You've learnt how to transmit data via Bluetooth and Infrared from one device to another in Chapter 5, Building Integrated Services. Just to jog your memory a little, you placed the data for a lead account in a Dataset object, serialized it into an array of bytes, transmitted it across to the other device, and then de-serialized the stream of bytes back into a Dataset object).
It is unsafe to leave your data unprotected over wireless transmission. For instance, Bluetooth technology works over a distance wide enough for an unauthorized device (and an adept hacker) to intercept the stream of data.
The System.Security.Cryptography libraries in the .NET CF provide a number of algorithms that allow you to encrypt and decrypt your data. Unlike the SHA algorithm you've seen earlier, which was one-way, these algorithms are two-way. A key (password) is usually applied during the encryption. An encrypted stream can only be decrypted when the same key is supplied. One of these algorithms is the Rijndael algorithm.
Note
Rijndael encryption is also another name for AES (Advanced Encryption Standard). Rijndael encryption comes in three types—128-bit, 192-bit, and 256-bit. The bit size denotes the strength of the key.
In Rijndael encryption, three pieces of information usually need to be supplied:
- The text to encrypt (input)
- Initialization Vector (IV)
- Key (password)
The IV is an arbitrary number that can be used along with the key for data encryption. The purpose of an IV is to prevent repetition in data encryption. For example, if every occurrence of the word "hello" in the original text became the sequence "ABC789" after encryption, without an IV, an attacker could assume that every occurrence of "ABC789" meant that it represented the same identical sequence. This way an attacker may be able to identify patterns in the ciphertext. An IV prevents the appearance of corresponding duplicate character sequences in the ciphertext.
Let's take a look at how you can apply Rijndael encryption to a simple text message. Create a new C# Smart Device project, add a new form to the project and in this form, import the following library:
using System.Security.Cryptography;
The next thing you need to do is write the EncryptAES function. This function (shown as follows) will pass in the plain text, key, and IV into the .NET CF Rijndael cryptography library and set up the stream objects required for the encryption process. The function will return a stream of bytes representing the encrypted text (ciphertext).
public byte[] EncryptAES(string plainText, byte[] Key, byte[] IV)
{
RijndaelManaged _aesObject = null;
MemoryStream _encStream = null;
// Create the Rijndael object
_aesObject = new RijndaelManaged();
_aesObject.Key = Key;
_aesObject.IV = IV;
// Create an encryptor object
ICryptoTransform encryptor =
_aesObject.CreateEncryptor(_aesObject.Key, _aesObject.IV);
// Create the stream objects used for the encryption
_encStream = new MemoryStream();
using (CryptoStream csEncrypt = new
CryptoStream(_encStream, encryptor, CryptoStreamMode.Write))
{
using (StreamWriter swEncrypt = new
StreamWriter(csEncrypt))
{
// Write data to the stream
swEncrypt.Write(plainText);
}
}
_aesObject.Clear();
return _encStream.ToArray();
}
The DecryptAES function is roughly similar. You will need to pass in the same key and IV (used during encryption) to decrypt the ciphertext successfully. This function will output the original plain text as a string object.
public string DecryptAES(byte[] cipherText, byte[] Key, byte[] IV)
{
RijndaelManaged _AESObject = null;
string _decText = null;
// Create the Rijndael object
_AESObject = new RijndaelManaged();
_AESObject.Key = Key;
_AESObject.IV = IV;
// Create the decryptor object
ICryptoTransform decryptor =
_AESObject.CreateDecryptor(_AESObject.Key, _AESObject.IV);
// Setup the stream objects used for decryption
using (MemoryStream msDecrypt = new MemoryStream(cipherText))
{
using (CryptoStream csDecrypt = new
CryptoStream(msDecrypt, decryptor, CryptoStreamMode.Read))
{
using (StreamReader srDecrypt = new StreamReader(csDecrypt))
{
// Read data from the stream
_decText = srDecrypt.ReadToEnd();
}
}
}
_AESObject.Clear();
return _decText;
}
It's time to try out these routines. Place a button on the form, and in the click event of this button, write the following code:
private void button1_Click(object sender, EventArgs e)
{
string plainText = "HELLO WORLD!";
// You can get a new IV and key simply by instantiating a
// new RijndaelManaged class
RijndaelManaged myRijndael = new RijndaelManaged();
// Run the encryption routine
byte[] _encryptedData = EncryptAES(plainText,
myRijndael.Key, myRijndael.IV);
// Run the decryption routine
string _decryptedData = DecryptAES(_encryptedData,
myRijndael.Key, myRijndael.IV);
MessageBox.Show("Decrypted text:" + _decryptedData);
}
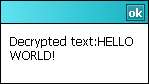
If you run the form and click the button, you should be able to see your original text after it has been run through the encryption and decryption process:
You can now apply these same routines to your sales force project by encrypting the stream of bytes obtained right after serializing a dataset (before it gets sent out via Bluetooth or Infrared). You must also correspondingly decrypt the stream of bytes immediately once it is retrieved on the device, and then finally de-serialize it back into a dataset.
