Kali includes several tools developed to take advantage of IPv6 (most comprehensive scanners, such as nmap, now support IPv6), some of which are as follows; tools that are particular to IPv6 were largely derived from the THC-IPv6 Attack Toolkit.
The following table provides the list of tools that are utilized for reconnaissance of IPv6:
|
Application |
Description |
|
dnsdict6 |
Enumerates sub-domains to obtain IPv4 and IPv6 addresses (if present) using a brute force search based on a supplied dictionary file or its own internal list |
|
dnsrevenum6 |
Performs reverse DNS enumeration given an IPv6 address |
|
covert_send6 |
Sends the content of a file covertly to the target |
|
covert_send6d |
Writes covertly received content to file |
|
denial6 |
Performs various denial of service attacks on a target |
|
detect-new-ip6 |
Detects new IPv6 addresses joining the local network |
|
detect_sniffer6 |
Tests whether systems on the local LAN are sniffing |
|
exploit6 |
Performs exploits of various CVE-known IPv6 vulnerabilities on the destination |
|
fake_dhcps6 |
Fake DHCPv6 server |
Metasploit can also be utilized for IPv6 host discovery. The auxiliary/scanner/discovery/ipv6_multicast_ping module will discover all of the IPv6-enabled machines with the physical (MAC) address, as shown in the following screenshot:

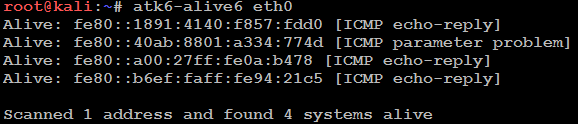
THC IPv6 suite atk6-alive6 will discover alive addresses in the same segment, as shown in the following screenshot: