Chapter 3. Telecommunications and Network Security
This chapter covers the following topics:
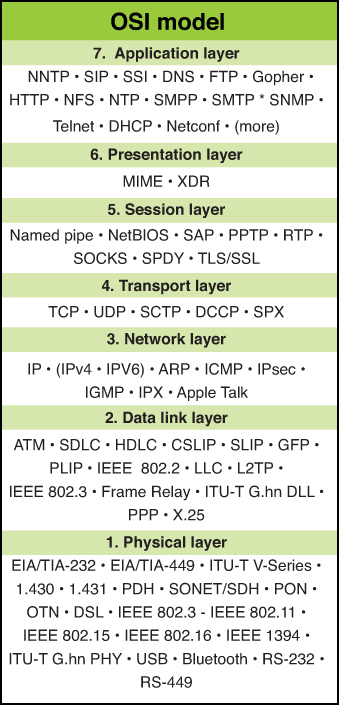
• OSI model: An explanation of the functions of the seven layers of the OSI model
• TCP/IP model: A discussion of the TCP/IP model and its relationship to the OSI model
• Common TCP/UDP ports: A description of the function of port numbers and common standard ports
• IP addressing: A look at both logical and physical addressing systems and their interrelationship in routing and switching
• Network transmission: An examination of the processes used to transfer data across various media types
• Cabling: Types of bounded media, their characteristics, and proper use
• Network topologies: A survey of both logical and physical network topologies
• Network technologies: A discussion of the various technologies used to accomplish networking
• Network protocols/services: The functions of the major network protocols and services that provide network functionality
• Network routing: An explanation of how static and dynamic routing works and a discussion of the major interior and exterior routing protocols
• Network devices: Covers the function and placement of major network devices
• Network types: An explanation of local area network types including MAN, WAN, LAN, extranet, and intranet
• WAN technologies: A discussion of the various methods of connecting local area networks with wide area networks
• Remote connection technologies: A description of the methods of connecting remote users and networks to the LAN and the Internet
• Wireless networks: Covers the types of wireless networks and the processes required to secure them
• Network threats: An introduction to the various security threats facing networks
Sensitive data must be protected from unauthorized access when the data is at rest (on a hard drive) and in transit (moving through a network). Moreover, sensitive communications of other types such as emails, instant messages, and phone conversations must also be protected from prying eyes and ears. Many communication processes send information in a form that can be read and understood if captured with a protocol analyzer or sniffer.
In today’s communication world, assume that your communications are being captured regardless of how unlikely you think that might be. You should also take steps to protect or encrypt the transmissions so they will be useless to anyone capturing them. This chapter covers the protection of wired and wireless transmissions and of the network devices that perform the transmissions, as well as some networking fundamentals required to understand transmission security.
Foundation Topics
OSI Model
A complete understanding of networking requires an understanding of the Open Systems Interconnect (OSI) model. Created in the 1980s by the International Standards Organization (ISO) as a part of its mission to create a protocol set to be used as a standard for all vendors, it breaks the communication process into layers. Although the ensuing protocol set did not catch on as a standard (TCP/IP was adopted), the model has guided the development of technology since its creation. It also has helped generations of students understand the network communication process between two systems.
The OSI model breaks up the process into seven layers or modules. The benefits of doing this are
• It breaks up the communication process into layers with standardized interfaces between the layers, allowing for changes and improvements on one layer without necessitating changes on other layers.
• It provides a common framework for hardware and software developers, fostering interoperability.
The goal of this open systems architecture is that no vendor owns it and it acts as a blueprint or model for developers to work with. Various protocols operate at different layers of this model. A protocol is a set of communication rules two systems must both use and understand to communicate. Some protocols depend on other protocols for services, and as such these protocols work as a team to get transmissions done, much like the team at the post office that gets your letters delivered. Some people sort, others deliver, and still others track lost shipments.
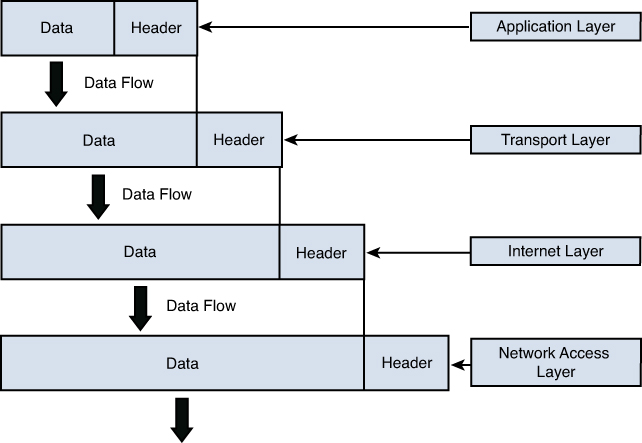
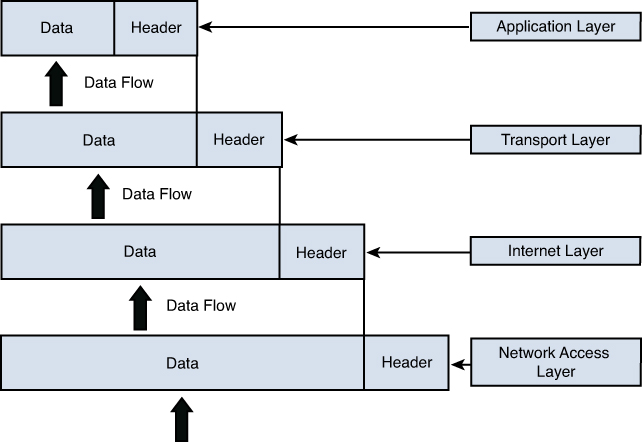
The OSI model and the TCP/IP model, explained in the next section, are often both used to describe the process called packet creation or encapsulation. Until a packet is created to hold the data, it cannot be sent on the transmission medium.
With a modular approach it becomes possible for a change in a protocol or the addition of a new protocol to be accomplished without having to rewrite the entire protocol stack (a term for all the protocols that work together at all layers). The model has seven layers. This section discusses each layer’s function and its relationship to the layer above and below it in the model. The layers are often referred to by their number with the numbering starting at the bottom of the model at layer 1, the Physical layer.
The process of creating a packet or encapsulation begins at layer 7, the Application layer rather than layer 1, so we discuss the process starting at layer 7 and work down the model to layer 1, the Physical layer, where the packet is sent out on the transmission medium.
Application Layer
The Application layer (layer 7) is where the encapsulation process begins. This layer receives the raw data from the application in use and provides services, such as file transfer and message exchange to the application (and thus the user). An example of a protocol that operates at this layer is Hypertext Transfer Protocol (HTTP), which is used to transfer web pages across the network. Other examples of protocols that operate at this layer are DNS queries, FTP transfers, and SMTP email transfers.
The user application interfaces with these application protocols through a standard interface called an Application Programming Interface (API). The Application layer protocol receives the raw data and places it in a container called a protocol data unit (PDU). When the process gets down to layer 4 these PDUs have standard names, but at layers 5–7 we simply refer to the PDU as “data.”
Presentation Layer
The information that is developed at layer 7 is then handed to layer 6, the Presentation layer. Each layer makes no changes to the data received from the layer above it. It simply adds information to the developing packet. In the case of the Presentation layer, information is added that standardizes the formatting of the information if required.
Layer 6 is responsible for the manner in which the data from the Application layer is represented (or presented) to the Application layer on the destination device (explained more fully in the section “Encapsulation.” If any translation between formats is required it will take care of it. It also communicates the type of data within the packet and the application that might be required to read it on the destination device.
Session Layer
The Session layer or layer 5 is responsible for adding information to the packet that makes a communication session between a service or application on the source device possible with the same service or application on the destination device. Do not confuse this process with the one that establishes a session between the two physical devices. That occurs not at this layer but at layers 3 and 4. This session is built and closed after the physical session between the computers has taken place.
The application or service in use is communicated between the two systems with an identifier called a port number. This information is passed on to the Transport layer, which also makes use of these port numbers.
Transport Layer
The protocols that operate at the Transport layer (layer 4) work to establish a session between the two physical systems. The service provided can be either connection oriented or connectionless, depending on the transport protocol in use. The “TCP/IP Model” section (TCP/IP being the most common standard networking protocol in use) discusses the specific transport protocols used by TCP/IP in detail.
The Transport layer receives all the information from layers 7, 6, and 5 and adds information that identifies the transport protocol in use and the specific port number that identifies the required layer 7 protocol. At this layer the PDU is called a segment because this layer takes a large transmission and segments it into smaller pieces for more efficient transmission on the medium.
Network Layer
At layer 3 or the Network layer, information required to route the packet is added. This is in the form of a source and destination logical address (meaning one that is assigned to a device in some manner and can be changed). In TCP/IP this is in terms of a source and destination IP address. An IP address is a number that uniquely differentiates a host from all other devices on the network. It is based on a numbering system that makes it possible for computers (and routers) to identify whether the destination device is on the local network or on a remote network Any time a packet needs to be sent to a different network or subnet (IP addressing is covered later in the chapter), it must be routed and the information required to do that is added here. At this layer the PDU is called a packet.
Data Link Layer
The Data Link layer is responsible for determining the destination physical address. Network devices have logical addresses (IP addresses) and the network interfaces they possess have a physical address (MAC address), which is permanent in nature. When the transmission is handed off from routing device to routing device, at each stop this source and destination address pair changes, whereas the source and destination logical addresses (in most cases IP addresses) do not. This layer is responsible for determining what those MAC addresses should be at each hop (router interface) and adding them to this part of the packet. The later section “TCP/IP Model” covers how this resolution is performed in TCP/IP. After this is done, we call the PDU a frame.
Something else happens at this layer that is unique to this layer. Not only is a layer 2 header placed on the packet but also a trailer at the “end” of the frame. Information contained in the trailer is used to verify that none of the data contained has been altered or damaged en route.
Physical Layer
Finally, the packet (or frame as it is called at layer 2 is received by the Physical layer (layer 1). Layer 1 is responsible for turning the information into bits (ones and zeros) and sending it out on the medium. The way in which this is accomplished can vary according to the media in use. For example, in a wired network, the ones and zeros are represented as electrical charges. In wireless, they are represented by altering the radio waves. In an optical network they are represented with light.
The ability of the same packet to be routed through various media types is a good example of the independence of the layers. As a PDU travels through different media types, the physical layer will change but all the information in layers 2–7 will not. Similarly, when a frame crosses routers or hops, the MAC addresses change but none of the information in layers 3–7 changes. The upper layers depend on the lower layers for various services but the lower layers leave the upper layer information unchanged.
Figure 3-1 shows common protocols mapped to the OSI model.

The next section covers another model that perhaps more accurately depicts what happens in a TCP/IP network. Because TCP/IP is the standard now for transmission comparing these two models is useful. Although they have a different number of layers and some of the layer names are different, they describe the same process of packet creation or encapsulation.
Multi-Layer Protocols
Many protocols, such as FTP and DNS, operate on a single layer of the OSI model. However, many protocols operate at multiple layers of the OSI model. The best example is TCP/IP, the networking protocol used on the Internet and on the vast majority of LANs. In fact, this protocol has its own model that describes the layers on which it operates and the parts of the protocol that operate on each layer. The next section covers this model and the protocol it was designed to describe.
TCP/IP Model
The protocols developed when the OSI model was developed (sometimes referred to as OSI protocols) did not become the standard for the Internet. The Internet as we know it today has its roots in a wide area network developed by the Department of Defense with TCP/IP being the protocol developed for that network. The Internet is a global network of public networks and Internet Service Providers (ISPs) throughout the world.
Although the OSI model is still often referenced, of the protocols themselves only X.400, X.500, and IS-IS have had much lasting impact. For that reason a second model exists based on TCP/IP. In a discussion of this model, the protocols that are part of what is called the TCP/IP suite can be mapped to the layer on which they perform their function.
This model bears many similarities to the OSI model, which is not unexpected because they both describe the process of packet creation or encapsulation. The difference is that the OSI model breaks the process into seven layers, whereas the TCP/IP model breaks it into four. If you examine them side by side, however, it becomes apparent that many of the same functions occur at the same layers, while the TCP/IP model combines the top three layers of the OSI model into one and the bottom two layers of the OSI model into one. Figure 3-2 show the two models next to one another.

Figure 3-2. TCP/IP and OSI Models

The TCP/IP model has only four layers and is useful to study because it focuses its attention on TCP/IP. This section explores those four layers and their functions and relationships to one another and to layers in the OSI model.
Application Layer
Although the Application layer in the TCP/IP model has the same name as the top layer in the OSI model, the Application layer in the TCP/IP model encompasses all the functions performed in layers 5–7 in the OSI model. Not all functions map perfectly because both are simply conceptual models. Within the Application layer, applications create user data and communicate this data to other processes or applications on another host. For this reason, it is sometimes also referred to as the process-to-process layer.
Examples of protocols that operate at this layer are SMTP, FTP, SSH, and HTTP. These protocols are discussed in the section “Network Protocols/Services” later in this chapter. In general, however, these are usually referred to as higher layer protocols that perform some specific function, whereas protocols in the TCP/IP suite that operate at the Transport and Internet layers perform location and delivery service on behalf of these higher layer protocols.
A port number identifies to the receiving device these upper layer protocols and the programs on whose behalf they function. The number identifies the protocol or service. Many port numbers have been standardized. For example, DNS is identified with the standard port number of 53. The “Common TCP/UDP Ports” section covers these port numbers in more detail.
Transport Layer
The Transport layers of the OSI model and the TCP/IP model perform the same function, which is to open and maintain a connection between hosts. This must occur before the session between the processes can occur as described in the Application layer section and can be done in TCP/IP in two ways: connectionless and connection-oriented. A connection-oriented transmission means that a connection will be established before any data is transferred, whereas in a connectionless transmission this is not done. One of two different transport layer protocols is used for each process. If a connection-oriented transport protocol is required, Transmission Control Protocol (TCP) will be used. If the process will be connectionless, User Datagram Protocol (UDP) is used.
Application developers can choose to use either TCP or UDP as the Transport layer protocol used with the application. Regardless of which transport protocol is used, the application or service will be identified to the receiving device by its port number and the transport protocol (UDP or TCP). Port numbers are discussed in more detail in the section “Common TCP/UDP Ports” later in this chapter.
Although TCP provides more functionality and reliability, the overhead required by this protocol is substantial when compared to UDP. This means that a much higher percentage of the packet consists of the header when using TCP than when using UDP. This is necessary to provide the fields required to hold the information needed to provide the additional services. Figure 3-3 shows a comparison of the size of the two respective headers.
Figure 3-3. TCP/IP and UDP Headers

When an application is written to use TCP, a state of connection is established between the two hosts before any data is transferred. This occurs using a process known as the TCP three-way handshake. This process is followed exactly, and no data is transferred until it is complete. Figure 3-4 shows the steps in this process. The steps are as follows:
1. The initiating computer sends a packet with the SYN flag set (one of the fields in the TCP header), which indicates a desire to create a connection.
2. The receiving host acknowledges receiving this packet and indicates a willingness to create a state of connection by sending back a packet with both the SYN and ACK flags set.
3. The first host acknowledges completion of the connection process by sending a final packet back with only the ACK flag set.

Figure 3-4. TCP Three-Way Handshake

So what exactly is gained by using the extra overhead to use TCP? The following are examples of the functionality provided with TCP:
• Guaranteed delivery: If the receiving host does not specifically acknowledge receipt of each packet, the sending system will resend the packet.
• Sequencing: In today’s routed networks, the packets might take many different routes to arrive and might not arrive in the order in which they were sent. A sequence number added to each packet allows the receiving host to reassemble the entire transmission using these numbers.
• Flow control: The receiving host has the capability of sending the acknowledgement packets back to signal the sender to slow the transmission if it cannot process the packets as fast as they are arriving.
Many applications do not require the services provided by TCP or cannot tolerate the overhead required by TCP. In these cases the process will use UDP, which sends on a “best effort” basis with no guarantee of delivery. In many cases some of these functions are provided by the Application layer protocol itself rather than relying on the Transport layer protocol.
Internet Layer
The Transport layer can neither create a state of connection nor send using UDP until the location and route to the destination are determined, which occurs on the Internet layer. The four protocols in the TCP/IP suite that operate at this layer are
• Internet Protocol (IP): Responsible for putting the source and destination IP addresses in the packet and for routing the packet to its destination.
• Internet Control Message Protocol (ICMP): Used by the network devices to send messages regarding the success or failure of communications and used by humans for troubleshooting. When you use the PING or TRACEROUTE commands, you are using ICMP.
• Internet Group Management Protocol (IGMP): Used when multicasting, which is a form of communication whereby one host sends to a group of destination hosts rather than a single host (called a unicast transmission) or to all hosts (called a broadcast transmission).
• Address Resolution Protocol (ARP): Resolves the IP address placed in the packet to a physical or layer 2 address (called a MAC address in Ethernet).
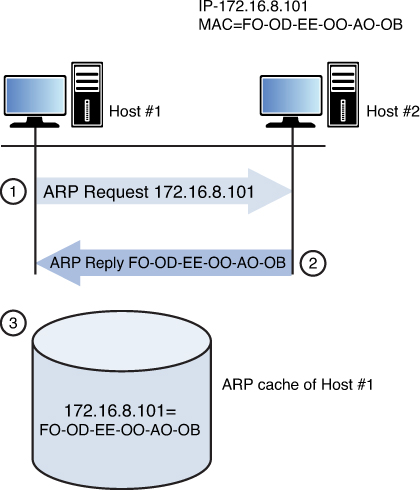
The relationship between IP and ARP is worthy of more discussion. IP places the source and destination IP addresses in the header of the packet. As we saw earlier, when a packet is being routed across a network the source and destination IP addresses never change but the layer 2 or MAC address pairs change at every router hop. ARP uses a process called the ARP broadcast to learn the MAC address of the interface that matches the IP address of the next hop. After it has done this, a new layer 2 header is created. Again, nothing else in the upper layer changes in this process, just layer 2.
That brings up a good point concerning the mapping of ARP to the TCP/IP model. Although we generally place ARP on the Internet layer, the information it derives from this process is placed in the Link layer or layer 2, the next layer in our discussion.
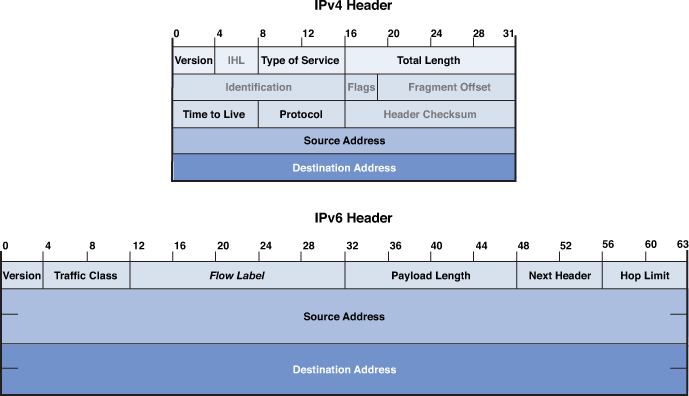
Just as the Transport layer added a header to the packet, so does the Internet layer. One of the improvements made by IPv6 is the streamlining of the IP header. Although the same information is contained in the header and the header is larger, it has a much simpler structure. Figure 3-5 shows a comparison of the two.
Figure 3-5. IPv6 and IPv4 Header
Link Layer
The Link layer of the TCP/IP model provides the services provided by both the Data Link and the Physical layers in the OSI model. The source and destination MAC addresses are placed in this layer’s header. A trailer is also placed on the packet at this layer with information in the trailer that can be used to verify the integrity of the data.
This layer is also concerned with placing the bits on the medium, as discussed in the section on the OSI model earlier in this chapter Again the exact method of implementation varies with the physical transmission medium. It might be in terms of electrical impulses, light waves, or radio waves.
Encapsulation
In either model as the packet is created, information is added to the header at each layer and then a trailer is placed on the packet before transmission. This process is called encapsulation. Intermediate devices, such as routers and switches, only read the layers of concern to that device (for a switch layer 2 and for a router layer 3). The ultimate receiver strips off the entire header with each layer, making use of the information placed in the header by the corresponding layer on the sending device. This process is called de-encapsulation. Figure 3-6 shows a visual representation of this process.

