Linux
Linux is a popular open-source operating system that is widely used in server environments. By default, Linux systems have simplified ACL-based file permission systems. Unlike a standard ACL-based system, rights are not inherited in Linux and must be applied to all files and folders explicitly. There are three rights and three classes to which those rights can be assigned.
The rights in a Linux environment are:
- Read—Grants a user or group the ability to read a file. If the right is set on a directory, the requestor may read the list of files in that directory.
- Write—Grants the requestor the ability to modify a file. If the right is set on a directory, the requestor may create, rename, or remove files in the directory.
- Execute—Grants the right to execute a file. This allows the requestor to run a binary or script file. If the right is set on a directory, the user may access files in the directory and access subdirectories but not view the list of files in the directory.
There are three classes of users as well: owner, group, and world. The group class refers to the group that the file or directory is a member of. Each one of these classes can have any, all, or none of the permissions applied to them. If no permission is set, the system denies access to the file.
Linux File Permissions
There are two standard ways Linux-based file permissions are written: symbolic notation or octal notation. Symbolic notation is simply listing the permissions by the first letter of the right. For example, the read right is listed as “r.” This is done in a nine-character string with dashes in place of unassigned rights. The order in which the classes are listed is always the same, with user coming first, followed by group, and then world. The order in each three-character set is also standard, with read coming first, then write, and followed by execute.
Octal notation is based on assigning each triplicate in symbolic notation a numerical value between 0 and 7. These values are then expressed as a three-digit number. No permissions has a value of zero, read adds 4, write adds 2, and execute adds 1. Adding the rights together gives a value for each class.
 NOTE
NOTE
Linux-based file permissions are customarily written in all lowercase, while Windows permissions are usually written with an initial capital.
TABLE 8-4 lists some examples of Linux-based rights in both notations.
| RIGHTS | SYMBOLIC NOTATION | OCTAL NOTATION |
|---|---|---|
| Full rights for all classes on a file | Rwxrwxrwx | 777 |
| Full rights for user, read execute for group, read for world | rwxr – xr – – | 754 |
| Read write for user, read for group, none for world | rw – r – – – – – | 640 |
| Full rights for user, write, execute for group, read for world | rwx – wx – – x | 731 |
To calculate the octal notation for full rights to the user and for read and execute for the group and world:
- For the user: r + w + x or 4 + 2 + 1 = 7
- For the group: r + x or 4 + 1 = 5
- For the world: r + w or 4 + 2 = 6
- Combine the results of the addition: 756
To change the permissions on a file or folder, use the chmod command, as shown here. Replace myfile with the name of the file or folder to be changed:
chmod 756 myfile
You can also use the letter notation or add or subtract rights from the user, group, or world. The command:
chmod g+rwx myfile
adds read, write, and execute permissions for the group on the file myfile. The command:
chmod w—x myfile
removes the execute permission from the world on the file myfile.
An example of modifying Linux file permissions with these commands appears in FIGURE 8-5. Take a few minutes to follow the sequence of steps that uses different variations of the chmod command to alter file permissions and the ls −al command to display the new permission settings on that file. You should be able to explain each of the changes that result from permission modifications.
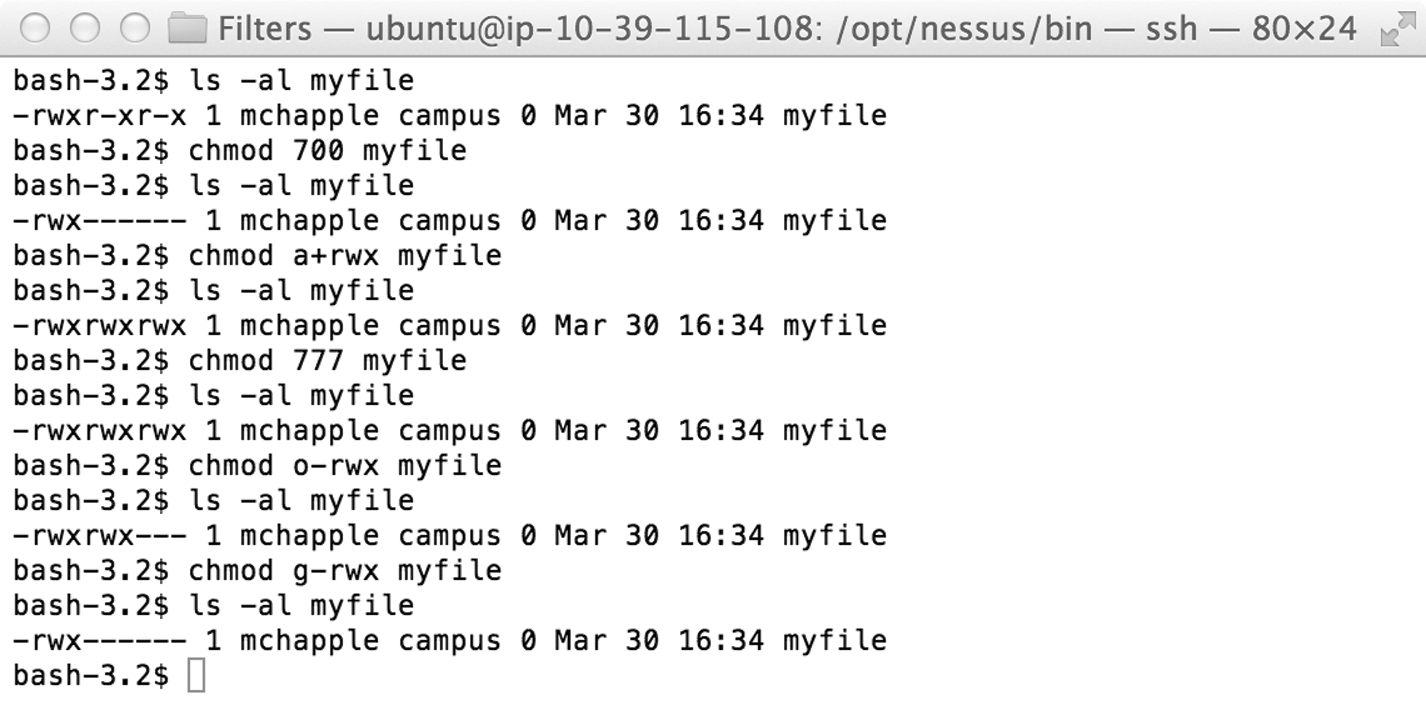
FIGURE 8-5 Changing Linux file permissions.
Although this simplified ACL is useful on a standalone server or workstation, it has a lack of granular control and does not allow for multiple groups with different permissions. This causes difficulties and confusion in a network environment. In most organizations, the basic Linux-based permissions have been extended with more full-featured ACL-based systems.
The Root Superuser
Root is a special class of user in a Linux environment, also known as the superuser. It is similar to the administrator user in Windows. Root has full access to the system. It has the ability to override file system permissions and run any process. Therefore, it is not a good idea to run a system when performing ordinary tasks as root. Not only is it a security concern but a user can also accidentally damage the system. Linux assumes you know what you are doing and that you intend to run all the commands you enter. If root is logged in, it is possible to accidentally delete major parts of the operating system.
However, some administrative tasks must be run with root access. Linux offers a solution: the sudo command. Substitute user do (sudo) allows you to run any process as if another user were running it. This allows an administrator to be logged into the system with a standard user account and still perform tasks that require enhanced rights on the system by using sudo to run the command with root permissions.
