lab_A(config)#no ip nat pool GlobalNet 171.16.10.50
171.16.10.55 netmask 255.255.255.0
Lab_A(config)#no ip nat inside source list 1 pool GlobalNetLab_A#config t
Lab_A(config)#ip nat pool Lammle 171.16.10.100 171.16.10.100
net 255.255.255.0Lab_A(config)#access-list 2 permit 192.168.20.0 0.0.0.255
Lab_A(config)#access-list 2 permit 192.168.30.0 0.0.0.255Lab_A(config)#ip nat inside source list 2 pool Lammle overloadISP>sh users
Line User Host(s) Idle Location
* 0 con 0 idle 00:00:00
2 vty 0 idle 00:00:39 171.16.10.100
4 vty 2 idle 00:00:37 171.16.10.100
Interface User Mode Idle Peer Address
ISP>Lab_A#sh ip nat translations
Pro Inside global Inside local Outside local Outside global
tcp 171.16.10.100:11001 192.168.20.2:11001 171.16.10.1:23 171.16.10.1:23
tcp 171.16.10.100:11002 192.168.30.2:11002 171.16.10.1:23 171.16.10.1:2301:12:36: NAT: s=192.168.30.2->171.16.10.100, d=171.16.10.1 [35]
01:12:36: NAT*: s=171.16.10.1, d=171.16.10.100->192.168.30.2 [35]
01:12:36: NAT*: s=192.168.30.2->171.16.10.100, d=171.16.10.1 [36]
01:12:36: NAT*: s=171.16.10.1, d=171.16.10.100->192.168.30.2 [36]
01:12:36: NAT*: s=192.168.30.2->171.16.10.100, d=171.16.10.1 [37]
01:12:36: NAT*: s=171.16.10.1, d=171.16.10.100->192.168.30.2 [37]
01:12:36: NAT*: s=192.168.30.2->171.16.10.100, d=171.16.10.1 [38]
01:12:36: NAT*: s=171.16.10.1, d=171.16.10.100->192.168.30.2 [38]
01:12:37: NAT*: s=192.168.30.2->171.16.10.100, d=171.16.10.1 [39]
01:12:37: NAT*: s=171.16.10.1, d=171.16.10.100->192.168.30.2 [39]Review Questions
The answers to these questions can be found in Appendix B, “Answers to Chapter Review Questions.”
1. Which of the following are disadvantages of using NAT? (Choose three.)
A. Translation introduces switching path delays.
B. NAT conserves legally registered addresses.
C. NAT causes loss of end-to-end IP traceability.
D. NAT increases flexibility when connecting to the Internet.
E. Certain applications will not function with NAT enabled.
F. NAT reduces address overlap occurrence.
2. Which of the following are advantages of using NAT? (Choose three.)
A. Translation introduces switching path delays.
B. NAT conserves legally registered addresses.
C. NAT causes loss of end-to-end IP traceability.
D. NAT increases flexibility when connecting to the Internet.
E. Certain applications will not function with NAT enabled.
F. NAT remedies address overlap occurrence.
3. Which command will allow you to see real-time translations on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
4. Which command will show you all the translations active on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
5. Which command will clear all the translations active on your router?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
6. Which command will show you the summary of the NAT configuration?
A. show ip nat translations
B. show ip nat statistics
C. debug ip nat
D. clear ip nat translations *
7. Which command will create a dynamic pool named Todd that will provide you with 30 global addresses?
A. ip nat pool Todd 171.16.10.65 171.16.10.94 net 255.255.255.240
B. ip nat pool Todd 171.16.10.65 171.16.10.94 net 255.255.255.224
C. ip nat pool Todd 171.16.10.65 171.16.10.94 net 255.255.255.224
D. ip nat pool Todd 171.16.10.1 171.16.10.254 net 255.255.255.0
8. Which of the following are methods of NAT? (Choose three.)
A. Static
B. IP NAT pool
C. Dynamic
D. NAT double-translation
E. Overload
9. When creating a pool of global addresses, which of the following can be used instead of the netmask command?
A. / (slash notation)
B. prefix-length
C. no mask
D. block-size
10. Which of the following would be a good starting point for troubleshooting if your router is not translating?
A. Reboot
B. Call Cisco
C. Check your interfaces for the correct configuration
D. Run the debug all command
11. Which of the following would be good reasons to run NAT? (Choose three.)
A. You need to connect to the Internet and your hosts don’t have globally unique IP addresses.
B. You change to a new ISP that requires you to renumber your network.
C. You don’t want any hosts connecting to the Internet.
D. You require two intranets with duplicate addresses to merge.
12. Which of the following is considered to be the inside host’s address after translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
13. Which of the following is considered to be the inside host’s address before translation?
A. Inside local
B. Outside local
C. Inside global
D. Outside global
14. By looking at the following output, which of the following commands would allow dynamic translations?
Router#show ip nat trans
Pro Inside global Inside local Outside local Outside global
--- 1.1.128.1 10.1.1.1 --- ---
--- 1.1.130.178 10.1.1.2 --- ---
--- 1.1.129.174 10.1.1.10 --- ---
--- 1.1.130.101 10.1.1.89 --- ---
--- 1.1.134.169 10.1.1.100 --- ---
--- 1.1.135.174 10.1.1.200 --- ---A. ip nat inside source pool todd 1.1.128.1 1.1.135.254 prefix-length 19
B. ip nat pool todd 1.1.128.1 1.1.135.254 prefix-length 19
C. ip nat pool todd 1.1.128.1 1.1.135.254 prefix-length 18
D. ip nat pool todd 1.1.128.1 1.1.135.254 prefix-length 21
15. Your inside locals are not being translated to the inside global addresses. Which of the following commands will show you if your inside globals are allowed to use the NAT pool?
ip nat pool Corp 198.18.41.129 198.18.41.134 netmask 255.255.255.248
ip nat inside source list 100 int pool Corp overloadA. debug ip nat
B. show access-list
C. show ip nat translation
D. show ip nat statistics
16. Which command would you place on the interface of a private network?
A. ip nat inside
B. ip nat outside
C. ip outside global
D. ip inside local
17. Which command would you place on an interface connected to the Internet?
A. ip nat inside
B. ip nat outside
C. ip outside global
D. ip inside local
18. Port Address Translation is also called what?
A. NAT Fast
B. NAT Static
C. NAT Overload
D. Overloading Static
19. What does the asterisk (*) represent in the following output?
NAT*: s=172.16.2.2, d=192.168.2.1->10.1.1.1 [1]A. The packet was destined for a local interface on the router.
B. The packet was translated and fast-switched to the destination.
C. The packet attempted to be translated but failed.
D. The packet was translated but there was no response from the remote host.
20. Which of the following needs to be added to the configuration to enable PAT?
ip nat pool Corp 198.18.41.129 198.18.41.134 netmask 255.255.255.248
access-list 1 permit 192.168.76.64 0.0.0.31A. ip nat pool inside overload
B. ip nat inside source list 1 pool Corp overload
C. ip nat pool outside overload
D. ip nat pool Corp 198.41.129 net 255.255.255.0 overload