We can grant permission for a non-admin user from the CLI as follows:
- Create a policy document that allows AssumeRole on the child account role, that is, OrganizationAccountAccessRole and save it as assume-role-policy-document.json. Refer to the previous section for the JSON document structure.
- Create the policy, as follows:
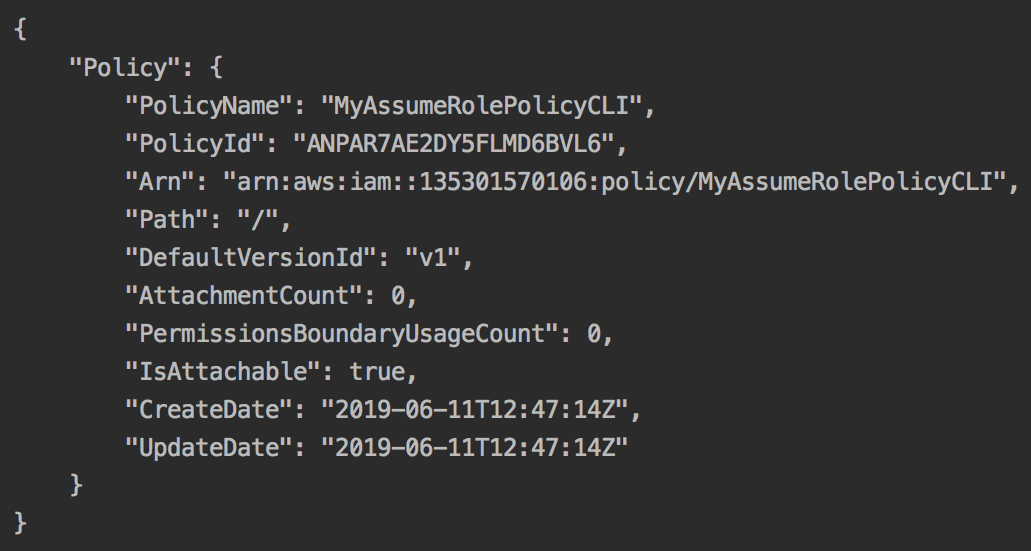
aws iam create-policy
--policy-name MyAssumeRolePolicyCLI
--policy-document file://resources/assume-role-policy-document.json
--profile awssecadmin
We should get the following response:
- Attach this policy to the user group:
aws iam attach-group-policy
--group-name testusergroup
--policy-arn arn:aws:iam::135301570106:policy/MyAssumeRolePolicyCLI
--profile awssecadmin
We should now be able to switch roles.