Figure 3-6. Encapsulation and De-encapsulation
Common TCP/UDP Ports
When the Transport layer learns the required port number for the service or application required on the destination device from the Application layer, it is recorded in the header as either a TCP or UDP port number. Both UDP and TCP use 16 bits in the header to identify these ports. These port numbers are software based or logical, and there are 65,535 possible numbers. Port numbers are assigned in various ways, based on three ranges:
• System or well-known ports (0–1023)
• User Ports (1024–49151)
• Dynamic and/or Private Ports (49152–65535)
System Ports are assigned by the Internet Engineering Task Force (IETF) for standards-track protocols, as per [RFC6335]. User ports can be registered with the Internet Assigned Numbers Authority (IANA) and assigned to the service or application using the “Expert Review” process, as per [RFC6335]. Dynamic ports are used by source devices as source ports when accessing a service or application on another machine. For example, if computer A is sending an FTP packet, the destination port will be the well-known port for FTP and the source will be selected by the computer randomly from the dynamic range.
The combination of the destination IP address and the destination port number is called a socket. The relationship between these two values can be understood if viewed through the analogy of an office address. The office has a street address but the address also must contain a suite number as there could be thousands (in this case 65,535) suites in the building. Both are required to get the information where it should go.
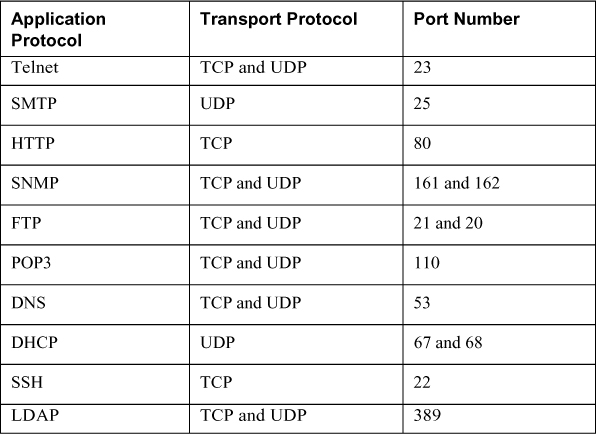
As a security professional you should be aware of well-known port numbers of common services. In many instances firewall rules and access control lists (ACLs) are written or configured in terms of the port number of what is being allowed or denied rather than the name of the service or application. Table 3-1 lists some of the more important port numbers. Some use more than one port.

Table 3-1. Common TCP/UDP Port Numbers
Logical and Physical Addressing
During the process of encapsulation at layer 3 of the OSI model, IP places source and destination IP addresses in the packet. Then at layer 2, the matching source and destination MAC addresses that have been determined by ARP are placed in the packet. IP addresses are examples of logical addressing, and MAC addresses are examples of physical addressing. IP addresses are considered logical because these addresses are administered by humans and can be changed at any time. MAC addresses on the other hand are assigned permanently to the interface cards of the devices when the interfaces are manufactured. It is important to note, however, that although these addresses are permanent they can be spoofed. When this is done, however, the hacker is not actually changing the physical address, but rather telling the interface to place a different MAC address in the layer 2 headers.
This section discusses both address types with a particular focus on how IP addresses are used to create separate networks or subnets in the larger network. It also discusses how IP addresses and MAC addresses are related and used during a network transmission.
IPv4
IPv4 addresses are 32 bits in length and can be represented in either binary or in dotted-decimal format. The number of possible IP addresses using 32 bits can be calculated by raising the number 2 (the number of possible values in the binary number system) to the 32nd power. The result is 4,294,967,296, which on the surface appears to be enough IP addresses. But with the explosion of the Internet and the increasing number of devices that require an IP address, this number has proven to be insufficient.
Due to the eventual exhaustion of the IPv4 address space, several methods of preserving public IP addresses (more on that in a bit, but for now these are addresses that are legal to use on the Internet) have been implemented, including the use of private addresses and Network Address Translation (NAT), both discussed in the following sections. The ultimate solution lies in the adoption of IPv6, a new system that uses 128 bits and allows for enough IP addresses for each man, woman, and child on the planet to have as many IP addresses as the entire IPv4 numbering space. IPv6 is discussed later in this section.
IP addresses that are written in dotted-decimal format, the format in which humans usually work with them, have four fields called octets separated by dots or periods. Each field is called an octet because when we look at the addresses in binary format, we devote 8 bits in binary to represent each decimal number that appears in the octet when viewed in dotted-decimal format. Therefore, if we look at the address 216.5.41.3, four decimal numbers are separated by dots, where each would be represented by 8 bits if viewed in binary. The following is the binary version of this same address:
11011000.00000101.00101001.00000011
There are 32 bits in the address, 8 in each octet.
The structure of IPv4 addressing lends itself to dividing the network into subdivisions called subnets. Each IP address also has a required companion value called a subnet mask. The subnet mask is used to specify which part of the address is the network part and which part is the host. The network part, on the left side of the address determines on which network the device resides whereas the host portion on the right identifies the device on that network. Figure 3-7 shows the network and host portion of the three default classes of IP address.
Figure 3-7. Network and Host Bits

When the IPv4 system was first created, there were only three default subnet masks. This yielded only three sizes of networks, which later proved to be inconvenient and wasteful of public IP addresses. Eventually a system called Classless Interdomain Routing (CIDR) was adopted that uses subnet masks that allows you to make subnets or subdivisions out of the major classful networks possible before CIDR. CIDR is beyond the scope of the exam but it is worth knowing about. You can find more information about how CIDR works at http://searchnetworking.techtarget.com/definition/CIDR.
IP Classes
Classful subnetting (pre-CIDR) created five classes of networks. Each class represented a range of IP addresses. Table 3-2 shows the five classes. Only the first three (A, B, and C) are used for individual network devices. The other ranges are for special use.

Table 3-2. Classful Addressing

As you can see, the key value that changes as you move from one class to another is the value of the first octet (the one on the far left). What might not be immediately obvious is that as you move from one class to another, the dividing line between the host portion and network portion also changes. This is where the subnet mask value comes in. When the mask is overlaid with the IP addresses (thus we call it a mask) every octet in the subnet mask where there is a 255 is a network portion and every octet where there is a 0 is a host portion. Another item to mention is that each class has a distinctive pattern in the first two bits of the first octet. For example, ANY IP address that begins with 01 in the first bit positions MUST be in Class A, also indicated in Table 3-2.
The significance of the network portion is that two devices must share the same values in the network portion to be in the same network. If they do not, they will not be able to communicate.
Public versus Private IP Addresses
The initial solution used (and still in use) to address the exhaustion of the IPv4 space involved the use of private addresses and Network Address Translation (NAT). Three ranges of IP addresses were set aside to be used ONLY within private networks and are NOT routable on the Internet. RFC 1918 set aside the IP address ranges in Table 3-3 to be used for this purpose. Because these addresses are not routable on the public network, they must be translated to public addresses before being sent to the Internet. This process, called Network Address Translation (NAT) is discussed in the next section.


NAT
Network Address Translation (NAT) is a service that can be supplied by a router or by a server. The device that provides the service stands between the LAN and the Internet. When packets need to go to the Internet, the packets go through the NAT service first. The NAT service changes the private IP address to a public address that is routable on the Internet. When the response is returned from the Web, the NAT service receives it, translates the address back to the original private IP address, and sends it back to the originator.
This translation can be done on a one-to-one basis (one private address to one public address), but to save IP addresses, usually the NAT service will represent the entire private network with a single public IP address. This process is called Port Address Translation (PAT). This name comes from the fact that the NAT service keeps the private clients separate from one another by recording their private address and the source port number (usually a unique number) selected when the packets were built.
Allowing NAT to represent an entire network (perhaps thousands of computers) with a single public address has been quite effective in saving public IP addresses. However, many applications do not function properly through NAT, and thus it has never been seen as a permanent solution to resolving the lack of IP addresses. That solution is IPv6.
IPv4 Versus IPv6
IPv6 was developed to more cleanly address the issue of the exhaustion of the IPv4 space. Although private addressing and the use of NAT have helped to delay the inevitable, the use of NAT introduces its own set of problems. The IPv6 system uses 128 bits so it creates such a large number of possible addresses that it is expected to suffice for many, many years.
The details of IPv6 are beyond the scope of the exam but these addresses look different than IPv4 addresses because they use a different format and use the hexadecimal number system, so there are letters and numbers in them such as you would see in a MAC address (discussed in the next section). There are eight fields separated by colons, not dots. Here is an example address:
2001:00000:4137:9e76:30ab:3035:b541:9693
Many of the security features that were add-ons to IPv4 (such as IPsec) have been built into IPv6, increasing its security. Moreover, while DHCP can be used with IPv6, IPv6 provides a host the ability to locate its local router, configure itself, and discover the IP addresses of its neighbors. Finally, broadcast traffic is completely eliminated in IPv6 and replaced by multicast communications.
MAC Addressing
All the discussion about addressing thus far has been addressing that is applied at layer 3, which is IP addressing. At layer 2 physical addresses reside. In Ethernet these are called Media Access Control (MAC) addresses. They are called physical addresses because these 48-bit addresses expressed in hexadecimal are permanently assigned to the network interfaces of devices. Here is an example of a MAC address:
01:23:45:67:89:ab
As a packet is transferred across a network, at every router hop and then again when it arrives at the destination network, the source and destination MAC addresses change. ARP resolves the next hop address to a MAC address using a process called the ARP broadcast. MAC addresses are unique. This comes from the fact that each manufacturer has a different set of values assigned to it at the beginning of the address called the Organizationally Unique Identifier (OUI). Each manufacturer ensures that it assigns no duplicate within its OUI. The OUI is the first three bytes of the MAC address.
Network Transmission
Data can be communicated across a variety of media types, using several possible processes. These communications can also have a number of characteristics that need to be understood. This section discusses some of the most common methods and their characteristics.
Analog versus Digital
Data can be represented in various ways on a medium. On a wired medium, the data can be transmitted in either analog or digital format. Analog represents the data as sound and is used in analog telephony. Analog signals differ from digital in that there are an infinite possible number of values. If we look at an analog signal on a graph, it looks like a wave going up and down. Figure 3-8 shows an analog waveform compared to a digital one.
Figure 3-8. Digital and Analog Signals

Digital signaling on the other hand, which is the type used in most computer transmissions, does not have an infinite number of possible values, but only two: on and off. A digital signal shown on a graph exhibits a sawtooth pattern as shown in Figure 3-8. Digital signals are usually preferable to analog because they are more reliable and less susceptible to noise on the line. Transporting more information on the same line at a higher quality over a longer distance than with analog is also possible.
Asynchronous versus Synchronous
When two systems are communicating, they not only need to represent the data in the same format (analog/digital) but they must also use the same synchronization technique. This process tells the receiver when a specific communication begins and ends so two-way conversations can happen without talking over one another. The two types of techniques are asynchronous transmission and synchronous transmission.
With asynchronous transmissions, the systems use start and stop bits to communicate when each byte is starting and stopping. This method also uses parity bits for the purpose of ensuring that each byte has not changed or been corrupted en route. This introduces additional overhead to the transmission.
Synchronous transmission uses a clocking mechanism to synch up the sender and receiver. Data is transferred in a stream of bits with no start, stop, or parity bits. This clocking mechanism is embedded into the layer 2 protocol. It uses a different form of error checking (cyclical redundancy check or CRC) and is preferable for high-speed, high-volume transmissions. Figure 3-9 shows a visual comparison of the two techniques.
Figure 3-9. Asynchronous versus Synchronous

Broadband versus Baseband
All data transfers use a communication channel. Multiple transmissions might need to use the same channel. Sharing this medium can be done in two different ways: broadband or baseband. The difference is in how the medium is shared.
In baseband, the entire medium is used for a single transmission, and then multiple transmission types are assigned time slots to use this single circuit. This is called Time Division Multiplexing (TDM). Multiplexing is the process of using the same medium for multiple transmissions. The transmissions take turns rather than sending at the same time.
Broadband, on the other hand, divides the medium in different frequencies, a process called Frequency Division Multiplexing (FDM). This has the benefit of allowing true simultaneous use of the medium.
An example of broadband transmission is DSL, where the phone signals are sent at one frequency and the computer data at another. This is why you can talk on the phone and use the Web at the same time. Figure 3-10 illustrates these two processes.
Figure 3-10. Broadband versus Baseband

Unicast, Multicast, and Broadcast
When systems are communicating in a network they might send out three types of transmissions. These methods differ in the scope of their reception as follow:
• Unicast: Transmission from a single system to another single system. It is considered one-to-one.
• Multicast: A signal is received by all others in a group called a multicast group. It is considered one-to-many.
• Broadcast: A transmission sent by a single system to all systems in the network. It is considered one-to-all.
Figure 3-11 illustrates the three methods.
Figure 3-11. Unicast, Multicast, and Broadcast

Wired versus Wireless
As you probably know by now, not all transmissions occur over a wired connection. Even within the category of wired connections, the way in which the ones and zeros are represented can be done in different ways. In a copper wire, the ones and zeros are represented with changes in the voltage of the signal, whereas in a fiberoptic cable, they are represented with manipulation of a light source (lasers or LEDs).
In wireless transmission, radios waves or light waves are manipulated to represent the ones and zeros. When infrared technology is used, this is done with infrared light. With WLANs, radio waves are manipulated to represent the ones and zeros. These differences is how the bits are represented occur at the physical and data link layers of the OSI model. When a packet goes from a wireless section of the network to a wired section, these two layers are the only layers that change.
When a different physical medium is used, typically a different layer 2 protocol is called for. For example, while the data is traveling over the wired Ethernet network, the 802.3 standard is used. However, when the data gets to a wireless section of the network, it needs a different layer 2 protocol. Depending on the technology in use, it could be either 802.11 (WLAN) or 802.16 (WiMAX).
The ability of the packet to travers various media types is just another indication of the independence of the OSI layers because the information in layers 3–7 remain unchanged regardless of how many layer 2 transitions must be made to get the data to its final destination.
Cabling
Cabling resides at the physical layer of the OSI model and simply provides a medium on which data can be transferred. The vast majority of data is transferred across cables of various types, including coaxial, fiberoptic, and twisted pair. Some of these cables represent the data in terms of electrical voltages whereas fiber cables manipulate light to represent the data. This section discusses each type.
You can compare cables to one another using several criteria. One of the criteria that is important with networking is the cables susceptibility to attenuation. Attenuation occurs when the signal meets resistance as it travels through the cable. This weakens the signal, and at some point (different in each cable type) the signal is no longer strong enough to be read properly at the destination. For this reason all cables have a maximum length. This is true regardless of whether the cable is fiberoptic or electrical.
Another important point of comparison between cable types is their data rate, which describes how much data can be sent through the cable per second. This area has seen great improvement over the years, going from rates of 10 Mbps in a LAN to 1000 Mbps in today’s networks (and even higher rates in data centers).
Another consideration when selecting a cable type is the ease of installation. Some cable types are easier than others to install, and fiberoptic cabling requires a special skill set to install, raising its price of installation.
Finally (and most importantly for our discussion) is the security of the cable. Cables can leak or radiate information. Cables can also be tapped into by hackers if they have physical access to it. Just as the cable types can vary in allowable length and capacity they can also vary in their susceptibility to these types of data losses.
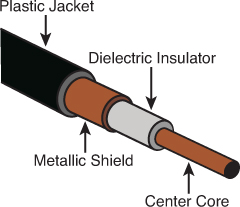
Coaxial
One of the earliest cable types to be used for networking was coaxial, the same basic type of cable that brought cable TV to millions of homes. Although coaxial cabling is still used, due to its low capacity and the adoption of other cable types, its use is almost obsolete now in LANs.
Coaxial cabling comes in two types or thicknesses. The thicker type, called Thicknet, has an official name of 10Base5. This naming system, used for other cable types as well, imparts several facts about the cable. In the case of 10Bbase5 it means that it is capable of transferring 10 Mbps and can go roughly 500 meters. Thicknet uses two types of connectors: a vampire tap (named thusly because it has a spike that pierces the cable) and N-connectors.
Thinnet or 10Base2 also operates at 10 Mbps. Although when it was named it was anticipated to be capable of running 200 feet, this was later reduced to 185 feet. Both types are used in a bus topology (more on topologies in the section “Network Topologies” later in this chapter). Thinnet uses two types of connectors: BNC connectors and T-connectors.
Coaxial has an outer cylindrical covering that surrounds either a solid core wire (Thicknet) or a braided core (Thinnet). This type of cabling has been replaced over time with more capable twisted-pair and fiberoptic cabling. Coaxial cabling can be tapped, so physical access to this cabling should be restricted or prevented if possible. It should be out of sight if it is used. Figure 3-12 shows the structure of a coaxial cable.
Another security problem with coax in a bus topology is that it is broadcast based, which means a sniffer attached anywhere in the network can capture all traffic. In switched networks (more on that topic later in this chapter in the section “Network devices”), this is not a consideration.
Twisted Pair
The most common type of network cabling found today is called twisted-pair cabling. It is called this because inside the cable are four pairs of smaller wires that are braided or twisted. This twisting is designed to eliminate a phenomenon called crosstalk, which occurs when wires that are inside a cable interfere with one another. The number of wire pairs that are used depends on the implementation. In some implementations, only two pairs are used, and in others all four wire pairs are used. Figure 3-13 shows the structure of a twisted-pair cable.
Figure 3-13. Twisted-Pair Cabling

Twisted-pair cabling comes in shielded (STP) and unshielded (UTP) versions. Nothing is gained from the shielding except protection from Radio Frequency Interference (RFI) and Electromagnetic Interference (EMI). RFI is interference from radio sources in the area, whereas EMI is interference from power lines. A common type of EMI is called common mode noise, which is interference that appears on both signal leads (signal and circuit return) or the terminals of a measuring circuit, and ground. If neither EMI nor RFI are a problem, nothing is gained by using STP, and it costs more.
The same naming system used with coaxial and fiber is used with twisted pair. The following are the major types of twisted pair you will encounter:
• 10BaseT: Operates at 10 Mbps
• 100BaseT: Also called Fast Ethernet; operates at 100 Mbps
• 1000BaseT: Also called Gigabit Ethernet; operates at 1000 Mbps
• 10GBaseT: Operates at 10 Gbps
Twisted-pair cabling comes in various capabilities and is rated in categories. Table 3-4 lists the major types and their characteristics. Regardless of the category, twisted-pair cabling can be run about 100 meters before attenuation degrades the signal.

