In this recipe, we are going to learn about WEP encryption cracking. Wired Equivalent Privacy (WEP) is a security protocol, specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11b, and designed to provide a Wireless Local Area Network (WLAN) with a level of security and privacy comparable to what is usually expected of a wired LAN. WEP works on RC4 encryption and has been widely used on the Internet as a part of HTTPS. The flaw here is not RC4 but the way RC4 had been implemented. The problem was the reuse of IVs. For this exercise, we will be using a tool called Wifite. This tool is used to attack multiple WEP-, WPA-, and WPS-encrypted networks in a row. This tool is customizable and can be automated with only a few arguments. Wifite aims to be the "set it and forget it" wireless auditing tool.
For this activity, we will require wifite (preinstalled in Kali), an active and running wireless adaptor, and a wireless router running WEP encryption.
- To ensure that the wifite framework is updated, enter the following command:
wifite -upgrade - To list all the available wireless networks, enter the following command:
wifite -showbThe output will be as shown in the following screenshot:
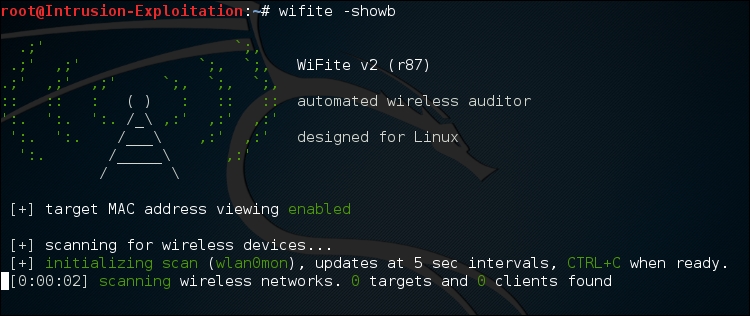

- With this, one can have a look of all the wireless devices available in the vicinity. Use Ctrl + C to break out of the script.
- Use the following command to start Wifite again:
WifiteThe output will be as shown in the following screenshot:

- As we can see, the command has listed all the detected wireless networks with their ESSID, BSSID, and more. Keep in mind the number corresponding to the target ID. Now we should break out of the listing mode and enter the following keyboard combination:
Ctrl + C 3
The output will be as shown in the following screenshot:

- Once we hit the Ctrl + C combination, it prompts us to provide the target number. Once this is done wifite will automatically start working on WEP cracking and give you the password.
In the background, what the framework does initially is put the wireless adaptor into monitor mode using the airmon-ng command, a part of the aircrack-ng suite, and start the enumeration list:
wifite -upgrade: This command upgrades the wifite framework to the latest versionwifite -showb: This command lists all the available wireless networks detected over the network
The details of how WEP cracking works are as follows:
WEP prepares a keyschedule (seed); this is a concatenation of the user's shared secret key with a random-generated 24-bit initialization vector (IV). The IV increases the life of the secret key because the station can change the IV for each frame transmission. WEP then sends that output as a resulting "seed" to a pseudo-random number generator that produces a keystream. The length of this keystream is equal to the length of the frame's payload plus a 32-bit (Integrity Check Value (ICV)).
The reason WEP failed is because the IVs were short and in clear text; the 24-bit field keystream generated by RC4 is relatively small. As the IV's are static and the stream of IV is short ,hence they are reused. There has been no standard as to how the IV has to be set or changed; there are possible scenarios where wireless adapters from the same vendors end up having the same IV sequences.
An attacker can keep sniffing data and collect all the IVs available and then successfully crack the password. For more information, visit http://www.isaac.cs.berkeley.edu/isaac/wep-faq.html .
