The MIM Service account will be the account that calls the MIM Synchronization service, and tells it to reset the password in AD. But in order for the MIM Service account to be able to do that, we need to assign it some permissions with the following steps:
- We need to add the account to a couple of groups created during installation of the MIM Synchronization service.
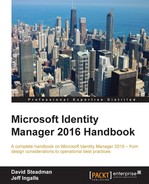
- Add the MIM Service account to the MIMSyncBrowse group, as shown in the following screenshot:
- To be allowed to initiate a password reset, we also need to add the MIM Service account to MIMSyncPasswordSet, as shown in the following screenshot:

The call from MIM Service to the MIM Synchronization service to do a password reset is made using Windows Management Instrumentation (WMI). This, in turn, means that we need to give MIM Service the WMI permissions as well. Because we have, in our example, separated MIM Service and the MIM Synchronization server, it will be remote WMI calls that demand a few extra steps. A few of these steps can be ignored if the services are running on the same server. You will need to make these changes if/when you separate the services.
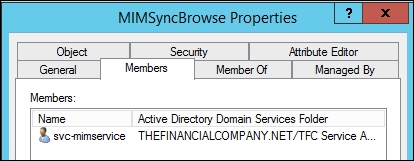
- On the Synchronization server, run Microsoft Management Console (MMC), and add the WMI Control snap-in, as seen in the following screenshot:
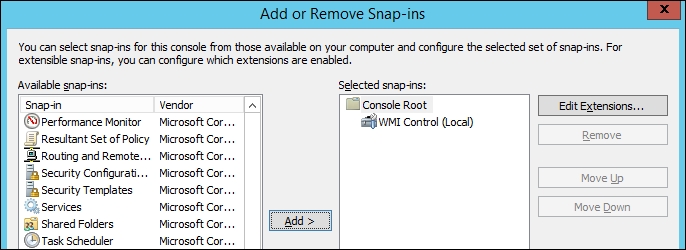
- Right-click on WMI Control (Local), and select Properties:
- In the Security tab, expand the Root namespace, and select the CIMV2 namespace. Then click on the Security button at the bottom:
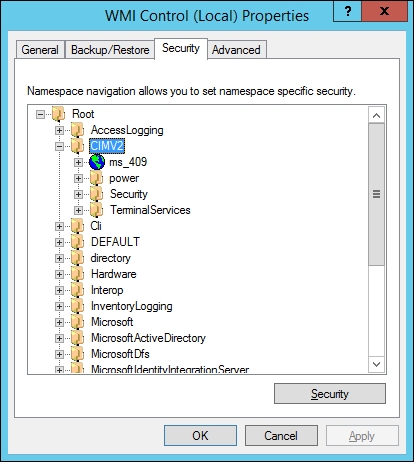
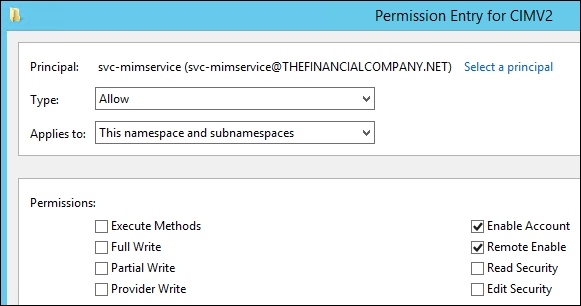
- Add the MIM Service account, and assign the Enable Account and Remote Enable permissions. This will allow the MIM Service account to connect to this namespace:

- But we need to give access to subnamespaces as well. Click on the Advanced button.
- In the advanced security settings for CIMV2, select the entry with the MIM Service account, and edit it. Change Applies to: from This namespace only to This namespace and subnamespaces. Click on OK a few times to save your settings:
As we have separated the servers, we also need to allow WMI calls through the firewall in the MIM Synchronization server.
- Navigate to Control Panel | System and Security and click on the Allow an app through Windows Firewall link:
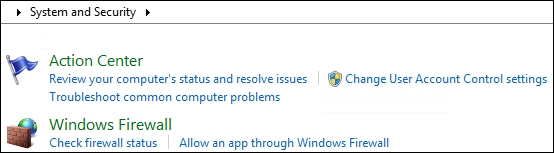
- In the Allowed apps and features setting, check the Windows Management Instrumentation (WMI) program:

This can be done using GPOs, if that is your preferred way of managing the local firewall on your servers. When allowing WMI to communicate through the firewall, it will create a firewall rule. If you would like to narrow down the IP addresses allowed to use the remote WMI, you can do so by modifying that rule.
The MIM Synchronization groups are assigned some DCOM permissions during setup, but we need to make some adjustments in order for SSPR to work. The following are steps to achieve this:
- Add the Component Services snap-in in the MMC (in the MIM Synchronization server), and click down to My Computer. Right-click and select Properties, then click on the COM Security tab:
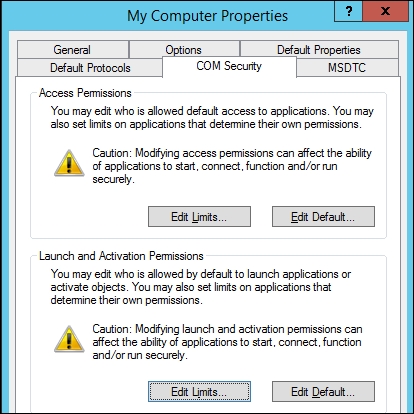
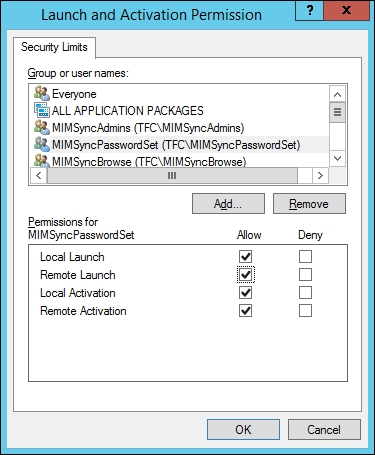
- Click on Edit Limits in the Launch and Activation Permissions section and add the Local Launch and Remote Launch permissions to the MIMSyncPasswordSet group:
Now the MIM Service account has the permissions required to make the calls to the MIM Synchronization service to tell it to reset the password in the target CDS (AD).