Table 3-4. Twisted-Pair Categories

Fiberoptic
Fiberoptic cabling uses a source of light that shoots down an inner glass or plastic core of the cable. This core is covered by cladding that causes light to be confined to the core of the fiber. Figure 3-14 shows the structure of a fiberoptic cable.
Figure 3-14. Fiberoptic Cabling
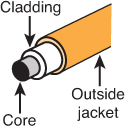
Fiberoptic cabling manipulates light such that it can be interpreted as ones and zeros. Because it is not electrically based, it is totally impervious to EMI, RFI, and crosstalk. Moreover, although not impossible, tapping or eavesdropping on a fiber cable is much more difficult. In most cases, attempting to tap into it results in a failure of the cable, which then becomes quite apparent to all.
Fiber comes in a single and multi-mode format. The single mode uses a single beam of light provided by a laser, goes the further of the two, and is the most expensive. Multi-mode uses several beams of light at the same time, uses LEDs, will not go as far and is less expensive. Either type goes much further than electrical cabling in a single run and also typically provides more capacity. Fiber cabling has its drawbacks, however. It is the most expensive to purchase and the most expensive to install. Table 3-5 shows some selected fiber specifications and their theoretical maximum distances.
Table 3-5. Selected Fiber Specifications

Network Topologies
Networks can be described by their logical topology (the data path used) and by their physical topology (the way in which devices are connected to one another. In most cases the logical topology and the physical topology will be the same but not in all. This section discusses both logical and physical network topologies.
Ring
A physical ring topology is one in which the devices are daisy-chained one to another in a circle or ring. If the network is also a logical ring, the data circles the ring from one device to another. Two technologies use this topology, Fiber Distributed Data Interface (FDDI) and Token Ring. Both of these technologies are discussed in detail in the section, “Network Technologies.” Figure 3-15 shows a typical ring topology.

One of the drawbacks of the ring topology is that if a break occurs in the line, all systems will be affected as the ring will be broken. As you will see in the section “Network Technologies” a FDDI network addresses this issue with a double ring for fault tolerance.
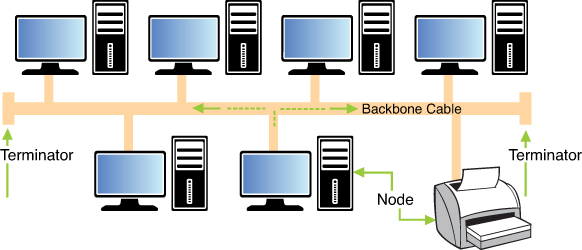
Bus
The bus topology was the earliest Ethernet topology used. In this topology all devices are connected to a single line that has two definitive endpoints. The network does NOT loop back and form a ring. This topology is broadcast based, which can be a security issue in that a sniffer or protocol analyzer connected at any point in the network will be capable of capturing all traffic. From a fault tolerance standpoint, the bus topology suffers the same danger as a ring. If a break occurs anywhere in the line all devices are affected. Moreover, a requirement specific to this topology is that each end of the bus must be terminated. This prevents signals from “bouncing” back on the line causing collisions. (More on collisions later, but collisions require the collided packets to be sent again, lowering overall throughput.) If this termination is not done properly, the network will not function correctly. Figure 3-16 shows a bus topology.
Star
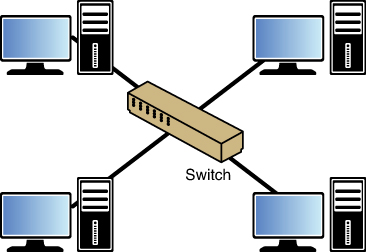
The star topology is the most common in use today. In this topology all devices are connected to a central device (either a hub or a switch). One of the advantages of this topology is that if a connection to any single device breaks, ONLY that device is affected and no others. The downside of this topology is that a single point of failure (the hub or switch) exists. If the hub or switch fails all devices are affected. Figure 3-17 shows a star topology.
Mesh
Although the mesh topology is the most fault tolerant of any discussed thus far, it is also the most expensive to deploy. In this topology all devices are connected to all other devices. This provides complete fault tolerance but also requires multiple interfaces and cables on each device. For that reason it is deployed only in rare circumstances where such an expense is warranted. Figure 3-18 shows a mesh topology.

Hybrid
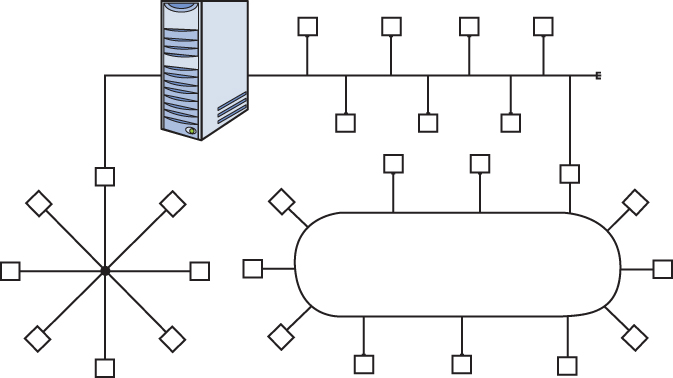
In many cases an organization’s network is a combination of these network topologies, or a hybrid network. For example, one section might be a star that connects to a bus network or a ring network. Figure 3-19 shows an example of a hybrid network.
Network Technologies
Just as a network can be connected in various topologies, different technologies have been implemented over the years that run over those topologies. These technologies operate at layer 2 of the OSI model, and their details of operation are specified in various standards by the Institute of Electrical and Electronics Engineers (IEEE). Some of these technologies are designed for Local Area Network (LAN) applications whereas others are meant to be used in a Wide Area Network (WAN). In this section we’ll look at the main LAN technologies and some of the processes that these technologies use to arbitrate access to the network.
Ethernet 802.3
The IEEE specified the details of Ethernet in the 802.3 standard. Prior to this standardization Ethernet existed in several earlier forms, the most common of which was called Ethernet ll or DIX Ethernet (DIX stands for the three companies that collaborated on its creation, DEC, Intel and Xerox).
In the section on the OSI model you learned that the protocol data unit (PDU) created at layer 2 is called a frame. Because Ethernet is a layer 2 protocol we refer to the individual Ethernet packets as frames. There are small differences in the frame structures of Ethernet ll and 802.3, although they are compatible in the same network. Figure 3-20 shows a comparison of the two frames. The significant difference is that during the IEEE standardization process, the EtherType field was changed to a (data) length field in the new 802.3 standard. For purposes of identifying the data type another field called the 802.2 header was inserted to contain that information.
Figure 3-20. Ethernet ll and 802.3
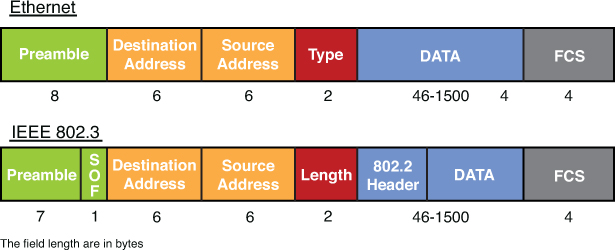
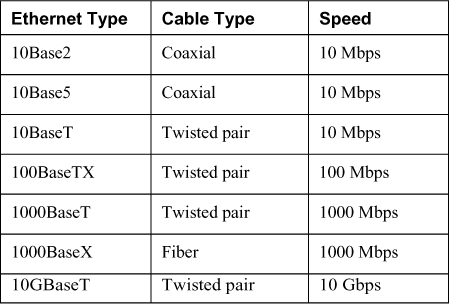
Ethernet has been implemented on coaxial, fiber, and twisted-pair wiring. Table 3-6 lists some of the more common Ethernet implementations.

Table 3-6. Ethernet Implementations
Note
Despite the fact that 1000 BaseT and 1000 BaseX are faster, 100 BaseTX is called Fast Ethernet! Also both 1000 BaseT and 1000 BaseX are usually referred to as Gigabit Ethernet.
Ethernet calls for devices to share the medium on a frame-by-frame basis. It arbitrates access to the media using a process called Carrier Sense Multiple Access with Collision Detection (CSMA/CD). This process is discussed in detail in the section “CSMA/CD versus CSMA/CA” where the process will be contrasted with the method used in 802.11 wireless networks.
Token Ring 802.5
Ethernet is the most common layer 2 protocol, but it has not always been that way. An example of a proprietary layer 2 protocol that enjoyed some small success is IBM Token Ring. This protocol operates using specific IBM connective devices and cables, and the nodes must have Token Ring network cards installed. It can operate at 16 Mbps, which at the time of its release was impressive, but the propriety nature of the equipment and the soon-to-be faster Ethernet caused Token Ring to fall from favor.
As mentioned earlier, in most cases the physical network topology is the same as the logical topology. Token Ring is the exception to that general rule. It is logically a ring and physically a star. It is a star in that all devices are connected to a central device called a Media Access Unit (MAU), but the ring is formed in the MAU and when you investigate the flow of the data it goes from one device to another in a ring design by entering and exiting each port of the MAU, as shown on Figure 3-21.

FDDI
Another layer 2 protocol that uses a ring topology is Fiber Distributed Data Interface (FDDI). Unlike Token Ring it is both a physical and a logical ring. It is actually a double ring, each going in a different direction to provide fault tolerance. It also is implemented with fiber cabling. In many cases it is used for a network backbone and is then connected to other network types, such as Ethernet, forming a hybrid network. It is also used in Metropolitan Area Networks (MANs) because it can be deployed up to 100 kilometers.
Figure 3-22 shows an example of an FFDI ring.

Contention Methods
Regardless of the layer 2 protocol in use, there must be some method used to arbitrate the use of the shared media. Four basic processes have been employed to act as the traffic cop, so to speak:
• CSMA/CD
• CSMA/CA
• Polling
This section compares and contrasts each and provides examples of technologies that use each.
CSMA/CD Versus CSMA/CA
To appreciate CSMA/CD and CSMA/CA, you must understand the concept of collisions and collision domains in a shared network medium. Collisions occur when two devices send a frame at the same time causing the frames and their underlying electrical signals to collide on the wire. When this occurs both signals and the frames they represent are destroyed or at the very least corrupted such that they are discarded when they reach the destination. Frame corruption or disposal causes both devices to resend the frames, resulting in a drop in overall throughput.
Collision Domains
A collision domain is any segment of the network where the possibility exists for two or more devices’ signals to collide. In a bus topology, that would constitute the entire network because the entire bus is a shared medium. In a star topology, the scope of the collision domain or domains depends on the central connecting device. Central connecting devices include hubs and switches. Hubs and switches are discussed more fully in the section “Network Devices” but their differences with respect to collision domains need to be discussed here.
A hub is an unintelligent junction box into which all devices plug. All the ports in the hub are in the same collision domain because when a hub receives a frame the hub broadcasts the frame out all ports. So logically the network is still a bus.
A star topology with a switch in the center does not operate this way. A switch has the intelligence to record the MAC address of each device on every port. After all the devices’ MAC addresses are recorded, the switch sends a frame ONLY to the port on which the destination device resides. Because each device’s traffic is then segregated from any other device’s traffic, each device is considered to be in its own collision domain.
This segregation provided by switches has both performance and security benefits. From a performance perspective, it greatly reduces the number of collisions, thereby significantly increasing overall throughput in the network. From a security standpoint, it means that a sniffer connected to a port in the switch will ONLY capture traffic destined for that port, not all traffic. Compare this security to a hub-centric network. When a hub is in the center of a star network, a sniffer will capture all traffic regardless of the port to which it is connected because all ports are in the same collision domain.
In Figure 3-23, a switch has several devices and a hub connected to it with each collision domain marked to show how the two devices create collision domains. Note that each port on the switch is a collision domain whereas the entire hub is a single collision domain.
Figure 3-23. Collision Domains

CSMA/CD
In 802.3 networks a mechanism called Carrier Sense Multiple Access Collision Detection (CSMA/CD) is used when a shared medium is in use to recover from inevitable collisions. This process is a step-by-step mechanism that each station follows every time it needs to send a single frame. The steps to the process are as follow:

1. When a device needs to transmit, it checks the wire for existing traffic. This process is called carrier sense.
2. If the wire is clear, the device transmits and continues to perform carrier sense.
3. If a collision is detected, both devices issue a jam signal to all the other devices, which indicates to them to NOT transmit. Then both devices increment a retransmission counter. This is a cumulative total of the number of times this frame has been transmitted and a collision occurred. There is a maximum number at which it aborts the transmission of the frame.
4. Both devices calculate a random amount of time (called a called a random back off) and wait that amount of time before transmitting again.
5. In most cases because both devices choose random amounts of time to wait, another collision will not occur. If it does, the procedure repeats.
CSMA/CA
In 802.11 wireless networks CSMA/CD cannot be used as an arbitration method because unlike when using bounded media, the devices cannot detect a collision. The method used is called Carrier Sense Multiple Access Collision Avoidance (CSMA/CA). It is a much more laborious process because each station must acknowledge each frame that is transmitted.
The “Wireless Networks” section covers 802.11 network operations in more detail, but for the purposes of understanding CSMA/CA we must at least lay some groundwork. The typical wireless network contains an access point (AP) and at least one or more wireless stations. In this type of network (called Infrastructure Mode wireless network), traffic never traverses directly between stations but is always relayed through the AP. The steps in CSMA/CA are as follow:

1. Station A has a frame to send to Station B. It checks for traffic in two ways. First it performs carrier sense, which means it listens to see whether any radio waves are being received on its transmitter. Secondly, after the transmission is sent it will continue to monitor the network for possible collisions.
2. If traffic is being transmitted, Station A decrements an internal countdown mechanism called the random back-off algorithm. This counter will have started counting down after the last time this station was allowed to transmit. All stations will be counting down their own individual timers. When a station’s timer expires, it is allowed to send.
3. If Station A performs carrier sense, there is no traffic, and its timer hits zero, it sends the frame.
4. The frame goes to the AP.
5. The AP sends an acknowledgment back to Station A. Until that acknowledgment is received by Station A, all other stations must remain silent. For each frame that AP needs to relay, it must wait its turn to send using the same mechanism as the stations.
6. When its turn comes up in the cache queue, the frame from Station A is relayed to Station B.
7. Station B sends an acknowledgment back to the AP. Until that acknowledgment is received by the AP, all other stations must remain silent.
As you can see, these processes create a lot of overhead but are required to prevent collisions in a wireless network.
Token Passing
Both FDDI and Token Ring networks use a process called token passing. In this process a special packet called a token is passed around the network. A station cannot send until the token comes around and is empty. Using this process, NO collisions occur because two devices are never allowed to send at the same time. The problem with this process is that the possibility exists for a single device to gain control of the token and monopolize the network.
Polling
The final contention method to discuss is polling. In this system a primary device polls each other device to see whether it needs to transmit. In this way each device gets a transmit opportunity. This method is common in the mainframe environment.
Network Protocols/Services
Many protocols and services have been developed over the years to add functionality to networks. In many cases these protocols reside at the Application layer of the OSI model. These Application layer protocols usually perform a specific function and rely on the lower layer protocols in the TCP/IP suite and protocols at layer 2 (like Ethernet) to perform routing and delivery services.
This section covers some of the most important of these protocols and services, including some that do NOT operate at the Application layer, focusing on the function and port number of each. Port numbers are important to be aware of from a security standpoint because in many cases port numbers are referenced when configuring firewall rules. In cases where a port or protocol number is relevant they will be given as well.
ARP
Address Resolution Protocol (ARP), one of the protocols in the TCP/IP suite, operates at layer 3 of the OSI model. The information it derives is utilized at layer 2, however. ARP’s job is to resolve the destination IP address placed in the header by IP to a layer 2 or MAC address. Remember, when frames are transmitted on a local segment the transfer is done in terms of MAC addresses not IP addresses, so this information must be known.
Whenever a packet is sent across the network, at every router hop and again at the destination subnet, the source and destination MAC address pairs change but the source and destination IP addresses not. The process that ARP uses to perform this resolution is called an ARP broadcast.
First an area of memory called the ARP cache is consulted. If the MAC address has been recently resolved, the mapping will be in the cache and a broadcast is not required. If the record has aged out of the cache, ARP sends a broadcast frame to the local network that all devices will receive. The device that possesses the IP address responds with its MAC address. Then ARP places the MAC address in the frame and sends the frame. Figure 3-24 illustrates this process.
DHCP
Dynamic Host Configuration Protocol (DHCP) is a service that can be used to automate the process of assigning an IP configuration to the devices in the network. Manual configuration of an IP address, subnet mask, default gateway, and DNS server is not only time consuming but fraught with opportunity for human error. Using DHCP can not only automate this, but can also eliminate network problems from this human error.
DHCP is a client/server program. All modern operating systems contain a DHCP client, and the server component can be implemented either on a server or on a router. When a computer that is configured to be a DHCP client starts, it performs a precise four-step process to obtain its configuration. Conceptually, the client broadcasts for the IP address of the DHCP server. All devices receive this broadcast, but only DHCP servers respond. The device accepts the configuration offered by the first DHCP server from which it hears. The process uses four packets with distinctive names (see Figure 3-25). DHCP uses UDP ports 67 and 68. Port 67 sends data to the server, and port 68 sends data to the client.

