- We were able to dump and decrypt this configuration section from the sample. This is the most important part of the analysis process and provides insight into what the malware is configured for.
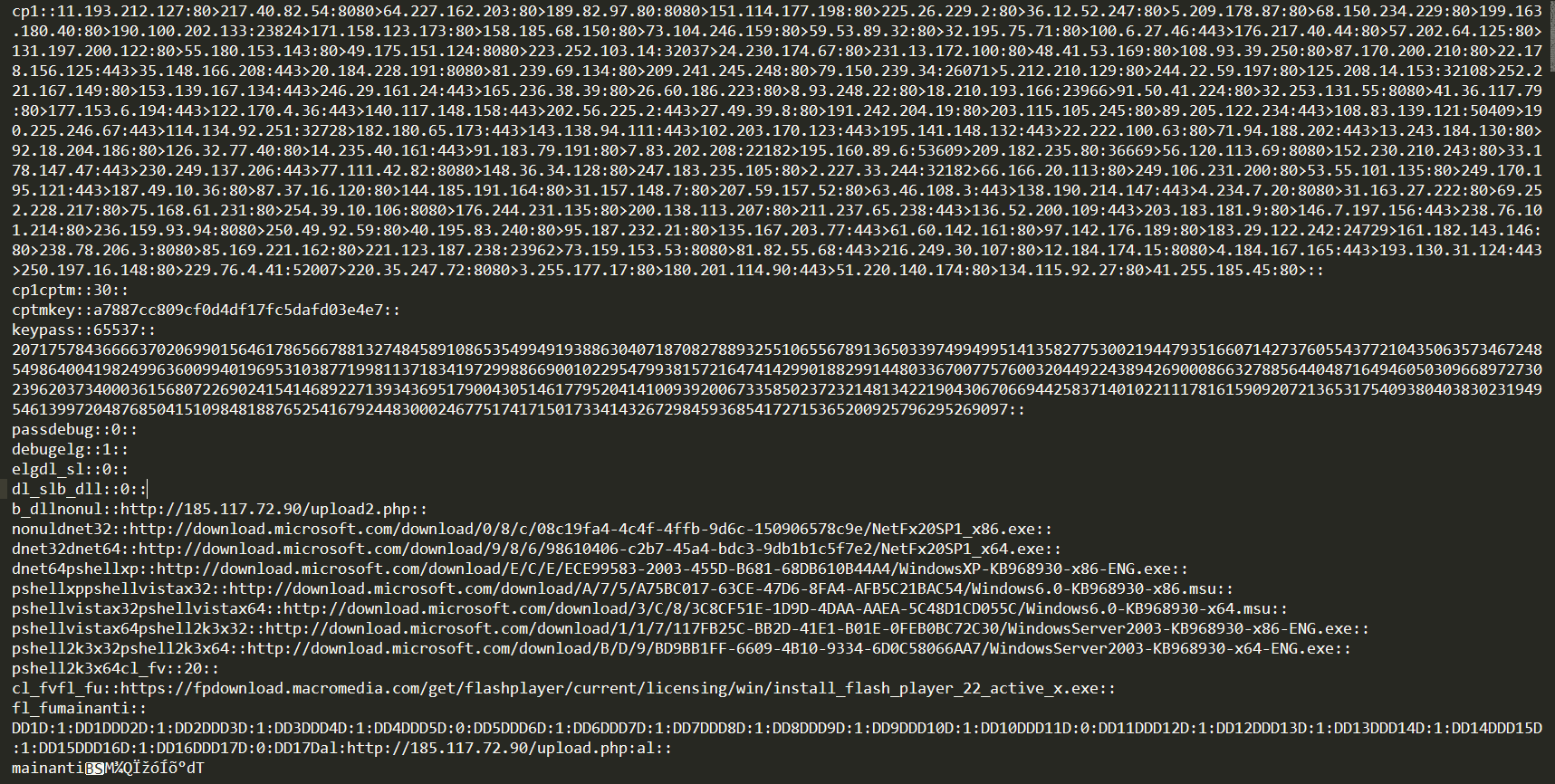
- By deobfuscating and decrypting the configuration file with the 16-byte key, we were able to see the list of command and control (C&C) servers the malware was using. See the following screenshot:
- This was the point at which we realized we were analyzing a Kovter sample.
