Before testing a system against a recommended security setting, checking for vulnerabilities, or validating a vulnerable system through exploitation, it may make sense to clone your system for testing purposes, rather than testing the real system. Best practices are replicating everything from the hardware hosting the web application to all content because vulnerabilities can exist in all technology layers. Testing a cloned environment will give the Penetration Tester freedom to execute any degree of attack while avoiding negative impact to operations. Although most people cannot mirror the exact environment, it is usually possible to set up a virtual environment with the same functionality.
HTTrack is a free offline browser utility. HTTrack allows you to download a website from the Internet to a location directory, build all directories, capture HTML, images, and other files from the server and store on your computer. You can browse the cloned website link-to-link, as well as test it for vulnerabilities. HHTrack is an extremely simple tool to work with basic websites. It will not replicate dynamic content, nor will it replicate website middleware, such as databases. Therefore, it may not be appropriate in all Penetration Testing environments.
At the time of writing, HTTack no longer comes preinstalled with Kali. To install HTTack, open up a Terminal window and type apt-get install httrack. Once the install is complete, you can launch HTTrack, open a Terminal and type httrack.
You will be asked to give a project name, path to install the website (default is root/websites/), and URLs to copy. HTTrack gives a few options to copy your target(s), as shown in the following screenshot. Some additional optional questions are defining wildcards and recurse level. We selected option 2. Once you answer the questions, select Y to clone your target(s).

HTTrack will start cloning your target and all associated links. It may take a while to complete, depending on the size of your target. The next screenshot shows HTTrack cloning www.thesecurityblogger.com.

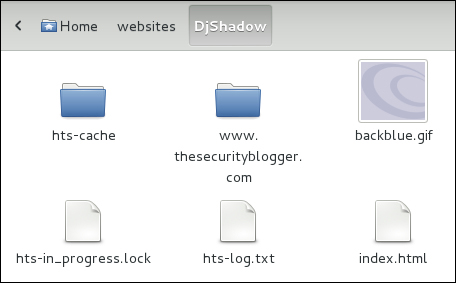
Navigate to the folder you specified to save the cloned targets to start your testing.