DNS
Just as DHCP relieves us from having to manually configure the IP configuration of each system, Domain Name System (DNS) relieves all humans from having to know the IP address of every computer with which they want to communicate. Ultimately, an IP address must be known to connect to another computer. DNS resolves a computer name (or in the case of the web a domain name) to an IP address.
DNS is another client/server program with the client included in all modern operating systems. The server part resides on a series of DNS servers located both in the local network and on the Internet. When a DNS client needs to know the IP address that goes with a particular computer name or domain name, it queries the local DNS server. If the local DNS server does not have the resolution, it contacts other DNS servers on the client’s behalf, learns the IP address, and relays that information to the DNS client. DNS uses UDP port 53 and TCP port 53. The DNS servers use TCP port 53 to exchange information, and the DNS clients use UDP port 53 for queries.
FTP, FTPS, SFTP
File Transfer Protocol (FTP), and its more secure versions FTPS and SFTP, transfers files from one system to another. FTP is insecure in that the username and password is transmitted in clear text. The original clear text version uses TCP port 20 for data and TCP port 21 as the control channel. Using FTP when security is a consideration is not recommended.
FTPS is FTP that adds support for the Transport Layer Security (TLS) and the Secure Sockets Layer (SSL) cryptographic protocols. FTPS uses TCP ports 989 and 990.
FTPS is not the same as and should not be confused with another secure version of FTP, SSH File Transfer Protocol (SFTP). This is an extension of the Secure Shell Protocol (SSH). There have been a number of different versions with version 6 being the latest. Because it uses SSH for the file transfer, it uses TCP port 22.
HTTP, HTTPS, SHTTP
One of the most frequently used protocols today is Hypertext Transfer Protocol (HTTP) and its secure versions, HTTPS and SHTTP. This protocol is used to view and transfer web pages or web content. The original version (HTTP) has no encryption so when security is a concern one of the two secure versions should be used. HTTP uses TCP port 80.
Hypertext Transfer Protocol Secure (HTTPS) layers the HTTP on top of the SSL/TLS protocol, thus adding the security capabilities of SSL/TLS to standard HTTP communications. It is often used for secure websites because it requires no software or configuration changes on the web client to function securely. When HTTPS is used, port 80 is not used. Rather it uses port 443.
Unlike HTTPS, which encrypts the entire communication, SHTTP encrypts only the served page data and submitted data such as POST fields, leaving the initiation of the protocol unchanged. Secure-HTTP and HTTP processing can operate on the same TCP port, port 80. This version is rarely used.
ICMP
Internet Control Message Protocol (ICMP) operates at layer 3 of the OSI model and is used by devices to transmit error messages regarding problems with transmissions. It also is the protocol used when the ping and traceroute commands are used to troubleshoot network connectivity problems. Because IP is part of the TCP/IP suite, it doesn’t use a port number but is identified in the packet by its protocol number. Its protocol number is 1.
ICMP is a protocol that can be leveraged to mount several network attacks based on its operation, and for this reason many networks choose to block ICMP. These attacks are discussed in the section “Network Threats.”
IMAP
Internet Message Access Protocol (IMAP) is an Application layer protocol for email retrieval. Its latest version is IMAP4. It is a client email protocol used to access email from a server. Unlike POP3, another email client that can only download messages from the server, IMAP4 allows one to download a copy and leave a copy on the server. IMAP 4 uses port 143. A secure version also exists, IMAPS (IMAP over SSL) that uses port 993.
NAT
Network Address Translation is a service that maps private IP addresses to public IP addresses. It is discussed in the section “Logical and Physical addressing” earlier in this chapter.
PAT
Port Address Translation (PAT) is a specific version of NAT that uses a single public IP address to represent multiple private IP addresses. Its operation is discussed in the section “Logical and Physical Addressing” earlier in this chapter
POP
Post Office Protocol (POP) is an Application layer email retrieval protocol. POP3 is the latest version. It allows for downloading messages only and does not allow the additional functionality provided by IMAP4. POP3 uses port 110. A version that runs over SSL is also available that uses port 995.
SMTP
POP and IMAP are client email protocols used for retrieving email, but when email servers are talking to each other they use a protocol called Simple Mail Transfer Protocol (SMTP), a standard Application layer protocol. This is also the protocol used by clients to send email. SMTP uses port 25, and when it is runs over SSL it uses port 465.
SNMP
Simple Network Management Protocol (SNMP) is an Application layer protocol that is used to retrieve information from network devices and to send configuration changes to those devices. SNMP uses TCP port 162 and UDP ports 161 and 162.
SNMP devices are organized into communities and the community name must be known to either access information from or send a change to a device. It also can be used with a password. SNMP versions 1 and 2 are susceptible to packet sniffing, and all versions are susceptible to brute-force attacks on the community strings and password used. The defaults of community string names, which are widely known, are often left in place. The latest version, SNMPv3 is the most secure.
Network Routing
Routing occurs at layer 3 of the OSI model, which is also the layer at which IP operates and where the source and destination IP addresses are placed in the packet. Routers are devices that transfer traffic between systems in different IP networks. When computers are in different IP networks, they cannot communicate unless a router is available to route the packets to the other networks.
Routers keep information about the paths to other networks in a routing table. These tables can be populated several ways. Administrators manually enter these routes, or dynamic routing protocols allow the routers running the same protocol to exchange routing tables and routing information. Manual configuration, also called static routing, has the advantage of avoiding the additional traffic created by dynamic routing protocols and allows for precise control of routing behavior, but requires manual intervention when link failures occur. Dynamic routing protocols create traffic but are able to react to link outages and reroute traffic without manual intervention.
From a security standpoint, routing protocols introduce the possibility that routing update traffic might be captured, allowing a hacker to gain valuable information about the layout of the network. Moreover, Cisco devices (perhaps the most widely used) also use a proprietary layer 2 protocol by default called Cisco Discovery Protocol (CDP) that they use to inform each other about their capabilities. If the CDP packets are captured, additional information can be obtained that can be helpful to mapping the network in advance of an attack.
This section compares and contrasts routing protocols.
Distance Vector, Link State, or Hybrid Routing
Routing protocols have different capabilities and operational characteristics that impact when and where they are utilized. Routing protocols come in two basic types: interior and exterior. Interior routing protocols are used within an autonomous system, which is a network managed by one set of administrators, typically a single enterprise. Exterior routing protocols route traffic between systems or company networks. An example of this type of routing is what occurs on the Internet.
Routing protocols also can fall into three categories that describe their operations more than their scope: distance vector, link state, and hybrid (or advanced distance vector). The difference in these mostly revolves around the amount of traffic created and the method used to determine the best path out of possible paths to a network. The value used to make this decision is called a metric, and each has a different way of calculating the metric and thus determining the best path.
Distance vector protocols share their entire routing table with their neighboring routers on a schedule, thereby creating the most traffic of the three categories. They also use a metric called hop count. Hop count is simply the number of routers traversed to get to a network.
Link state protocols only share network changes (link outages and recoveries) with neighbors, thereby greatly reducing the amount of traffic generated. They also use a much more sophisticated metric that is based on many factors, such as the bandwidth of each link on the path and the congestion on each link. So when using one of these protocols, a path might be chosen as best even though it has more hops because the path chosen has better bandwidth, meaning less congestion.
Hybrid or advanced distance vector protocols exhibit characteristics of both types. EIGRP, discussed later in this section, is the only example of this type. In the past EIGRP has been referred to as a hybrid protocol but in the last several years Cisco (which created IGRP and EIGRP) has been calling this an advanced distance vector protocol so you might see both terms used. In the following sections several of the most common routing protocols are discussed briefly.
RIP
Routing Information Protocol (RIP) is a standards-based distance vector protocol that has two versions: RIPv1 and RIPv2. Both use hop count as a metric and share their entire routing tables every 30 seconds. Although RIP is the simplest to configure, it has a maximum hop count of 15, so it is only useful in very small networks. The biggest difference between the two versions is that RIPv1 can only perform classful routing whereas RIPv2 can route in a network where CIDR has been implemented.
OSPF
Open Shortest Path First (OSPF) is a standards-based link state protocol. It uses a metric called cost that is calculated based on many considerations. Thus it makes much more sophisticated routing decisions than a distance vector routing protocol such as RIP. It also only updates other routers with changes, greatly reducing the amount of traffic generated. To take full of advantage of OSPF, a much deeper knowledge of routing and OSPF itself is required. It can scale successfully to very large networks because it has no minimum hop count.
IGRP
Interior Gateway Routing Protocol is an obsolete classful Cisco-propriety routing protocol that you will not likely see in the real world because of its inability to operate in an environment where CIDR has been implemented. It has been replaced with the classless version Enhanced IGRP (EIGRP) discussed next.
EIGRP
Enhanced IGRP (EIGRP) is a classless Cisco-propriety routing protocol that is considered a hybrid or advanced distance vector protocol. It exhibits some characteristics of both link state and distance vector operations. It also has no limitations on hop count and is much simpler to implement than OSPF. It does, however, require that all routers be Cisco.
VRRP
When a router goes down, all hosts that use that router for routing will be unable to send traffic to other networks. Virtual Router Redundancy Protocol (VRRP) is not really a routing protocol but rather is used to provide multiple gateways to clients for fault tolerance in the case of a router going down. All hosts in a network are set with the IP address of the virtual router as their default gateway. Multiple physical routers are mapped to this address so there will be an available router even if one goes down.
IS-IS
Intermediate system to Intermediate system (IS-IS) is a complex interior routing protocol that is based on OSI protocols rather than IP. It is a link state protocol. The TCP/IP implementation is called Integrated IS-IS. OSPF has more functionality, but IS-IS creates less traffic than OSPF and is much less widely implemented than OSPF.
BGP
Border Gateway Protocol (BGP) is an exterior routing protocol considered to be a path vector protocol. It routes between autonomous systems (ASs) and is used on the Internet. It has a rich set of attributes that can be manipulated by administrators to control path selection and to control the exact way in which traffic enters and exits the AS. However, it is one of the most complex to understand and configure.
Network Devices
Network devices operate at all layers of the OSI model. The layer at which they operate reveals quite a bit about their level of intelligence and about the types of information used by each device. This section covers common devices and their respective roles in the overall picture.
Patch Panel
Patch panels operate at the Physical (layer 1) of the OSI model and simply function as a central termination point for all the cables running through the walls from wall outlets, which in turn are connected to computers with cables. The cables running through the walls to the patch panel are permanently connected to the panel. Short cables called patch cables are then used to connect each panel port to a switch or hub.
Multiplexer
A multiplexer is a physical (layer 1) device that combines several input information signals into one output signal, which carries several communication channels, by means of some multiplex technique. Conversely, a demultiplexer takes a single input signal that carries many channels and separates those over multiple output signals. Sharing the same physical medium can be done in a number of different ways: on the basis of frequencies used (frequency division multiplexing or FDM) or by using time slots (time division multiplexing or TDM).
Hub
A hub is a physical (layer 1) device that functions as a junction point for devices in a star topology. It is considered a physical layer device because it has no intelligence. When a hub receives traffic, it broadcasts that traffic out of every port because it does not have the intelligence to make any decisions about where the destination is located.
Although this results in more collisions and poor performance, from a security standpoint the problem is that it broadcasts all traffic to all ports. A sniffer connected to any port will be able to sniff all traffic. The operation of a hub is shown in Figure 3-26. When a switch is used, that is not the case (more on those later in this section).

