So far, you have learned how to use passive reconnaissance to collect names and biographical information for users of the target being tested; this is the same process used by hackers. The next step is to use this information to create password lists specific to the users and the target.
Lists of commonly used passwords are available for download, and are stored locally on Kali in the /usr/share/wordlists directory. These lists reflect the choices of a large population of users, and it can be time consuming for an application to attempt to use each possible password before moving on to the next password in the queue.
Fortunately, Common User Password Profiler (CUPP) allows the tester to generate a wordlist that is specific to a particular user. CUPP was present on Backtrack 5r3; however, it will have to be downloaded for use on Kali. To obtain CUPP, enter the following command:
git clone https://github.com/Mebus/cupp.git
This will download CUPP to the local directory.
CUPP is a Python script, and can be simply invoked from the CUPP directory by entering the following command:
root@kali:~# python cupp.py -i
This will launch CUPP in interactive mode, which prompts the user for specific elements of information to use in creating wordlists. An example is shown in the following screenshot:
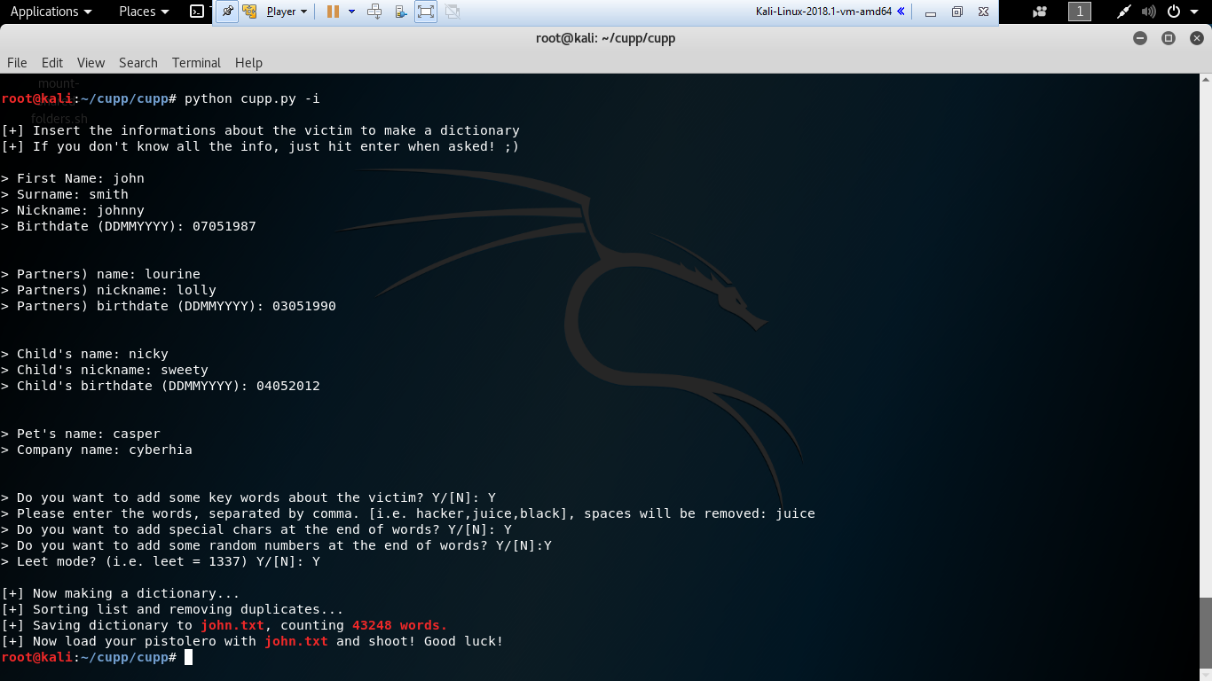
When the interactive mode has completed creating a wordlist, it is placed in the cupp directory.
