Sometimes, the resource was created manually. For example, you might have had an existing AWS infrastructure in place before you decided to introduce Terraform to your company. Now you need to move it somehow under Terraform's control. One option is, of course, to just recreate everything. Not all the resources are that easy to recreate though. That's where the terraform import command will help us.
If you destroyed it before, then rerun the template to create a new VPC. Then, create a new NAT gateway manually from AWS Management Console:
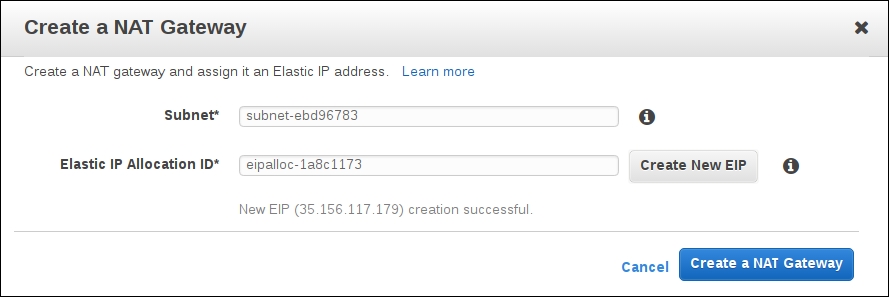
To import it, we need to know the ID of this gateway:

Copy it and go back to console. To add this gateway to the state file, you need to execute the following command:
$> terraform import aws_nat_gateway.imported_gateway nat-034caa3c2000cd7fb provider.aws.region aws_nat_gateway.imported_gateway: Importing from ID "nat-034caa3c2000cd7fb"... aws_nat_gateway.imported_gateway: Import complete! Imported aws_nat_gateway (ID: nat-034caa3c2000cd7fb) aws_nat_gateway.imported_gateway: Refreshing state... (ID: nat-034caa3c2000cd7fb) Import success! The resources imported are shown above. These are now in your Terraform state. Import does not currently generate configuration, so you must do this next. If you do not create configuration for the above resources, then the next `terraform plan` will mark them for destruction.
Pay attention to what Terraform tells you at the end of import procedure: import does NOT create configuration for this resource, it only adds it to the state file with the name you choose (imported_gateway in this case). If you don't add it to the template, then during next Terraform run it will be destroyed. If you don't want it to be destroyed (and why would you), you have to add something similar to the following configuration to your template:
resource "aws_nat_gateway" "imported_gateway" {
allocation_id = "eipalloc-1a8c1173"
subnet_id = "${aws_subnet.private-1.id}"
depends_on = ["aws_internet_gateway.gw"]
}
Importing like this can be useful if you have really small amount of resources outside Terraform template. If you have dozens of them, then this process might become a bit too repetitive and boring.
There is another solution: a ruby gem named terraforming that is capable of generating both state file and actual Terraform configuration. It is available on Github at https://github.com/dtan4/terraforming.
Installation is simple:
$> gem install terraforming
Now you can use the terraforming command to import various types of resources. Create VPC by hand and try it out:
$> terraforming vpc resource "aws_vpc" "my-manual-vpc" { cidr_block = "10.0.0.0/16" enable_dns_hostnames = false enable_dns_support = true instance_tenancy = "default" tags { "Name" = "my-manual-vpc" } }
And to make terraforming return possible state file for this vpc, run the following code:
terraforming vpc --tfstate
{
"version": 1,
"serial": 1,
"modules": [
{
"path": [
"root"
],
"outputs": {
},
"resources": {
"aws_vpc.my-manual-vpc ": {
Much more useful that built-in import command! It is capable of merging this state info into the existing state file as well:
$> terraforming vpc --state --merge=./terraform.tfstate
Note that terraforming gem works only with AWS resources. If you are using other provider, then the terraform import command is your last hope.