Switch
Switches are intelligent and operate at layer 2 of the OSI model. We say they map to this layer because they make switching decisions based on MAC addresses, which reside at layer 2. This process is called transparent bridging. Figure 3-27 shows this process.
Figure 3-27. Transparent Bridging
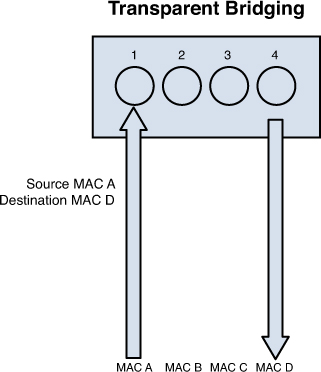
Switches improve performance over hubs because they eliminate collisions. Each switch port is in its own collision domain, whereas all ports of a hub are in the same collision domain. From a security standpoint, switches are more secure in that a sniffer connected to any single port will only be able to capture traffic destined for or originating from that port.
Some switches, however, are both routers and switches, and in that case we call them layer 3 switches because they route and switch.
VLANs
Enterprise-level switches are also capable of another functionality called virtual local area networks (VLANs). These are logical subdivisions of a switch that segregate ports from one another as if they were in different LANs. These VLANs can also span multiple switches, meaning that devices connected to switches in different parts of a network can be placed in the same VLAN regardless of physical location.
VLANs offer another way to add a layer of separation between sensitive devices and the rest of the network. For example, if only two devices should be able to connect to the HR server, the two devices and the HR server could be placed in a VLAN separate from the other VLANs. Traffic between VLANs can only occur through a router. Routers can be used to implement access control lists (ACLs) that control the traffic allowed between VLANs.
Layer 3 versus Layer 4
Typically we map the switching process to layer 2 of the OSI model because layer 2 addresses are used to make frame-forwarding decisions. That doesn’t mean that a single physical device cannot be capable of both functions. A layer 3 switch is such a device. It is a switch with the routing function also built in. It can both route and switch and can combine the two functions in an integrated way such that a single data stream can be routed when the first packet arrives and then the rest of the packets in the stream can be fast switched, resulting in better performance.
Layer 4 switches take this a step further by providing additional routing above layer 3 by using the port numbers found in the Transport layer header to make routing decisions. The largest benefit of layer 4 switching is the ability to prioritize data traffic by application, which means a quality of service (QoS) can be defined for each user.
Router
Routers operate at layer 3 (Network layer) when we are discussing the routing function in isolation. As previously discussed, certain devices can combine routing functionality with switching and layer 4 filtering. However, because routing uses layer 3 information (IP addresses) to make decisions, it is a layer 3 function.
Routers use a routing table that tells the router in which direction to send traffic destined for a particular network. Although routers can be configured with routes to individual computers, typically they route toward networks, not individual computers. When the packet arrives at the router that is directly connected to the destination network, that particular router performs an ARP broadcast to learn the MAC address of the computer and send the packets as frames at layer 2.
Routers perform an important security function because on them access lists (ACLs) are typically configured. These are ordered sets of rules that control the traffic that is permitted or denied the use of a path through the router. These rules can operate at layer 3 making these decisions on the basis of IP addresses or at layer 4 when only certain types of traffic are allowed. When this is done the ACL typically references a port number of the service or application that is allowed or denied.
Gateway
The term gateway doesn’t refer to a particular device but rather to any device that performs some sort of translation or acts as a control point to entry and exit. For example, if a router has one interface that uses TCP/IP and another interface that uses IPX/SPX (a now obsolete LAN protocol), we would say it is performs as a gateway between the two protocols.
Another example of a device performing as a gateway would be an email server. It receives email from all types of email servers (Exchange, IBM Notes, Novell GroupWise) and performs any translation of formats that is necessary between these different implementations.
Finally, but certainly not the last example would be a Network Access Server (NAS) that controls access to a network. This would be considered a gateway in that all traffic might need to be authenticated before entry is allowed. This type of server might even examine the computers themselves for the latest security patches and updates before entry is allowed.
Firewall
The network device that perhaps is most connected with the idea of security is the firewall. Firewalls can be software programs that are installed over server operating systems or they can be appliances that have their own operating system. In either case their job is to inspect and control the type of traffic allowed.
Firewalls can be discussed on the basis of their type and their architecture. They can also be physical devices or exist in a virtualized environment. This section looks at them from all angles.
Types
When we discuss types of firewalls we are focusing on the differences in the way they operate. Some firewalls make a more thorough inspection of traffic than others. Usually there is tradeoff in the performance of the firewall and the type of inspection that it performs. A deep inspection of the contents of each packet results in the firewall having a detrimental effect on throughput whereas a more cursory look at each packet has somewhat less of an impact on performance. It is for this reason we make our selections of what traffic to inspect wisely, keeping this tradeoff in mind.
Packet filtering firewalls are the least detrimental to throughput because they only inspect the header of the packet for allowed IP addresses or port numbers. Although even performing this function will slow traffic, it involves only looking at the beginning of the packet and making a quick allow or disallow decision.
Although packet filtering firewalls serve an important function, they cannot prevent many attack types. They cannot prevent IP spoofing, attacks that are specific to an application, attacks that depend on packet fragmentation, or attacks that take advantage of the TCP handshake. More advanced inspection firewall types are required to stop these attacks.
Stateful firewalls are those that are aware of the proper functioning of the TCP handshake, keep track of the state of all connections with respect to this process, and can recognize when packets are trying to enter the network that don’t make sense in the context of the TCP handshake. You might recall the discussion of how the TCP handshake occurs from the section titled “Transport Layer” earlier in this chapter.
To review that process, a packet should never arrive at a firewall for delivery that has both the SYN flag and the ACK flag set unless it is part of an existing handshake process and it should be in response to a packet sent from inside the network with the SYN flag set. This is the type of packet that the stateful firewall would disallow. It also has the ability to recognize other attacks types that attempt to misuse this process. It does this by maintaining a state table about all current connections and the status of each connection process. This allows it to recognize any traffic that doesn’t make sense with the current state of the connection. Of course, maintaining this table and referencing the table causes this firewall type to have more effect on performance than a packet filtering firewall.
Proxy firewalls actually stand between each connection from the outside to the inside and make the connection on behalf of the endpoints. Therefore there is no direct connection. The proxy firewall acts as a relay between the two endpoints. Proxy firewalls can operate at two different layers of the OSI model. Both are discussed shortly.
Circuit-level proxies operate at the Session layer (layer 5) of the OSI model. They make decisions based on the protocol header and Session layer information. Because they do not do deep packet inspection (at layer 7 or the Application layer), they are considered application independent and can be used for wide ranges of layer 7 protocol types.
A SOCKS firewall is an example of a circuit-level firewall. This requires a SOCKS client on the computers. Many vendors have integrated their software with SOCKS to make using this type of firewall easier.
Application-level proxies perform deep packet inspection. This type of firewall understands the details of the communication process at layer 7 for the application of interest. An application-level firewall maintains a different proxy function for each protocol. For example, for HTTP the proxy will be able to read and filter traffic based on specific HTTP commands. Operating at this layer requires each packet to be completely opened and closed, making this firewall the most impactful on performance.
Dynamic packet filtering rather than describing a different type of firewall describes functionality that a firewall might or might not possess, When internal computers attempt to establish a session with a remote computer it places both a source and destination port number in the packet. For example, if the computer is making a request of a web server, because HTTP uses port 80 the destination will be port 80.
The source computer selects the source port at random from the numbers available above the well-known port numbers, or above 1023. Because predicting what that random number will be is impossible, creating a firewall rule that anticipates and allows traffic back through the firewall on that random port is impossible. A dynamic packet filtering firewall will keep track of that source port and dynamically add a rule to the list to allow return traffic to that port.
A kernel proxy firewall is an example of a fifth-generation firewall. It inspects the packet at every layer of the OSI model but does not introduce the performance hit that an Application layer firewall will because it does this at the kernel layer. It also follows the proxy model in that it stands between the two systems and creates connections on their behalf.
Architecture
Although the type of firewall speaks to the internal operation of the firewall, the architecture refers to the way in which the firewall or firewalls are deployed in the network to form a system of protection. This section looks at the various ways firewalls can be deployed and what the names of these various configurations are.
A bastion host might or might not be a firewall. The term actually refers to the position of any device. If it is exposed directly to the Internet or to any untrusted network, we would say it is a bastion host. Whether it is a firewall, a DNS server, or a web server, this means all standard hardening procedures become even more important for these exposed devices. Any unnecessary services should be stopped, all unneeded ports should be closed, and all security patches must be up to date. These procedures are referred to as reducing the attack surface.
A dual-homed firewall is one that has two network interfaces, one pointing to the internal network and another connected to the untrusted network. In many cases routing between these interfaces is turned off. The firewall software allows or denies traffic between the two interfaces based on the firewall rules configured by the administrator. The danger of relying on a single dual-homed firewall is that there is a single point of failure. If this device is compromised, the network is also. If it suffers a denial of service attack, no traffic will pass. Neither is a good situation.
In some cases the firewall may be multihomed. One popular type is the three-legged firewall. In this configuration are three interfaces: one connected to the untrusted network, one to the internal network, and the last to a part of the network called a Demilitarized Zone (DMZ). A DMZ is a portion of the network where systems are placed that will be accessed regularly from the untrusted network. These might be web servers or an email server, for example. The firewall can then be configured to control the traffic that flows between the three networks, being somewhat careful with traffic destined for the DMZ and then treating traffic to the internal network with much more suspicion.
Although the firewalls discussed thus far typically connect directly to the untrusted network (at least one interface does), a screened host is a firewall that is between the final router and the internal network. When traffic comes into the router and is forwarded to the firewall, it will be inspected before going into the internal network.
Taking this concept a step further is a screened subnet. In this case, two firewalls are used, and traffic must be inspected at both firewalls to enter the internal network. It is called screen subnet because there will be a subnet between the two firewalls that can act as a DMZ for resources from the outside world.
In the real world, these various approaches are mixed and matched to meet requirements, so you might find elements of all of these architectural concepts being applied to a specific situation.
Virtualization
Today physical servers are increasingly being consolidated as virtual servers on the same physical box. Virtual networks using virtual switches even exist in the physical devices that host these virtual servers. These virtual network systems and their traffic can be segregated in all the same ways as in a physical network using subnets, VLANs, and of course, virtual firewalls. Virtual firewalls are software that has been specifically written to operate in the virtual environment. Increasingly, virtualization vendors such as VMware are making part of their code available to security vendors to create firewalls (and antivirus products) that integrate closely with the product.
Keep in mind that in any virtual environment each virtual server that is hosted on the physical server must be configured with its own security mechanisms. These mechanisms include antivirus and antimalware software and all the latest service packs and security updates for ALL the software hosted on the virtual machine. Also, remember that all the virtual servers share the resources of the physical device.
Proxy Server
Proxy servers can be appliances or they can be software that is installed on a server operating system. These servers act like a proxy firewall in that they create the web connection between systems on their behalf, but they can typically allow and disallow traffic on a more granular basis. For example, a proxy server might allow the Sales group to go to certain websites while not allowing the Data Entry group access to these same sites. The functionality extends beyond HTTP to other traffic types, such as FTP and others.
Proxy servers can provide an additional beneficial function called web caching. When a proxy server is configured to provide web caching, it saves a copy of all web pages that have been delivered to internal computers in a web cache. If any user requests the same page later, the proxy server has a local copy and need not spend the time and effort to retrieve it from the Internet. This greatly improves web performance for frequently requested pages.
PBX
A private branch exchange (PBX) is a private telephone switch that resides on the customer premises. It has a direct connection to the telecommunication provider’s switch. It performs call routing within the internal phone system. This is how a company can have two “outside” lines but 50 internal phones. The call comes in on one of the two outside lines, and the PBX routes it to the proper extension. Sometimes the system converts analog to digital but not always.
The security considerations with these devices revolve around their default configurations. They typically are configured with default administrator passwords that should be changed, and they often contain backdoor connections that can be used by vendor support personal to connect in and help with problems. These back doors are usually well known and should be disabled until they are needed.
Honeypot
Honeypots are systems that are configured to be attractive to hackers and lure them into spending time attacking them while information is gathered about the attack. In some cases entire networks called honeynets are attractively configured for this purpose. These types of approaches should only be undertaken by companies with the skill to properly deploy and monitor them.
Care should be taken that the honeypots and honeynets do not provide direct connections to any important systems. This prevents providing a jumping-off point to other areas of the network. The ultimate purpose of these systems is to divert attention from more valuable resources and to gather as much information about an attack as possible. A tarpit is a type of honeypot designed to provide a very slow connection to the hacker so that the attack can be analyzed.
Cloud Computing
Cloud computing is all the rage these days, and it comes in many forms. The basic idea of cloud computing is to make resources available in a web-based data center so the resources can be accessed from anywhere. When a company pays another company to host and manage this environment, we call it a public cloud solution. When companies host this environment themselves, we call it a private cloud solution.
There is trade-off when a decision must be made between the two architectures. The private solution provides the most control over the safety of your data but also requires the staff and the knowledge to deploy, manage, and secure the solution. A public cloud puts your data’s safety in the hands of a third party, but that party is often more capable and knowledgeable about protecting data in this environment and managing the cloud environment.
When a public solution is selected various levels of service can be purchased. Some of these levels include

Infrastructure as a service (IaaS) involves the vendor providing the hardware platform or data center and the company installing and managing its own operating systems and application systems. The vendor simply provides access to the data center and maintains that access.
Platform as a service (PaaS) involves the vendor providing the hardware platform or data center and the software running on the platform. This includes the operating systems and infrastructure software. The company is still involved in managing the system.
Software as a service (SaaS) involves the vendor providing the entire solution. This includes the operating system, infrastructure software, and the application. It might provide you with an email system, for example, whereby the vendor hosts and manages everything for you.
Figure 3-28 shows the relationship of these services to one another.
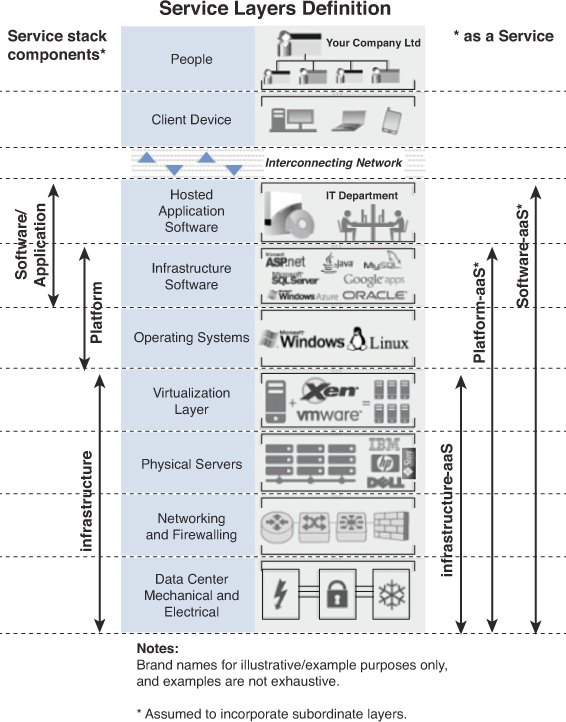
Endpoint Security
Endpoint security is field of security that attempts to protect individual systems in a network by staying in constant contact with these individual systems from a central location. It typically works on a client server model in that each system will have software that communicates with the software on the central server. The functionality provided can vary.
In its simplest form this incudes monitoring and automatic updating and configuration of security patches and personal firewall settings. In more advanced systems it might include an examination of the system each time it connects to the network. This examination would ensure that all security patches are up to date and in even more advanced scenarios it could automatically provide remediation to the computer. In either case the computer would not be allowed to connect to the network until the problem is resolved, either manually or automatically.
Network Types
So far we have discussed network topologies and technologies, so now let’s look at a third way to describe networks: network type. Network type refers to the scope of the network. Is it a LAN or a WAN? Is it a part of the internal network, or is it an extranet? This section discusses and differentiates all of these network types.
LAN
First let’s talk about what makes a local area network (LAN) local. Although classically we think of a LAN as a network located in one location, such as a single office, referring to a LAN as a group of systems that are connected with a fast connection is more correct. For purposes of this discussion, that is any connection over 10 Mbps.
That might not seem very fast to you, but it is when compared to a wide area connection (WAN). Even a T1 connection is only 1.544 Mbps. Using this as our yardstick, if a single campus network has a WAN connection between two buildings, then the two networks are considered two LANs rather than a single LAN. In most cases, however, networks in a single campus are typically NOT connected with a WAN connection, which is why usually you hear that a LAN defined as a network in a single location.
Intranet
Within the boundaries of a single LAN, there can be subdivisions for security purposes. The LAN might be divided into an intranet and an extranet. The intranet is the internal network of the enterprise. It would be considered a trusted network and typically houses any sensitive information and systems and should receive maximum protection with firewalls and strong authentication mechanisms.
Extranet
An extranet is a network logically separate from the intranet where resources that will be accessed from the outside world are made available. Access might be granted to customers, business partners, and the public in general. All traffic between this network and the intranet should be closely monitored and securely controlled. Nothing of a sensitive nature should be placed in the extranet.
MAN
A Metropolitan Area Network (MAN) is a type of LAN that encompasses a large area such as the downtown of a city. In many cases it is a backbone that is provided for local area networks to hook into. Three technologies are usually used in a MAN:
Fiber Distributed Data Interface (FDDI)
Synchronous Optical Networks (SONET)
Metro Ethernet
FDDI and SONET rings, which both rely on fiber cabling, can span large areas, and businesses can connect to the rings using T1, fractional T1, or T3 connections. As you saw earlier, FDDI rings are a double ring with fault tolerance built in. SONET is also self-healing, meaning it has a double ring with a backup line if a line goes bad.
Metro Ethernet is the use of Ethernet technology over a wide area. It can be pure Ethernet or a combination of Ethernet and other technologies such as the ones mentioned in this section. Traditional Ethernet (the type used on a LAN) is less scalable. It is often combined with Multiple Protocol Label Switching (MPLS) technology, which is capable of carrying packets of various types, including Ethernet.
Less capable MANs often feed into MANs of higher capacity. Conceptually, you can divide the MAN architecture into three sections: customer, aggregation, and core layer. The customer section is the local loop that connects from the customer to the aggregation network, which then feeds into the high-speed core. The high-speed core connects the aggregation networks to one another.
WAN
Finally, wide area networks (WANs) are used to connect LANs and MANs together. Many technologies can be used for these connections. They vary in capacity and cost, and access to these networks is purchased from a telecommunications company. The ultimate WAN is the Internet, the global backbone to which all MANs and LANs are connected. However, not all WANs connect to the Internet because some are private dedicated links to which only the company paying for them have access. WAN technologies are discussed more fully in the next section.
WAN Technologies
Many different technologies have evolved for delivering WAN access to a LAN. They differ in capacity, availability, and, of course, cost. This section compares the various technologies.
T Lines
T carriers are dedicated lines to which the subscriber has private access and does not share with another customer. Customers can purchase an entire T1, or they can purchase a part of a T1 called a fractional T1. T1 lines consist of 24 channels, each capable of 64 Kbps. This means a T1 has a total capacity of 1.544 Mbps. The T1 is split into channels through a process called time division multiplexing (TDM).
The drawback of a T1 is that the customer is buying the full capacity of the number of channels purchased, and any capacity left unused is wasted. This inflexibility and the high cost have made this option less appealing that it was at one time. The cost is a function of not only the number of channels but the distance of the line as well.
T carriers also come in larger increments as well. Table 3-7 shows a summary of T carriers and their capacity.

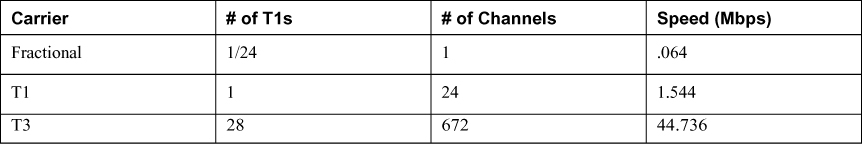
E Lines
In Europe, a similar technology to T-carrier lines exists called E carriers. With this technology 30 channels are bundled rather than 24. These technologies are not compatible, and the available sizes are a bit different. Table 3-8 shows some selected increments of E carriers.


OC Lines (SONET)
Synchronous Optical Networks (SONET) use fiber-based links that operate over lines measured in optical carrier (OC) transmission rates. These lines are defined by an integer value of the basic unit of rate. The basic OC-1 rate is 55.84 Mbps, and all other rates are multiples of that. For example, an OC3 yields 155.52 Mbps. Table 3-9 shows some these rates. Smaller increments such as OC-2 or OC-9 might be used by a company, whereas the larger pipes such as OC-3072 would be used by a service provider.

