Day 16. Utilizing NetFlow
CCNA 200-101 ICND2 Exam Topics
![]() Monitor NetFlow statistics
Monitor NetFlow statistics
![]() Utilize NetFlow data
Utilize NetFlow data
Key Topics
Even though Simple Network Management Protocol (SNMP) and syslog messages provide important information to network administrators, it quickly became apparent that a more powerful network monitoring tool was needed. The review today covers the Cisco NetFlow protocol.
NetFlow Operation
NetFlow was invented by Cisco to track TCP/IP flows in the network. You can use the information from these flows for a variety of purposes, including the following:
![]() Identify potential bottlenecks
Identify potential bottlenecks
![]() Provide data for network improvements and redesigns
Provide data for network improvements and redesigns
![]() Assist in monitoring customer usage of links
Assist in monitoring customer usage of links
NetFlow became so popular that it is now a standard used by other networking equipment manufacturers. Flexible NetFlow is the latest NetFlow technology. Flexible NetFlow (Version 9) improves on “original NetFlow” by adding the capability to customize the traffic analysis parameters for the specific requirements of a network administrator.
Most organizations use NetFlow for some or all of the following important data collection purposes:
![]() Measuring who is using what network resources for what purpose
Measuring who is using what network resources for what purpose
![]() Accounting and charging back according to the resource utilization level
Accounting and charging back according to the resource utilization level
![]() Using the measured information to do more effective network planning so that resource allocation and deployment are well aligned with customer requirements
Using the measured information to do more effective network planning so that resource allocation and deployment are well aligned with customer requirements
![]() Using the information to better structure and customize the set of available applications and services to meet user needs and customer service requirements
Using the information to better structure and customize the set of available applications and services to meet user needs and customer service requirements
When Cisco sought out to create NetFlow, two key criteria provided guidance in its creation:
![]() NetFlow should be completely transparent to the applications and devices in the network.
NetFlow should be completely transparent to the applications and devices in the network.
![]() NetFlow should not have to be supported and running on all devices in the network to function.
NetFlow should not have to be supported and running on all devices in the network to function.
The original NetFlow distinguishes flows using a combination of seven fields. Should one of these fields vary in value from another packet, the packets could be safely determined to be from different flows:
![]() Source IP address
Source IP address
![]() Destination IP address
Destination IP address
![]() Source port number
Source port number
![]() Destination port number
Destination port number
![]() Layer 3 protocol type
Layer 3 protocol type
![]() Type of Service (ToS) marking
Type of Service (ToS) marking
![]() Input logical interface
Input logical interface
Configuring NetFlow
To implement NetFlow on a router, complete these steps:
Step 1 Configure NetFlow data capture using the ip flow ingress and ip flow egress interface configuration commands. A flow is unidirectional.
Step 2 Configure NetFlow to export data to the NetFlow collector’s IP address and source port number. Also, specify the NetFlow version and source interface (optional):
Router(config)# ip flow-export destination ip-address port-number
Router(config)# ip flow-export version version
Router(config)# ip flow-export source type number
Example 16-1 demonstrates configuring NetFlow on a router.
Example 16-1 Configuring NetFlow on a Router
R1(config)# interface g0/1
R1(config-if)# ip flow ingress
R1(config-if)# ip flow egress
R1(config-if)# exit
R1(config)# ip flow-export destination 192.168.1.3 2055
R1(config)# ip flow-export version 5
R1(config)# end
Verifying and Using NetFlow
After configuring NetFlow, you can analyze the exported data on a workstation running an application such as SolarWinds NetFlow Traffic Analyzer, Plixer Scrutinizer, or Cisco NetFlow Collector (NFC). Minimally, you can verify NetFlow is collecting data with the show ip cache flow command, as demonstrated in Example 16-2.
Example 16-2 Examining the NetFlow Cache
R1# show ip cache flow
IP packet size distribution (178617 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.002 .080 .008 .005 .001 .000 .001 .001 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .000 .895 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
5 active, 4091 inactive, 1573 added
18467 ager polls, 0 flow alloc failures
Active flows timeout in 1 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 34056 bytes
5 active, 1019 inactive, 1569 added, 1569 added to flow
0 alloc failures, 0 force free
1 chunk, 1 chunk added
last clearing of statistics never
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
-------- Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 3 0.0 3 50 0.0 1.0 15.0
TCP-WWW 245 0.0 6 93 0.0 0.3 2.4
TCP-other 529 0.0 27 57 0.2 0.7 6.2
UDP-other 328 0.0 6 107 0.0 2.4 15.3
ICMP 711 0.0 226 1261 2.4 0.2 15.4
Total: 1816 0.0 98 1137 2.7 0.8 11.0
UDP-other 253 0.0 6 105 0.0 2.6 15.3
ICMP 560 0.0 286 1262 2.6 0.2 15.5
Total: 1568 0.0 113 1142 2.9 0.8 10.4
SrcIf SrcIPaddress DstIf DstIPaddress Pr SrcP DstP Pkts
Gi0/1 192.168.1.3 Local 192.168.1.1 06 100B 01BB 1
Gi0/1 192.168.1.3 Local 192.168.1.1 01 0000 0303 1
Gi0/1 192.168.1.3 Local 192.168.1.1 01 0000 0800 1
Example 16-2 confirms that the router is collecting data. To verify that you correctly configured NetFlow, use the show ip flow interface and show ip flow export commands, as shown in Example 16-3.