- The configuration file of the malware contained a total of 129 hardcoded C&C servers, which are listed in the following figure:
|
11.193.212.127:80 217.40.82.54:8080 64.227.162.203:80 189.82.97.80:8080 151.114.177.198:80 225.26.229.2:80 36.12.52.247:80 5.209.178.87:80 68.150.234.229:80 199.163.180.40:80 190.100.202.133:23824 171.158.123.173:80 158.185.68.150:80 73.104.246.159:80 59.53.89.32:80 32.195.75.71:80 100.6.27.46:443 176.217.40.44:80 57.202.64.125:80 131.197.200.122:80 55.180.153.143:80 49.175.151.124:8080 223.252.103.14:32037 24.230.174.67:80 231.13.172.100:80 48.41.53.169:80 108.93.39.250:80 87.170.200.210:80 22.178.156.125:443 35.148.166.208:443 20.184.228.191:8080 81.239.69.134:80 209.241.245.248:80 79.150.239.34:26071 5.212.210.129:80 244.22.59.197:80 125.208.14.153:32108 252.221.167.149:80 153.139.167.134:443 246.29.161.24:443 165.236.38.39:80 26.60.186.223:80 8.93.248.22:80 18.210.193.166:23966 |
91.50.41.224:80 32.253.131.55:8080 41.36.117.79:80 177.153.6.194:443 122.170.4.36:443 140.117.148.158:443 202.56.225.2:443 27.49.39.8:80 191.242.204.19:80 203.115.105.245:80 89.205.122.234:443 108.83.139.121:50409 190.225.246.67:443 114.134.92.251:32728 182.180.65.173:443 143.138.94.111:443 102.203.170.123:443 195.141.148.132:443 22.222.100.63:80 71.94.188.202:443 13.243.184.130:80 92.18.204.186:80 126.32.77.40:80 14.235.40.161:443 91.183.79.191:80 7.83.202.208:22182 195.160.89.6:53609 209.182.235.80:36669 56.120.113.69:8080 152.230.210.243:80 33.178.147.47:443 230.249.137.206:443 77.111.42.82:8080 148.36.34.128:80 247.183.235.105:80 2.227.33.244:32182 66.166.20.113:80 249.106.231.200:80 53.55.101.135:80 249.170.195.121:443 187.49.10.36:80 87.37.16.120:80 144.185.191.164:80 31.157.148.7:80 |
207.59.157.52:80 63.46.108.3:443 138.190.214.147:443 4.234.7.20:8080 31.163.27.222:80 69.252.228.217:80 75.168.61.231:80 254.39.10.106:8080 176.244.231.135:80 200.138.113.207:80 211.237.65.238:443 136.52.200.109:443 203.183.181.9:80 146.7.197.156:443 238.76.101.214:80 236.159.93.94:8080 250.49.92.59:80 40.195.83.240:80 95.187.232.21:80 135.167.203.77:443 61.60.142.161:80 97.142.176.189:80 183.29.122.242:24729 161.182.143.146:80 238.78.206.3:8080 85.169.221.162:80 221.123.187.238:23962 73.159.153.53:8080 81.82.55.68:443 216.249.30.107:80 12.184.174.15:8080 4.184.167.165:443 193.130.31.124:443 250.197.16.148:80 229.76.4.41:52007 220.35.247.72:8080 3.255.177.17:80 180.201.114.90:443 51.220.140.174:80 134.115.92.27:80 41.255.185.45:80 |
- Although a majority of the C&C servers were dead, these servers were being used by the malware for grabbing click-fraud links, playing provided ads, and silently clicking the provided links in the background, as can be seen in the following screenshot:

- Though the malware is capable of running other malicious modules from its C&C server and acting as a remote back door, we have not observed such behavior during our sandboxed (virtual space in which the malware was run securely) analysis.