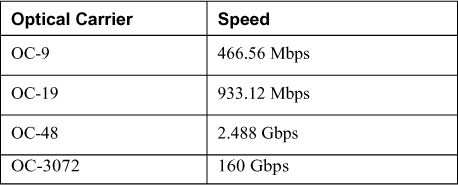
CSU/DSU
A discussion of WAN connections would not be complete without discussing a device that many customers connect to for their WAN connection. A Channel Service Unit/Data Service unit (CSU/DSU) connects a LAN to a WAN. This device performs a translation of the information from a format that is acceptable on the LAN to one that can be transmitted over the WAN connection.
The CSU/DSU is considered a Data Communications Equipment (DCE) device, and it provides an interface for the router, which is considered a Data Terminal Equipment (DTE) device. The CSU/DSU will most likely be owned by the Telco, but not always, and in some cases this functionality might be built into the interface of the router, making a separate device unnecessary.
Circuit-Switching Versus Packet-Switching
On the topic of WAN connections discussing the types of networks that these connections might pass through is also helpful. Some are circuit-switched, whereas others are packet switched. Circuit-switching networks (such as the telephone) establish a set path to the destination and only use that path for the entire communication. It results in a predictable operation with fixed delays. These networks usually carry voice-oriented traffic.
Packet-switching networks (such as the Internet or a LAN) establish an optimal path per-packet. This means each packet might go a different route to get to the destination. The traffic on these networks experiences performance bursts and the amount of delay can vary widely. These types of networks usually carry data-oriented traffic.
Frame Relay
Frame relay is a layer 2 protocol used for WAN connections. Therefore, when Ethernet traffic must traverse a frame relay link, the layer 2 header of the packet will be completely recreated to conform to frame relay. When the frame relay frame arrives at the destination, a new Ethernet layer 2 header will be placed on the packet for that portion of the network.
When frame relay connections are provisioned, the customer pays for a minimum amount of bandwidth called the Committed Information Rate (CIR). That will be the floor of performance. However, because frame relay is a packet-switched network using frame relay switches, the actual performance will vary based on conditions. Customers are sharing the network rather than having a dedicated line, such a T1 or ISDN line. So in many cases the actual performance will exceed the CIR.
ATM
Asynchronous Transfer Mode (ATM) is a cell-switching technology. It transfers fixed size cells of 53 bytes rather than packets, and after a path is established it uses the same path for the entire communication. The use of a fixed path makes performance more predictable, making it a good option for voice and video, which need such predictability. Where IP networks depend on the source and destination devices to ensure data is properly transmitted, this responsibility falls on the shoulder of the devices between the two in the ATM world.
ATM is used mostly by carriers and service providers for their backbones, but some companies have implemented their own ATM backbones and ATM switches. This allows them to make an ATM connection to the carrier, which can save money over connection with a T link because the ATM connection cost will be based on usage, unlike the fixed cost of the T1.
X.25
X.25 is somewhat like frame relay in that traffic moves through a packet-switching network. It charges by bandwidth used. The data is divided into 128-byte High-Level Data Link Control (HDLC) frames. It is, however, an older technology created in a time when noisy transmission lines were a big concern. Therefore, it has many error-checking mechanisms built in that make it very inefficient.
Switched Megabit Data Service
Switched Multimegabit Data Service (SMDS) is a connectionless, packet-switched technology that communicates across an established public network. It has been largely repacked with other WAN technologies. It can provide LAN-like performance to a WAN. It’s generally delivered over a SONET ring with a maximum effective service radius of around 30 miles.
Point-to-Point Protocol
Point-to-Point-Protocol (PPP) is a layer 2 protocol that performs framing and encapsulation of data across point-to-point connections. These are connections to the ISP where only the customer device and the ISP device reside on either end. It can encapsulate a number of different LAN protocols such as TCP/IP, IPX/SPX, and so on. It does this by using a Network Core Protocol (NCP) for each of the LAN protocols in use.
Along with the use of multiple NCPs, it uses a single Link Control Protocol (LCP) to establish the connection. PPP provides the ability to authenticate the connection between the devices using either Password Authentication Protocol (PAP) or Challenge Handshake Authentication Protocol (CHAP). Whereas PAP transmits the credentials in clear text, CHAP does NOT send the credentials across the line and is much safer.
High-Speed Serial Interface
High-Speed Serial Interface (HSSI) is one of the many physical implementations of a serial interface. Because these interfaces exist on devices, they are considered to operate at layer 1 of the OSI model. The Physical layer is the layer that is concerned with the signaling of the message and the interface between the sender or receiver and the medium. Examples of other serial interface are
• X.25
• V.35
• X.21
The HSSI interface is found on both routers and multiplexers and provides a connection to services such as frame relay and ATM. It operates at speeds up to 52 Mbps.
PSTN (POTS, PBX)
Probably the least attractive WAN connection available, at least from a performance standpoint, is the Public Switched Telephone Network (PSTN). Also referred to as the Plain Old Telephone Service (POTS) this is the circuit switched network that has been used for analog phone service for years and is now mostly a digital operation.
This network can be utilized using modems for an analog line or with ISDN for digital phone lines. Both of these options are discussed in more detail in the section “Remote Connection Technologies” because that is their main use. In some cases these connections may be used between offices but due to the poor performance, typically only as a backup solution in case a more capable option fails. These connections must be established each time they are used as opposed to “always on” solutions, such as cable or DSL.
PBX devices were discussed in the earlier section “Network Devices.”
VoIP
Although voice over the PSTN is circuit switched, voice can also be encapsulated in packets and sent across packet-switching networks. When this is done over an IP network, it is called Voice over IP (VoIP). Where circuit-switching networks use the Signaling System 7 (SS7) protocol to set up, control, and disconnect a call, VoIP uses Session Initiation Protocol (SIP) to break up the call sessions. In VoIP implementations, Quality of Service (QoS) is implemented to ensure that certain traffic (especially voice) is given preferential treatment over the network.
SIP is an application layer protocol that can operate over either TCP or UDP. Addressing is in terms of IP addresses, and the voice traffic uses the same network used for regular data. Because latency is always possible on these networks, protocols have been implemented to reduce the impact as this type of traffic is much more affected by delay. Applications such as voice and video need to have protocols and devices that can provide an isochronous network. Isochronous networks guarantee continuous bandwidth without interruption. It doesn’t use an internal clock source or start and stop bits. All bits are of equal importance and are anticipated to occur at regular intervals.
VoIP can be secured by talking the following measures
• Create a separate VLAN or subnet for the IP phones and prevent access to this VLAN by PCs.
• Deploy a VoIP -aware firewall at the perimeter.
• Ensure that all passwords related to VoIP are strong.
• Secure the network layer with IPsec.
Remote Connection Technologies
In many cases connections must be made to the main network from outside the network. The reasons for these connections are varied. In some cases it is for the purpose of allowing telecommuters to work on the network as if sitting in the office with all network resources available to them. In another instance it is for the purposes of managing network devices, whereas in others it could be to provide connections between small offices and the main office.
In this section some of these connection types are discussed along with some of the security measures that go hand in hand with them. These measures include both encryption mechanisms and authentication schemes.
Dial-up
A dial-up connection is one that uses the PSTN. If it is initiated over an analog phone line it requires a modem that converts the digital data to analog on the sending end with a modem on the receiving end converting it back to digital. These lines operate up to 56 Kbps.
Dialup connections can use either Serial Line Internet Protocol (SLIP) or Point to Point Protocol (PPP) at layer 2. SLIP is an older protocol that has been made obsolete by PPP. PPP provides authentication and multilink capability. The caller is authenticated by the remote access server. This authentication process can be centralized by using either a TACACS+ or RADIUS server. These servers are discussed more fully later in this section.
Some basic security measures that should be in place when using dial-up are
• Have the remote access server call back the initiating caller at a preset number. Do NOT allow call forwarding because it can be used to thwart this security measure.
• Modems should be set to answer after a set number of rings to thwart war dialers (more on them later).
• Consolidate the modems in one place for physical security, and disable modems not in use.
• Use the strongest possible authentication mechanisms.
If the connection is done over a digital line it can use Integrated Services Digital Network (ISDN). It also must be dialed up to make the connection but offers much more capability and the entire process is all digital. ISDN is discussed next.
ISDN
Integrated Services Digital Network (ISDN) is sometimes referred to as digital dialup. The really big difference between ISDN and analog dialup is the performance. ISDN can be provisioned in two ways:
Basic rate (BRI): Provides three channels—two B channels that provide 64 Kbps each and a D channel that is 16 Kbps for a total of 144 Kbps.
Primary Rate (PRI) can provide up to 23 B channels and a D channel for a total of 1.544 Mbps.
Although ISDN is typically now only used as a backup connection solution and many consider ISDN to be a dedicated connection and thus safe, attacks can be mounted against ISDN connections, including
Physical attacks: These are attacks by persons who are able to physically get to network equipment. With regard to ISDN, shared telecom closets can provide an access point. Physical security measures to follow are described in Chapter 11, “Physical (Environmental) Security.”
Router attacks: If a router can be convinced to accept an ISDN call from a rogue router it might allow an attacker access to the network. Routers should be configured to authenticate with one another before accepting call requests.
DSL
Digital Subscribers Line (DSL) is a very popular option that provides a high-speed connection from a home or small office to the ISP. Although it uses the existing phone lines it is an always-on connection. By using different frequencies than the voice transmissions over the same copper lines, talking on the phone and using the data network (Internet) at the same time is possible.
It also is many times faster than ISDN or dialup. It comes in several variants, some of which offer the same speed uploading and downloading (which is called symmetric service) while most offer better download performance than upload performance (called asymmetric service). Some possible versions are:
• Symmetric DSL (SDSL) usually provides from 192 Kbps to 1.1 Gbps in both directions. It is usually used by businesses.
• Asymmetric DSL (ADSL) usually provides uploads from 128Kbps–384 Kbps and downloads up to 768 Kbps. It is usually used in homes.
• High Bit-Rate DSL (HDSL) provides T1 speeds.
• Very High Bit-Rate DSL (VDSL) is capable of supporting HDTV and VoIP.
Unlike cable connections, DSL connections are dedicated links, but there are still security issues to consider. The PCs that are used to access the DSL line should be set with the following options in Internet Options.
• Check for publisher’s certificate revocation.
• Enable memory protection to help mitigate online attacks.
• Enable SmartScreen Filter.
• Use SSL 3.0.
• Use TLS 1.0.
• Warn about certificate address mismatch.
• Warn if POST submittal is redirected to a zone that does not permit posts.
Another issue with DSL is the fact it is always connected. This means that the PC typically keeps the same IP address. A static IP address provides a fixed target for the attacker. Therefore, taking measures such as network address translation helps to hide the true IP address of the PC to the outside world.
Cable
Getting connections to the ISP using the same cabling system used to deliver cable TV is also possible. Cable modems can provide up to 50 Mbps over the coaxial cabling used for cable TV. Cable modems conform to the Data-Over-Cable Service Interface Specification (DOCSIS) standard.
A security and performance concern with cable modems is that each customer is on a shared line with neighbors. This means performance varies with the time of day and congestion and the data is traveling over a shared medium. For this reason, many cable companies now encrypt these transmissions.
VPN
Virtual Private Network (VPN) connections are those that use an untrusted carrier network but provide protection of the information through strong authentication protocols and encryption mechanisms. Although we typically use the most untrusted network, the Internet as the classic example, and most VPNs do travel through the Internet, they can be used with interior networks as well whenever traffic needs to be protected from prying eyes.
When discussing VPN connections, many new to the subject become confused by the number and type of protocols involved. Let’s break down what protocols are required, which are optional, and how they all play together. Recall how the process of encapsulation works. Earlier we discussed this concept when we talked of packet creation and in that context we applied it to how one layer of the OSI model “wraps around” or encapsulates the other data already created at the other layers.
In VPN operations entire protocols wrap around other protocols (a process called encapsulation). They include
• A LAN protocol (required)
• A remote access or line protocol (required)
• An authentication protocol (optional)
• An encryption protocol (optional)
Let’s start with the original packet before it is sent across the VPN. This is a LAN packet, probably a TCP/IP packet. The change that will be made to this packet is it will be wrapped in a line or remote access protocol. This protocol’s only job is to carry the TCP/IP packet still fully intact across the line and then, just like a ferry boat drops a car at the other side of a river, it de-encapsulates the original packet and delivers it to the destination LAN unchanged.
Several of these remote access or line protocols are available. Among them are
• Point-to-Point-Tunneling Protocol (PPTP)
• Layer 2 Tunneling Protocol (L2TP)
PPTP is a Microsoft protocol based on PPP. It uses built-in Microsoft Point-to-Point encryption and can use a number of authentication methods, including CHAP, MS-CHAP. and EAP-TLS. One shortcoming of PPTP is that it only works on IP-based networks. If a WAN connection is in use that is not IP-based, L2TP must be used.
MS-CHAP comes in two versions. Both versions can be susceptible to password attacks. Version 1 is inherently insecure and should be avoided. Version 2 is much safer but can still suffer brute-force attacks on the password, although such attacks usually take up to 23 hours to crack the password. Moreover, the Microsoft Point-to-Point Encryption (MPPE) used with MS-CHAP can suffer attacks on the RC4 algorithm on which it is based. Although PPTP is a better solution it also has been shown to have known vulnerabilities related to the PPP authentication protocols used and is no longer recommended by Microsoft.
Although EAP-TLS is superior to both MSCHAP and PPTP, its deployment requires a public key infrastructure (PKI), which is often not within the technical capabilities of the network team or the resources to maintain it are not available.
L2TP is a newer protocol that operates at layer 2 of the OSI model. It can use various authentication mechanisms such as PPTP can but does not provide any encryption. It is typically used with IPSec, a very strong encryption mechanism.
With PPTP, the encryption is included, and the only remaining choice to be made is the authentication protocol. These authentication protocols are discussed later in the section “Remote Authentication Protocols.”
With L2TP, both encryption and authentication protocols, if desired, must be added. IPSec can provide encryption, data integrity, and system-based authentication, which makes it a flexible and capable option. By implementing certain parts of the IPsec suite, these features can be used or not.
IPsec is actually a suite of protocols in the same way that TCP/IP is. It includes the following components:
• Authentication Header (AH): Provides data integrity, data origin authentication, and protection from replay attacks.
• Encapsulating Security Payload (ESP): Provides all that AH does as well as data confidentiality.
• Internet Security Association and Key Management Protocol (ISAKMP): Handles the creation of a security association for the session and the exchange of keys.
• Internet Key Exchange (IKE), also sometimes referred to as IPsec Key Exchange: Provides the authentication material used to create the keys exchanged by ISAKMP during peer authentication. This was proposed to be performed by a protocol called Oakley that relied on the Diffie-Hellman algorithm, but Oakley been superseded by IKE.
You can find more information on IPsec in Chapter 6, “Cryptography.”
IPsec is a framework, which means it does not specify many of the components used with it. These components must be identified in the configuration, and they must match for the two ends to successfully create the required security association that must be in place before any data is transferred. The selections that must be made are:
• The encryption algorithm (encrypts the data)
• The hashing algorithm (ensures the data has not been altered and verifies its origin)
• The mode (tunnel or transport)
• The protocol (AH, ESP, or both)
All of these settings must match on both ends of the connection. It is not possible for the systems to select these on the fly. They must be preconfigured correctly to match.
When the tunnel is configured in tunnel mode, the tunnel exists only between the two gateways but all traffic that passes through the tunnel is protected. This is normally used to protect all traffic between two offices. The security association (SA) is between the gateways between the offices. This is the type of connection that would be called a site-to-site VPN.
The SA between the two endpoints is made up of the security parameter index (SPI) and the AH/ESP combination. The SPI, a value contained in each IPsec header, help the devices maintain the relationship between each SA (of which there could be several happening at once) and the security parameters (also called the transform set) used for each SA.
Each session has a unique session value which help to prevent:
• Reverse engineering
• Content modification
• Factoring attacks (the attacker tries all the combinations of numbers that can be used with the algorithm to decrypt ciphertext)
With respect to authenticating the connection, the keys can be pre-shared or derived form a Public Key Infrastructure (PKI). A PKI creates public/private key pair that is associated with individual users and computers that use a certificate. These key pairs are used in the place of pre-shared keys in that case. Certificates can also be used that are not derived from a PKI.
In transport mode, the SA is either between two end stations or an end station and a gateway or remote access server. In this mode, the tunnel extends from computer to computer or from computer to gateway. This is the type of connection that would be for a remote access VPN. This is but one application of IPsec. It is also used in other applications such as a General Packet Radio Service (GPRS) VPN solution for devices using a 2G cell phone network.
When the communication is from gateway to gateway or host to gateway, either transport or tunnel mode may be used. If the communication is computer to computer, the tunnel must be in must be transport mode. If the tunnel is configured in transport mode from gateway to host, the gateway must operate as a host.
The most effective attack against IPsec VPN is a man-in-the-middle attack. In this attack the attacker proceeds through the security negotiation phase until the key negotiation when the victim reveals its identity. In a well-implemented system, the attacker will fail when the attacker cannot likewise prove his identity.
RADIUS and TACACS
When users are making connections to the network through a variety of mechanisms, they should be authenticated first. These users could be accessing the network through
• Dial-up remote access servers
• VPN access servers
• Wireless Access Points
• Security-enabled switches
At one time each of these access devices would perform the authentication process locally on the device. The administrators would need to ensure that all remote access policies and settings were consistent across them all. When a password required changing, it had to be done on all devices.
Remote Authentication Dial In User Service (RADIUS) and Terminal Access Controller Access-Control System Plus (TACACS+) are networking protocols that provide centralized authentication and authorization. These services can be run at a central location, and all the access devices (AP, remote access, VPN, and so on) can be made clients of the server. Whenever authentication occurs, the TACACS+ or RADIUS server performs the authentication and authorization. This provides one location to manage the remote access policies and passwords for the network. Another advantage of using these systems is that the audit and access information (logs) are not kept on the access server.
TACACS and TACACS+ are Cisco proprietary services that operate in Cisco devices, whereas RADIUS is a standard defined in RFC 2138. Cisco has implemented several versions of TACACS over time. It went from TACACS to XTACACS to the latest version TACACS +. The latest version provides authentication, accounting, and authorization, which is why it is sometimes referred to as an AAA service. TACACS+ employs tokens for two-factor, dynamic password authentication. It also allows users to change their passwords.
RADIUS is designed to provide a framework that includes three components. The supplicant is the device seeking authentication. The authenticator is the device to which they are attempting to connect (AP, switch, remote access server), and the RADIUS server is the authentication server. With regard to RADIUS, the device seeking entry is not the RADIUS client. The authenticating server is the RADIUS server, and the authenticator (AP, switch, remote access server) is the RADIUS client.
In some cases a RADIUS server can be the client of another RADIUS server. In that case the RADIUS server acts as a proxy client for its RADIUS clients.
Diameter is another authentication protocol based on RADIUS and is not compatible with RADIUS. Diameter has a much larger set of attribute-value pairs (AVPs) than RADIUS, allowing more functionality and services to communicate, but has not been widely adopted.
Remote Authentication Protocols
Earlier we said that one of the protocol choices that must be made when provisioning a remote access solution is the authentication protocol. This section discusses some of the most important of those protocols.
Password Authentication Protocol (PAP) provides authentication but the credentials are sent in clear text and can be read with a sniffer.
Challenge Handshake Authentication Protocol (CHAP) solves the clear-text problem by operating without sending the credentials across the link. The server sends the client a set of random text called a challenge. The client encrypts the text with the password and sends it back. The server then decrypts it with the same password and compares the result with what was sent originally. If the results match, then the server can be assured that the user or system possesses the correct password without ever needing to send it across the untrusted network.
Extensible Authentication Protocol (EAP) is not a single protocol but a framework for port-based access control that uses the same three components that are used in RADIUS. A wide variety of these implementations can use all sorts of authentication mechanisms, including certificates, a PKI, or even simple passwords.
Telnet
Telnet is a remote access protocol used to connect to a device for the purpose of executing commands on the device. It can be used to access servers, routers, switches, and many other devices for the purpose of managing them. Telnet is not considered a secure remote management protocol because like another protocol used with UNIX-based systems, rlogin, it transmits all information including the authentication process in clear text. Alternatives such as Secure Shell (SSH) have been adopted to perform the same function while providing encryption. Telnet and rlogin connections are connection-oriented so they use TCP as the transport protocol.
TLS/SSL
Transport Layer Security/Secure Sockets layer (TLS/SSL) is another option for creating secure connections to servers. It works at the Application layer of the OSI model. It is used mainly to protect HTTP traffic or web servers. Its functionality is embedded in most browsers, and its use typically requires no action on the part of the user. It is widely used to secure Internet transactions. It can be implemented in two ways:
SSL portal VPN, in which a user has a single SSL connection used to access multiple services on the web server. After being authenticated the user is provided a page that acts as a portal to other services.
SSL tunnel VPN uses an SSL tunnel to access services on a server that is not a web server. It uses custom programming to provide access to non-web services through a web browser.
TLS and SSL are very similar but not the same. TLS 1.0 is based on the SSL 3.0 specification but they are not operationally compatible. Both implement confidentiality, authentication, and integrity above the Transport layer. The server is always authenticated and optionally the client also can be. SSL v2 must be used for client-side authentication. When configuring SSL a session key length must be designated. The two options are 40 bit and 128 bit. It prevents man-in-the middle attacks by using self-signed certificates to authenticate the server public key.
Multimedia Collaboration
In today’s modern enterprises the sharing of multimedia during both web presentations or meetings and instant messaging programs has exploded. Note that not all collaboration tools and products are created equally in regard to the security. Many were built with an emphasis on ease of use rather than security. This is a key issue to consider when choosing a product. For both the presenter and the recipient the following security requirements should be met:
• Data confidentiality
• Origin authentication
• Identity confidentiality
• Data integrity
• Non-repudiation of receipt
• Repudiation of transmission
• Non-repudiation of transmission
• Availability to present
• Availability to receive
Wireless Networks
Perhaps the area of the network that keeps more administrators awake at night is the wireless portion of the network. In the early days of 802.11 WLAN deployments many chose to simply not implement wireless for fear of the security holes it creates. However, it became apparent that not only did users demand this, but in some cases users were bringing home APs to work and hooking them up and suddenly there was a wireless network!
Today WLAN security has evolved to the point that security is no longer a valid reason to avoid wireless. This section offers a look at the protocols used in wireless, the methods used to convert the data into radio waves, the various topologies in which WLANs can be deployed, and security measures that should be taken.
FHSS, DSSS, OFDM, FDMA, TDMA, CDMA, OFDMA, and GSM
When data leaves an Ethernet NIC and is sent out on the network, the ones and zeros that constitute the data are represented with different electric voltages. In wireless this information must be represented in radio waves. A number of different methods exist for performing this operation, which is called modulation. You should also understand some additional terms to talk intelligently about wireless. This section defines a number of terms to provide a background for the discussion found in the balance of this section. The first section covers techniques used in WLAN and the second covers techniques used in cellular networking.
802.11 Techniques
Frequency Hopping Spread Spectrum (FHSS) is one of two technologies (along with DSSS) that were a part of the original 802.11 standard. It is unique in that it changes frequencies or channels every few seconds in a set pattern that both transmitter and receiver know. This is not a security measure because the patterns are well known, although it does make capturing the traffic difficult. It helps avoid inference by only occasionally using a frequency where the inference is present. Later amendments to the 802.11 standard did not include this technology. It can attain up to 2 Mbps.
Direct Sequence Spread Spectrum (DSSS) is one of two technologies (along with FHSS) that were a part of the original 802.11 standard. This is the modulation technique used in 802.11b. The modulation technique used in wireless has a huge impact on throughput. In the case of DSSS it spreads the transmission across the spectrum at the same time as opposed to hopping from one to another as in FHSS. This allows it to attain up to 11 Mbps.
Orthogonal Frequency Division Multiplexing (OFDM) is a more advanced technique of modulation in where a large number of closely spaced orthogonal sub-carrier signals are used to carry the data on several parallel data streams. It is used in 802.11a and 802.11g. It makes speed up to 54 Mbps possible.
Cellular or Mobile Wireless Techniques
Frequency Division Multiple Access (FDMA) is one of the modulation techniques used in cellular wireless networks. It divides the frequency range into bands and assigns a band to each subscriber. This was used in 1G cellular networks.
Time Division Multiple Access (TDMA) increases the speed over FDMA by dividing the channels into time slots and assigning slots to calls. This also helps to prevent eavesdropping in calls.
Code Division Multiple Access (CDMA) assigns a unique code to each call or transmission and spreads the data across the spectrum, allowing a call to make use of all frequencies.
Orthogonal Frequency Division Multiple Access (OFDMA) takes FDMA a step further by subdividing the frequencies into subchannels. This is the technique required by 4G devices.
Global System Mobile (GSM) is a type of cell phone that contains a Subscriber Identity Module (SIM) chip. These chips contain all the information about the subscriber and must be present in the phone for it to function. One of the dangers with these phones is cell phone cloning, a process where copies of the SIM chip are made, allowing another user to make calls as the original user. Secret key cryptography is used (using a common secret key) when authentication is performed between the phone and the network.
WLAN Structure
Before we can discuss 802.11 wireless, which has come to be known as WLAN, we need to discuss the components and the structure of a WLAN. This section covers basic terms and concepts.
Access Point
An access point (AP) is wireless transmitter and receiver that hooks into the wired portion of the network and provides an access point to this network for wireless devices. In some cases they are simply wireless switches, and in other cases they are also routers. Early APs were devices with all the functionality built into each device, but increasingly these “fat” or intelligent APs are being replaced with “thin” APs that are really only antennas that hook back into a central system called a controller.
SSID
The service set identifier (SSID) is a name or value assigned to identify the WLAN from other WLANs. The SSID can either be broadcast by the AP as is done in a free hot spot or it can be hidden. When it is hidden, a wireless station will have to be configured with a profile that includes the SSID to connect. Although some view hiding the SSID as a security measure, it is not an effective measure because hiding the SSID only removes one type of frame, the beacon frame, while it still exists in other frame types and can be easily learned by sniffing the wireless network.
Infrastructure Mode versus Ad hoc Mode
In most cases a WLAN includes at least one AP. When an AP is present the WLAN is operating in Infrastructure mode. In this mode all transmissions between stations go through the AP, and no direct communication between stations occurs. In Ad Hoc mode, there is no AP, and the stations communicate directly with one another.
WLAN Standards
The original 802.11 wireless standard has been amended a number of times to add features and functionality. This section discusses these amendments, which are sometimes referred to as standards although they really are amendments to the original standard. The original 802.11 standard specified the use of either FHSS or DSSS and supported operations in the 2.4 GHz frequency range at speeds of 1 Mbps and 2 Mbps.