Example 16-3 Verifying the NetFlow Configuration
R1# show ip flow interface
GigabitEthernet0/1
ip flow ingress
ip flow egress
R1# show ip flow export
Flow export v5 is enabled for main cache
Export source and destination details :
VRF ID : Default
Destination(1) 192.168.1.3 (2055)
Version 5 flow records
1764 flows exported in 532 udp datagrams
0 flows failed due to lack of export packet
0 export packets were sent up to process level
0 export packets were dropped due to no fib
0 export packets were dropped due to adjacency issues
0 export packets were dropped due to fragmentation failures
0 export packets were dropped due to encapsulation fixup failures
Examining NetFlow Data
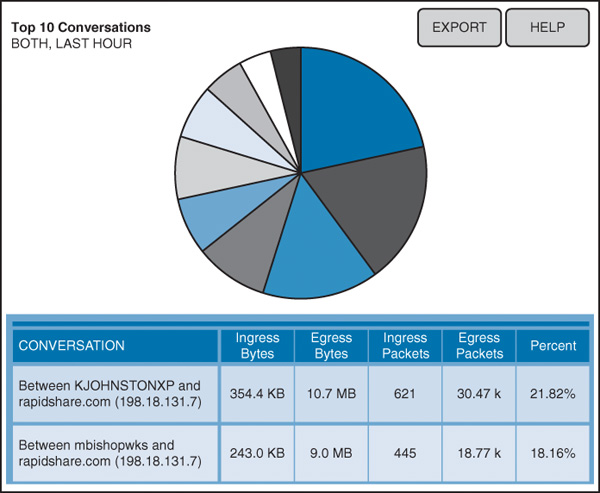
On a NetFlow collector, the NetFlow data is written to a drive at specified intervals. The administrator may run multiple collection schemes or threads concurrently. For example, different cuts of data can be stored to support planning versus billing; a NetFlow collector can easily produce the appropriate aggregation schemes. Figure 16-1 illustrates a NetFlow collector passively listening for exported NetFlow datagrams.
Collecting data provides a network administrator with data on top talkers, top hosts, and top listeners. Because data is preserved over time, after-the-fact network traffic analyses can determine network use trends.
You can use many different freeware and paid applications to collect NetFlow data. Typical reports that these applications generate include the following:
![]() Top talkers in the network
Top talkers in the network
![]() Top listeners in the network
Top listeners in the network
![]() Most frequently visited websites
Most frequently visited websites
![]() Most frequently downloaded content
Most frequently downloaded content
![]() Systems with the least available bandwidth
Systems with the least available bandwidth
As shown in Figure 16-2, a NetFlow collector displays the kinds of traffic (web, mail, FTP, peer-to-peer, and so on) on the network and the devices that send and receive most of the traffic.
You can sort and visualize the data in a manner that makes sense to you. You can then export the data to spreadsheets, such as Microsoft Excel, for more detailed analysis, trending, and reporting.
Study Resources
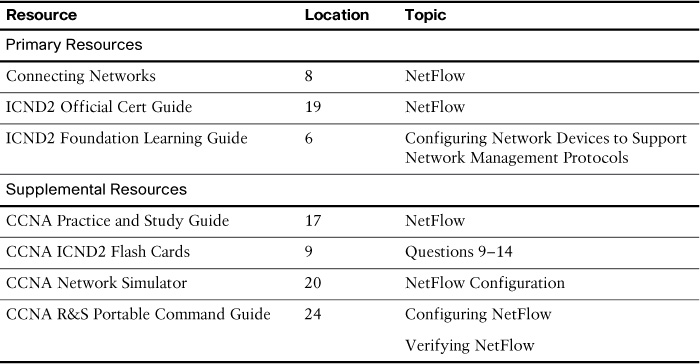
For today’s exam topics, refer to the following resources for more study.