Let's take a look at a DNS request that will fail.
For this, we'll create some sort of random domain and put in gibberish, jhadgug384r8.com, as shown in the following screenshot:
Next, you need to start a new capture. Go ahead and press Enter:

Now, you need to stop the capture.
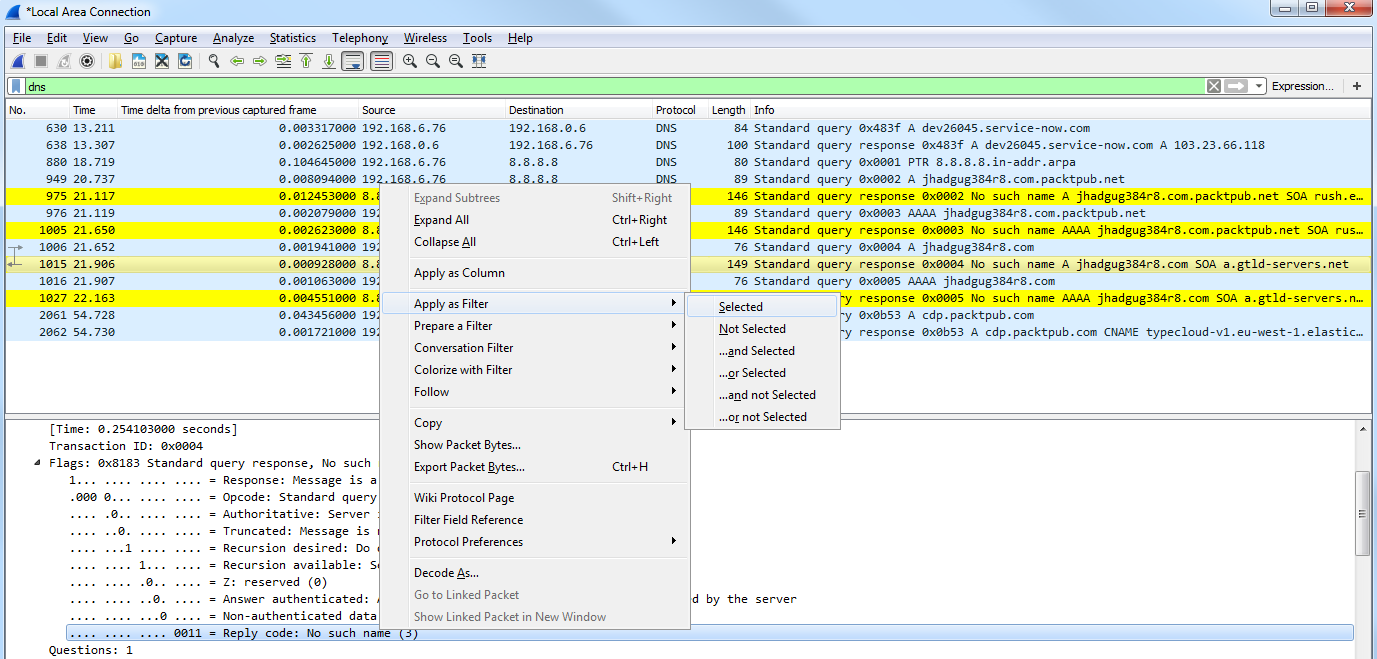
We can see we have the requests, like before:

We have the 8.8.8.8 domain name, and we have the actual request. Just like with wireshark.org, you can see that we've received an A record as well as a quad A record. This is because the system is requesting both IPv4 and IPv6. You saw that in the command-line output when we did wireshark.org.
So we have an A record, which is the IPv4, and a quad A record, which is IPv6. But you can see that we have some sort of gibberish domain name, which obviously responded back in that command line, saying that it couldn't find a result. So we sent out a query, asking for jhadgug384r8.com, and we received a response from the DNS servers at Google, saying No such name. If we go to the Flags and take a look, we have Message is a response, No such name, Reply code: No such name.
And if you remember from the filtering section, we can right-click on any flag and apply a filter by selecting Apply as Filter based on the options available, as shown in the following screenshot:
So we just filtered our display filter based on No such name as the error code in DNS. This is a great filter you could apply if you're doing a packet capture where there's some sort of connectivity problem. You can look for failed DNS queries.