802.11a
The first amendment to the standard was 802.11a. This standard called for the use of OFDM. Because that would require hardware upgrades to existing equipment, this standard saw limited adoption for some time. It operates in a different frequency than 802.11 (5 GHz) and by using OFDM supports speeds up to 54 Mbps.
802.11b
The 802.11b amendment dropped support for FHSS and enabled an increase of speed to 11 Mbps. It was widely adopted because it both operates in the same frequency as 802.11 and is backward compatible with it and can coexist in the same WLAN.
802.11f
The 802.11f amendment addressed problems introduced when wireless clients roam from one AP to another. This causes the station to need to reauthenticate with the new AP, which in some cases introduced a delay that would break the application connection. This amendment improves the sharing of authentication information between APs.
802.11g
The 802.11g amendment added support for OFDM, which made it capable of 54 Mbps. This also operates in the 2.4 GHz frequency so it is backward compatible with both 802.11 and 802.11b. While just as fast as 802.11a, one reason many switched to 802.11a is that the 5 GHz band is much less crowded than the 2.4 GHz band.
The 802.11n standard uses several newer concepts to achieve up to 650 Mbps. It does these using channels that are 40 MHz wide, using multiple antennas that allow for up to four spatial streams at a time (a feature called Multiple Input Multiple Output or MIMO). It can be used in both the 2.4 GHz and 5.0 GHz bands but performs best in a pure 5.0 GHz network because in that case it does not need to implement mechanisms that allow it to coexist with 802.11b and 802.11g devices. These mechanisms slow the performance.
Bluetooth
Bluetooth is a wireless technology that is used to create Personal Area Networks (PANs). These are simply short-range connections that are between devices and peripherals, such as headphones. It operates in the 2.4 GHz frequency at speeds of 1 Mbps to 3 Mbps at a distance of up to 10 meters.
Several attacks can take advantage of Bluetooth technology. Bluejacking is when an unsolicited message is sent to a Bluetooth-enabled device often for the purpose of adding a business card to the victim’s contact list. This can be prevented by placing the device in non-discoverable mode.
Bluesnarfing is the unauthorized access to a device using the Bluetooth connection. In this case the attacker is trying to access information on the device rather than send messages to the device.
Infrared
Finally, infrared is a short-distance wireless process that uses light rather than radio waves, in this case infrared light. It is used for short connections between devices that both have an infrared port. It operates up to 5 meters at speeds up to 4 Mbps and requires a direct line of sight between the devices. There is one infrared mode or protocol that can introduce security issues. The IrTran-P (image transfer) protocol is used in digital cameras and other digital image capture devices. All incoming files sent over IrTran-P are automatically accepted. Because incoming files might contain harmful programs, users should ensure that the files originate from a trustworthy source.
WLAN Security
To safely implement 802.11 wireless technologies you must understand all the methods used to secure a WLAN. In this section the most important measures are discussed including some measures that, although they are often referred to as security measures, provide no real security whatsoever.
WEP
Wired Equivalent Privacy (WEP) was the first security measure used with 802.11. It was specified as the algorithm in the original specification. It can be used to both authenticate a device and encrypt the information between the AP and the device. The problem with WEP is that it implements the RC4 encryption algorithm in a way that allows a hacker to crack the encryption. It also was found that the mechanism designed to guarantee the integrity of data (that the data has not changed) was inadequate and that it was possible for the data to be changed and for this fact to go undetected.
WEP is implemented with a secret key or password that is configured on the AP, and any station will need that password to connect. Above and beyond the problem with the implementation of the RC4 algorithm, it is never good security for all devices to share the same password in this way.
WPA
To address the widespread concern with the inadequacy of WEP, the Wi-Fi Alliance, a group of manufacturers that promotes interoperability, created an alternative mechanism called Wi-Fi Protected Access (WPA) that is designed to improve on WEP. There are four types of WPA but first let’s talk about how the original version improves over WEP.
First, WPA uses the Temporal Key Integrity Protocol (TKIP) for encryption, which generates a new key for each packet. Second, the integrity check used with WEP is able to detect any changes to the data. WPA uses a message integrity check algorithm called Michael to verify the integrity of the packets. There are two versions of WPA (covered in the section “Personal versus Enterprise”).
Some legacy devices might only support WPA. You should always check with a device’s manufacturer to find out whether a security patch has been released that allows for WPA2 support.
WPA2
WPA2 is an improvement over WPA. WPA2 uses Counter Cipher Mode with Block Chaining Message Authentication Code Protocol (CCMP) based on Advanced Encryption Standard (AES), rather than TKIP. AES is a much stronger method and is required for Federal Information Processing Standards (FIPS)-compliant transmissions. There also two versions of WPA2 (covered in the next section).
Personal versus Enterprise
Both WPA and WPA2 come in Enterprise and Personal versions. The Enterprise versions require the use of an authentication server, typically a RADIUS server. The Personal versions do not and use passwords configured on the AP and the stations. Table 3-10 provides a quick overview of WPA and WPA2.

