- Mastering Metasploit
- Mastering Metasploit
- Credits
- Foreword
- About the Author
- About the Reviewer
- www.PacktPub.com
- Preface
- 1. Approaching a Penetration Test Using Metasploit
- Organizing a penetration test
- Preinteractions
- Intelligence gathering/reconnaissance phase
- Predicting the test grounds
- Setting up Kali Linux in virtual environment
- The fundamentals of Metasploit
- Conducting a penetration test with Metasploit
- Benefits of penetration testing using Metasploit
- Penetration testing an unknown network
- Using databases in Metasploit
- Modeling threats
- Vulnerability analysis of VSFTPD 2.3.4 backdoor
- Vulnerability analysis of PHP-CGI query string parameter vulnerability
- Vulnerability analysis of HFS 2.3
- Maintaining access
- Clearing tracks
- Revising the approach
- Summary
- 2. Reinventing Metasploit
- Ruby – the heart of Metasploit
- Developing custom modules
- Building a module in a nutshell
- Understanding the existing modules
- Disassembling existing HTTP server scanner module
- Writing out a custom FTP scanner module
- Writing out a custom SSH authentication brute forcer
- Writing a drive disabler post exploitation module
- Writing a credential harvester post exploitation module
- Breakthrough meterpreter scripting
- Working with RailGun
- Summary
- 3. The Exploit Formulation Process
- The absolute basics of exploitation
- Exploiting stack-based buffer overflows with Metasploit
- Exploiting SEH-based buffer overflows with Metasploit
- Bypassing DEP in Metasploit modules
- Other protection mechanisms
- Summary
- 4. Porting Exploits
- 5. Testing Services with Metasploit
- 6. Virtual Test Grounds and Staging
- Performing a penetration test with integrated Metasploit services
- Summary
- 7. Client-side Exploitation
- 8. Metasploit Extended
- 9. Speeding up Penetration Testing
- 10. Visualizing with Armitage
From the intelligence gathering phase, we can see that there are numerous services running on the target. Hosts information also reveals that the target operating system is Linux-based. Let us search for one of the vulnerabilities within Metasploit and try to find the matching exploit module:
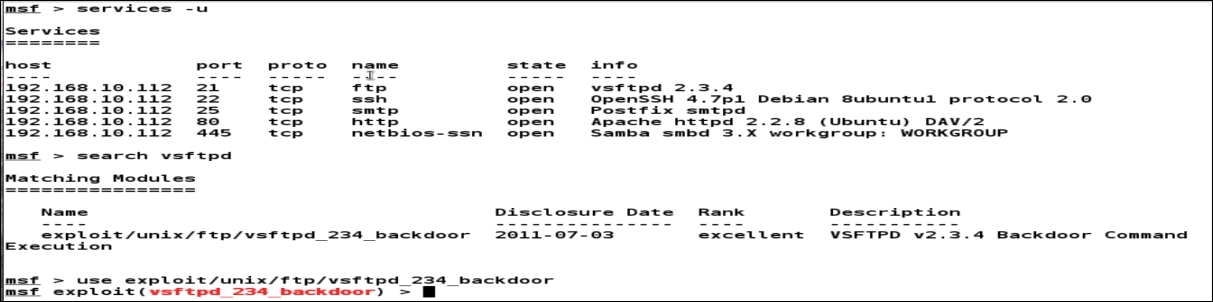
We can see that we already have a module in Metasploit that targets the vulnerable service found. After exploring the details at http://www.securityfocus.com/bid/48539/discuss and http://scarybeastsecurity.blogspot.in/2011/07/alert-vsftpd-download-backdoored.html, we can easily figure out that the vulnerability was intentionally put into the software and was carrying a backdoor that can be triggered remotely on the vulnerable system.
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