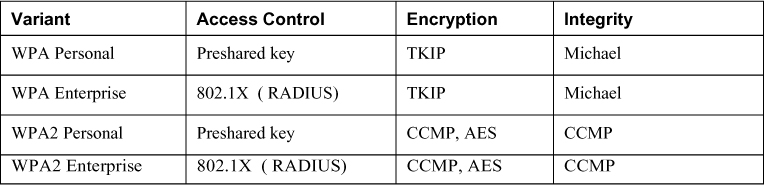
SSID Broadcast
Issues surrounding the SSID broadcast were covered in the section “WLAN Structure” earlier in this chapter.
MAC Filter
Another commonly discussed security measure that can be taken is to create a list of allowed MAC addresses on the AP. When this is done, only the devices with MAC addresses on the list can make a connection to the AP. Although on the surface this might seem like a good security measure, in fact a hacker can easily use a sniffer to learn the MAC addresses of devices that have successfully authenticated. Then by changing the MAC address on his device to one that is on the list he can gain entry.
MAC filters can also be configured to deny access to certain devices. The limiting factor in this method is that only the devices with the denied MAC addresses are specifically denied access. All other connections will be allowed.
Satellites
Satellites can be used to provide TV service and have for some time but now they can also be used to deliver Internet access to homes and businesses. The connection is two-way rather than one-way as is done with TV service. This is typically done using microwave technology. In most cases, the downloads come from the satellite signals, whereas the uploads occur through a ground line. Microwave technology can also be used for terrestrial transmission, which means ground station to ground station rather than satellite to ground. Satellite connections are very slow but are useful in remote locations where no other solution is available.
Network Threats
Before you can address network security threats you must be aware of them, understand how they work, and know the measure to take to prevent the attacks from succeeding. This section covers a wide variety of attack types along with measures that should be taken to prevent them from occurring.
Cabling
Although it’s true that a cabled network is easier to secure from eavesdropping than a wireless network, you must still be aware of some security issues. You should also understand some general behaviors of cabling that affect performance and ultimately can affect availability. As you might recall, maintaining availability to the network is also one of the goals of CIA, which is explained in Chapter 2, “Access Control.” Therefore, performance characteristics of cabling that can impact availability are also discussed.
Noise
Noise is a term used to cover several types of interference than can be introduced to the cable that causes problems. This can be from large electrical motors, other computers, lighting, and other sources. This noise combines with the data signals (packets) on the line and distorts the signal. When even a single bit in a transmission is misread (read as a 1 when it should be a zero or vice versa), nonsense data is received and retransmissions must occur. Retransmissions lead to lower throughput and in some cases no throughput whatsoever.
In any case where this becomes a problem, the simplest way to mitigate the problem is use shielded cabling. In cases where the noise is still present, locating the specific source and taking measures to remove it (or least the interference it is generating) from the environment might be necessary.
Attenuation
Attenuation is the weakening of the signal as it travels down the cable and meets resistance. In the discussion on cabling earlier in this chapter, you learned that all cables have a recommended maximum length. When you use a cable that is longer than its recommended length, attenuation weakens the signal to the point it cannot be read correctly, resulting in the same problem that is the end result of noise. The data must be sent again lowering throughput.
The solution to this problem is in design. Follow the length recommendations listed in the section on cables earlier in this chapter with any type of cabling. This includes coaxial, twisted pair, and fiberoptic. All types have maximum lengths that should not be exceeded without risking attenuation.
Crosstalk
Crosstalk is a behavior that can occur whenever individual wires within a cable are run parallel to one another. Crosstalk occurs when the signals from the two wires (or more) interfere with one another and distort the transmission. Cables such as twisted-pair cables would suffer from this were the cables not twisted as they are. The twisting prevents the crosstalk from occurring.
Eavesdropping
Although cabling is a bounded media and much easier to secure than wireless, eavesdropping can still occur. All cabling that depends on electrical voltages, such as coaxial and twisted pair, can be tapped or monitored with the right equipment. The least susceptible to eavesdropping (although not completely immune) is fiberoptic cabling because it doesn’t use electrical voltages, but rather light waves. In any situation where eavesdropping is a concern, using fiberoptic cabling can be a measure that will at least drastically raise the difficulty of eavesdropping. The real solution is ensuring physical security of the cabling. The cable runs should not be out in the open and available.
ICMP Attacks
Earlier in this chapter you learned about Internet Control Message Protocol (ICMP), one of the protocols in the TCP/IP suite. This protocol is used by devices to send error messages to sending devices when transmission problems occur and is also used when either the ping command or the traceroute command is used for troubleshooting. Like many tools and utilities that were created for good purposes this protocol can also be used by attackers who take advantage of its functionality.
This section covers ICMP-based attacks. One of the ways to prevent ICMP-based attacks is disallow its use by blocking the protocol number for ICMP, which is 1. Many firewall products also have the ability to only block certain types of ICMP messages as opposed to prohibiting its use entirely. Some of these problematic ICMP message types are discussed in this section as well.
Ping of Death
The Ping of Death is an attack that takes advantage of the normal behavior of devices that receive oversized ICMP packets. ICMP packets are normally a predictable 65,536 bytes in length. Hackers have learned how to insert additional data into ICMP packets. The Ping of Death attack sends several of these oversized packets, which can cause the victim system to be unstable at the least and possibly freeze up. That results in a denial-of-service attack because it makes the target system less able or even unable to perform its normal function in the network.
Smurf
The Smurf attack is also a denial-of-service attack that uses a type of ping packet called an ICMP ECHO REQUEST. This is an example of a Distributed Denial of Service (DDoS) attack in that the perpetuator enlists the aid of other machines in the network.
When a system receives an ICMP ECHO REQUEST packet it attempts to answer this request with an ICMP ECHO REPLY packet (usually four times by default). Normally this reply is sent to a single sending system. In this attack, the ECHO REQUEST has its destination address set to the network broadcast address of the network in which the target system resides and the source address is set to the target system. When every system in the network replies to the request it overwhelms the target device cause it to freeze or crash.
Fraggle
Although not really an ICMP attack because it uses UDP, the Fraggle attack is a DDoS attack with the same goal and method as the Smurf attack. In this attack an attacker sends a large amount of UDP echo traffic to an IP broadcast address, all of it having a fake source address, which will, of course, be the target system. When all systems in the network reply the target is overwhelmed.
ICMP Redirect
One of the many types of error messages that ICMP uses is called an ICMP redirect or an ICMP Packet type 5. ICMP redirects are used by routers to specify better routing paths out of one network. When it does this it changes the path that the packet will take.
By crafting ICMP redirect packets, the attacker alters the route table of the host that receives the redirect message. This changes the way packets are routed in the network to his advantage. After its routing table is altered, the host will continue to use the path for 10 minutes. For this reason ICMP redirect packets might be one of the types you might want to disallow on the firewall.
Ping Scanning
ICMP can be used to scan the network for live or active IP addresses. This attack basically pings every IP address and keeps track of which IP addresses respond to the ping. This attack is usually accompanied or followed by a port scan, covered later in this chapter.
DNS Attacks
As you might recall in the discussion of DNS earlier in this chapter, DNS resolves computer and domain names to IP addresses. It is a vital service to the network and for that reason multiple DNS servers are always recommended for fault tolerance. DNS servers are a favorite target of DoS and DDoS attacks because of the mayhem taking them down causes.
DNS servers also can be used to divert traffic to the attacker by altering DNS records. In this section all type of DNS attacks are covered along with practices that can eliminate or mitigate the effect of these attacks.
DNS Cache Poisoning
DNS clients send requests for name-to-IP address resolution (called queries) to a DNS server. The search for the IP address that goes with a computer or domain name usually starts with a local DNS server that is not authoritative for the DNS domain in which the requested computer or website resides. When this occurs the local DNS server makes a request of the DNS server that does hold the record in question. After the local DNS server receives the answer it returns it to the local DNS client. After this the local DNS server maintains that record in its DNS cache for a period called the Time to Live (TTL), which is usually an hour but can vary.
In a DNS cache poisoning attack, the attacker attempts to refresh or update that record when it expires with a different address than the correct address. If he can convince the DNS server to accept this refresh, the local DNS server will then be responding to client requests for that computer with the address inserted by the attacker. Typically the address they now receive is for a fake website that appears to look in every way like the site the client is requesting. The hacker can then harvest all the name and password combinations entered on his fake site.
To prevent this type of attack the DNS servers should be limited in the updates they accept. In most DNS software you can restrict the DNS servers from which a server will accept updates. This can help prevent the server from accepting these false updates.
DoS
DNS servers are a favorite target of Denial of Service (DoS) attacks. This is because the loss of DNS service in the network typically brings the network to a halt as many network services depend on its functioning. Any of the assorted type of DoS attacks discussed in this book can be targeted to DNS servers. For example, the ping of death might be the attack of choice.
DDoS
Any of the assorted DoS attacks can be amplified by the attacker by recruiting other devices to assist in the attack. Some examples of these attacks are the smurf and fraggle attacks (covered later).
In some cases the attacker might have used malware to install software on thousands of computers (called zombies) to which he sends commands at the given time, instructing all the devices to launch the attack. Not only does this amplify the attack but it also helps to hide the source of the attack because it appears to come from many places at once.
DNSSEC
One of the newer approaches to preventing DNS attacks is a stronger authentication mechanism called Domain Name System Security Extensions (DNSSEC). Many current implementations of DNS software contain this functionality. It uses digital signatures to validate the source of all messages to ensure they are not spoofed.
The problem with DNSSEC illustrates the classic tradeoff between security and simplicity. To deploy DNSSEC, a Public Key Infrastructure (PKI) must be built and maintained to issue, validate, and renew the public/private key pairs and certificates that must be issued to all the DNS servers. (PKI is covered more fully in Chapter 6, “Cryptography.”) Moreover, for complete security of DNS, all the DNS servers on the Internet would also need to participate, which complicates the situation further. The work on this continues today.
URL Hiding
An alternate and in some ways simpler way for an attacker to divert traffic to a fake website is a method called URL hiding. This attack takes advantage of the ability to embed URLs in web pages and email. The attacker might refer to the correct name of the website in the text of the webpage or email, but when he inserts the URL that goes with the link he inserts the URL for the fake site. The best protection against this issue is to ask users to not click links on unknown or untrusted websites.
Domain Grabbing
Domain grabbing occurs when individuals register a domain name of a well-known company before the company has the chance to do so. Then later the individuals hold the name hostage until the company becomes willing to pay to get the domain name. In some cases these same individuals monitor the renewal times for well-known websites and register the name before the company has chance to perform the renewal. Some practices that can help to prevent this are to register domain names for longer periods of time and to register all permutations of the chosen domain name (misspellings and so on).
Cybersquatting
When domain names are registered with no intent to use them but with intent to hold them hostage (as described in the preceding), it is called cybersquatting. The same practices to prevent domain grabbing are called for to prevent the company from becoming a victim of cybersquatting.
Email Attacks
One of the most popular avenues for attacks is a tool we all must use every day, email. In this section several attacks that use email as the vehicle are covered. In most cases the best way to prevent these attacks is user training and awareness because many of these attacks are based upon poor security practices on the part of the user.
Email Spoofing
Email spoofing is the process of sending an email that appears to come from one source when it really comes from another. It is made possible by altering the fields of email headers such as From, Return Path, and Reply-to. Its purpose is to convince the receiver to trust the message and reply to it with some sensitive information that the receiver would not have shared unless it was a trusted message.
Often this is one step in an attack designed to harvest usernames and passwords for banking or financial sites. This attack can be mitigated in several ways. One is SMTP authentication, which when enabled, disallows the sending of an email by a user that cannot authenticate with the sending server.
Another possible mitigation technique is to implement a Sender Policy Framework (SPF). An SPF is an email validation system that works by using DNS to determine whether an email sent by someone has been sent by a host sanctioned by that domain’s administrator. If it can’t be validated it is not delivered to the recipient’s box.
Spear Phishing
Phishing is a social engineering attack where a recipient is convinced to click on a link in an email that appears to go to a trusted site but in fact goes to the hacker’s site. This is used to harvest usernames and passwords.
Spear phishing is the process of foisting this attack on a specific person rather than a random set of people. The attack might be made more convincing by learning details about the person through social media that the email might reference to boosts its appearance of legitimacy.
Whaling
Just as spear phishing is a subset of phishing, whaling is a subset of spear phishing. It targets a single person and in the case of whaling, that person is someone of significance or importance. It might be a CEO, COO, or CTO, for example. The attack is based on the assumption that these people have more sensitive information to divulge.
Spam
No one enjoys the way our email boxes fill every day with unsolicited emails, usually trying to sell us something. In many cases we cause ourselves to receive this email by not paying close attention to all the details when we buy something or visit a site. When email is sent out on a mass basis that is not requested it is called spam.
Spam is more than an annoyance because it can clog email boxes and cause email servers to spend resources delivering it. Sending spam is illegal so many spammers try to hide the source of the spam by relaying through other corporations’ email servers. Not only does this practice hide the email’s true source, but it can cause the relaying company to get in trouble.
Today’s email servers have the ability to deny relaying to any email servers that you do not specify. This can prevent your email system from being used as a spamming mechanism. This type of relaying should be disallowed on your email servers.
Wireless Attacks
Wireless attacks are some of the hardest to prevent because of the nature of the medium. If you want to make the radio transmissions available to the users then you must make them available to anyone else in the area as well. Moreover there is no way to determine when someone is capturing your radio waves! You might be able to prevent someone from connecting to or becoming a wireless client on the network, but you can’t stop them from using a wireless sniffer to capture the packets. In this section some of the more common attacks are covered and some mitigation techniques are discussed as well.
Wardriving
Wardriving is the process of riding around with a wireless device connected to a high-power antenna searching for WLANs. It could be for the purpose of obtaining free Internet access, or it could be to identify any open networks vulnerable to an attack.
Warchalking
Warchalking is a practice that typically accompanies war driving. When a wardriver locates a WLAN he indicates in chalk on the sidewalk the SSID and the types of security used on the network. This activity has gone mostly online now as many sites are dedicated to compiling lists of found WLANs and their locations.
Remote Attacks
Although in a sense all attacks such as DoS attacks, DNS poisoning, port scanning, and ICMP attacks are remote in the sense they can be launched from outside the network, remote attacks can also be focused on remote access systems such as VPN servers or dialup servers. As security practices have evolved, these types of attacks have somewhat diminished.
Wardialing is not the threat that it once was simply because we don’t use modems and modem banks as much as we used to. In this attack, software programs attempt to dial large lists of phone numbers for the purpose of identifying numbers attached to modems. When a person or fax machine answers it records that fact, and when a modem answers it attempts to make a connection. If this connection is successful the hacker now has an entryway into the network.
Other Attacks
In this final section of this chapter some other attacks are covered that might not fall into any of the other categories discussed thus far.
SYN ACK Attacks
The SYN ACK attack takes advantage of the TCP three-way handshake, covered in the section “Transport Layer” earlier in this chapter.
In this attack, the hacker sends a large number of packets with the SYN flag set, which causes the receiving computer to set aside memory for each ACK packet it expects to receive in return. These packets never come and at some point the resources of the receiving computer are exhausted, making this a form of DoS attack.
Session Hijacking
In a session highjacking attack, the hacker attempts to place himself in the middle of an active conversation between two computers for the purpose of taking over the session of one of the two computers, thus receiving all data sent to that computer. A couple of tools can be used for this attack. Juggernaut and the Hunt Project allow the attacker to spy on the TCP session between the computers. Then he uses some sort of DoS attack to remove one of the two computers from the network while spoofing the IP address of that computer and replacing that computer in the conversation. This results in the hacker receiving all traffic that was originally intended for the computer that suffered the DoS attack.
Port Scanning
ICMP can also be used to scan the network for open ports. Open ports indicate services that might be running and listening on a device that might be susceptible to being used for an attack. This attack basically pings every address and port number combination and keeps track of which ports are open on each device as the pings are answered by open ports with listening services and not answered by closed ports.
Teardrop
A teardrop attack is a type of fragmentation attack. The Maximum Transmission Unit (MTU) of a section of the network might cause a packet to be broken up or fragmented, which requires the fragments to be reassembled when received. The hacker sends malformed fragments of packets that when reassembled by the receiver cause the receiver to crash or become unstable.
IP Address Spoofing
IP address spoofing is one of techniques used by hackers to hide their trail or to masquerade as another computer. The hacker alters the IP address as it appears in the packet. This can sometimes allow the packet to get through an ACL that is based on IP addresses. It also can be used to make a connection to a system that only trusts certain IP address or ranges of IP addresses.
Exam Preparation Tasks
Review All Key Topics
Review the most important topics in this chapter, noted with the Key Topics icon in the outer margin of the page. Table 3-11 lists a reference of these key topics and the page numbers on which each is found.
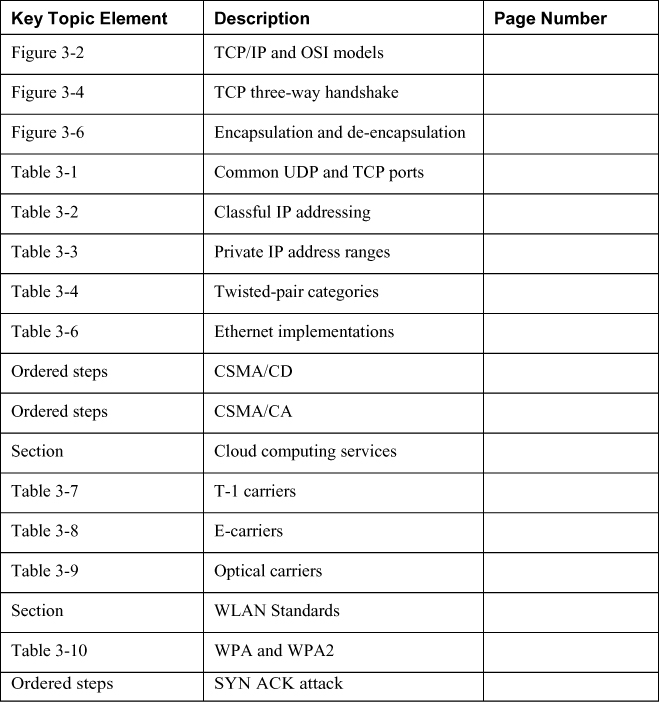
Define Key Terms
Define the following key terms from this chapter and check your answers in the glossary:
Open Systems Interconnect (OSI) model
Application layer
Presentation layer
Session layer
Transport layer (layer 4)
Network layer (layer 3)
Data Link layer (layer 2)
Physical layer (layer 1)
TCP/IP model
TCP three-way handshake
Internet Protocol (IP)
Internet Message Control Protocol (ICMP)
Internet Group Messaging Protocol (IGMP)
Address Resolution Protocol (ARP)
Private IP addresses
NAT
Media Access Control (MAC) addresses
Digital
Asynchronous transmission
Synchronous transmission
Baseband
Time Division Multiplexing (TDM)
Broadband
Frequency Division Multiplexing (FDM)
Unicast
Multicast
Broadcast
Coaxial
ThickNet
ThinNet
Twisted Pair
Radio Frequency Interference (RFI)
EMI
Fiberoptic
Single mode
Multi-mode
Ring
Bus
Star
Mesh
Hybrid
Ethernet
Token Ring
Fiber Distributed Data Interface (FDDI)
Carrier Sense Multiple Access Collision Detection (CSMA/CD)
Carrier Sense Multiple Access Collision Avoidance (CSMA/CA)
token passing
polling
Dynamic Host Configuration Protocol (DHCP)
DNS
File Transfer Protocol (FTP)
FTPS
Secure File Transfer Protocol (SFTP)
HTTP
Hypertext Transfer Protocol Secure (HTTPS)
S-HTTP
Internet Message Access Protocol (IMAP)
Network Address Translation (NAT)
Port Address Translation (PAT)
Post Office Protocol (POP)
Simple Mail Transfer Protocol (SMTP)
Simple Network Management Protocol (SNMP)
distance vector
link state
hybrid
Routing Internet Protocol (RIP)
Open Shortest Path First (OSPF)
Interior Gateway Protocol
Enhanced IGRP (EIGRP)
Virtual Router Redundancy Protocol (VRRP)
Intermediate system to Intermediate system (IS-IS)
Border Gateway Protocol (BGP)
patch panels
multiplexer
demultiplexer
hub
switches
VLANS
layer 3 switch
layer 4 switches
routers
Network Access Server (NAS)
firewall
packet filtering firewalls
stateful firewalls
proxy firewalls
circuit level proxies
SOCKS firewall
application-level proxies
dynamic packet filtering firewall
kernel proxy firewall
bastion host
dual-homed firewall
three legged firewall
DMZ
screened host
screened subnet
virtual firewalls
proxy firewall
Private branch exchange (PBX)
honeypots
honeynets
cloud computing
Infrastructure as a Service (IaaS)
LAN
intranet
extranet
Metropolitan Area Network (MAN)
Metro Ethernet
wide area networks (WANs)
T carriers
fractional T1
E carriers
Synchronous Optical Networks (SONET)
Channel Service Unit/Data Service unit (CSU/DSU)
circuit switching networks
packet switching networks
Asynchronous Transfer Mode (ATM)
X.25
Switched Multimegabit Data service (SMDS)
Point to Point Protocol (PPP)
HSSI
PSTN
VOIP
Signaling System 7 (SS7)
Session Initiation Protocol (SIP)
dialup
SLIP
Integrated Services Digital Network (ISDN)
Primary Rate (PRI)
Digital Subscribers Line (DSL)
Digital Subscribers Line (DSL)
High Bit Data Rate DSL (HDSL)
Very High Bit Data Rate DSL (VDSL)
cable modems
Data-Over-Cable Service Interface Specifications (DOCSIS)
Virtual Private Network (VPN)
PPTP
L2TP
IPsec
Authentication Header (AH)
Encapsulating Security Payload (ESP)
Internet Security Association and Key Management Protocol (ISAKMP)
Internet key Exchange (IKE)
TACACS+
RADIUS
authenticator
authenticating server
Password Authentication Protocol (PAP)
Challenge Handshake Authentication Protocol (CHAP)
Extensible Authentication Protocol (EAP)
Telnet
Transport Layer Security/Secure Sockets layer (TLS/SSL)
Frequency Hopping Spread Spectrum (FHSS)
Direct Sequence Spread Spectrum (DSSS)
Orthogonal Frequency Division Multiplexing (OFDM)
Frequency Division Multiple Access (FDMA)
Code Division Multiple Access (CDMA)
phone cloning
access point
Service Set Identifier (SSID)
Infrastructure mode
Ad Hoc mode
802.11a
802.11b
802.11f
802.11g
802.11n
Multiple Input Multiple Output
Bluetooth
blue jacking
bluesnarfing
infrared
Wired Equivalent privacy (WEP)
Wi-Fi Protected Access (WPA)
WPA2
noise
attenuation
crosstalk
ping of death
smurf
Distributed Denial of Service (DDOS)
smurf attack
ICMP redirect
ping scanning
DNS cache poisoning attack
DNSSEC (DNS security)
URL hiding
domain grabbing
cybersquatting
email spoofing
phishing
whaling
spam
war driving
war chalking
SYN ACK attack
session highjacking attack
port scan
teardrop
IP address spoofing
Review Questions
1. At which layer of the OSI model does the encapsulation process begin?
a. Transport
b. Application
c. Physical
d. Session
2. Which two layers of the OSI model are represented by the Link layer of the TCP/IP model? (Choose two.)
a. Data Link
b. Physical
c. Session
d. Application
e. Presentation
3. Which of the following represents the range of port numbers that are referred to as “well-known” port numbers?
a. 49152–65535
b. 0–1023
c. 1024–49151
d. all above 500
4. What is the port number for HTTP?
a. 23
b. 443
c. 80
d. 110
5. What protocol in the TCP/IP suite resolves IP addresses to MAC addresses?
a. ARP
b. TCP
c. IP
d. ICMP
6. How many bits are contained in an IPv4 IP address?
a. 128
b. 48
c. 32
d. 64
7. Which of the following is a Class C address?
a. 172.16.5.6
b. 192.168.5.54
c. 10.6.5.8
d. 224.6.6.6
8. Which of the following is a private IP address?
a. 10.2.6.6
b. 172.15.6.6
c. 191.6.6.6
d. 223.54.5.5
9. Which service converts private IP addresses to public IP addresses?
a. DHCP
b. DNS
c. NAT
d. WEP
10. Which type of transmission uses stop and start bits?
a. Asynchronous
b. Unicast
c. Multicast
d. Synchronous
Answers and Explanations
1. b. The Application Layer (layer 7) is where the encapsulation process begins. This layer receives the raw data from the application in use and provides services such as file transfer and message exchange to the application (and thus the user).
2. a, b. The Link layer of the TCP/IP model provides the services provided by both the Data Link and the Physical layers in the OSI model.
3. b. System Ports, also called well-known ports are assigned by the IETF for standards-track protocols, as per [RFC6335].
4. c. The listed ports numbers are as follows:
23–Telnet
443–HTTPS
80–HTTP
110–POP3
5. a. Address Resolution Protocol (ARP) resolves IP addresses to MAC addresses.
6. c. IPv4 addresses are 32 bits in length and can be represented in either binary or in dotted decimal format.
7. b. The calls C range of addresses is from 192.0.0.0 -223.255.255.255
8. a. Here are the private IP address ranges:
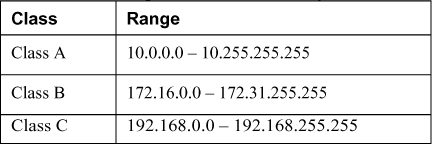
9. c. Network Address Translation (NAT) is a service that can be supplied by a router or by a server. The device that provides the service stands between the local LAN and the Internet. When packets need to go to the Internet the packets go through the NAT service first. The NAT service changes the private IP address to a public address that is routable on the Internet. When the response is returned from the web, the NAT service receives it and translates the address back to the original private IP address and sends it back to the originator.
10. a. With asynchronous transmission the systems use what are called start and stop bits to communicate when each byte is starting and stopping. This method also uses what are called parity bits to be used for the purpose of ensuring that each byte has not changed or been corrupted en route. This introduces additional overhead to the transmission.
