Amazon Web Services (AWS) provide Kali Linux as part of Amazon Machine Interface (AMI) and Software as a Service (SaaS). A penetration tester or hacker can utilize AWS to conduct penetration testing and more efficient phishing attacks. In this section, we will go through the steps to bring up the Kali Linux on AWS.
First, you'll need to have a valid AWS account. You can sign up by visiting the following URL: https://console.aws.amazon.com/console/home.
When we log in to the AWS account, we should be able to see all of the AWS services. Search for Kali Linux. You'll see the following as per the screenshot, https://aws.amazon.com/marketplace/pp/B01M26MMTT:

The open source community has made it very simple to directly launch with pre-configured Kali Linux 2018.1 in the Amazon marketplace. The following URL will take us to a direct launch of Kali-Linux within a few minutes, https://aws.amazon.com/marketplace/pp/B01M26MMTT. Follow the instructions and then you should be able to launch the instance by selecting Continue to Subscribe. This should take you to the following option to select as shown in the following screenshot. Finally, just click Launch:

Before you launch Kali Linux 2018.3 from AWS, it is recommended that you create a new key pair as shown in the following screenshot:

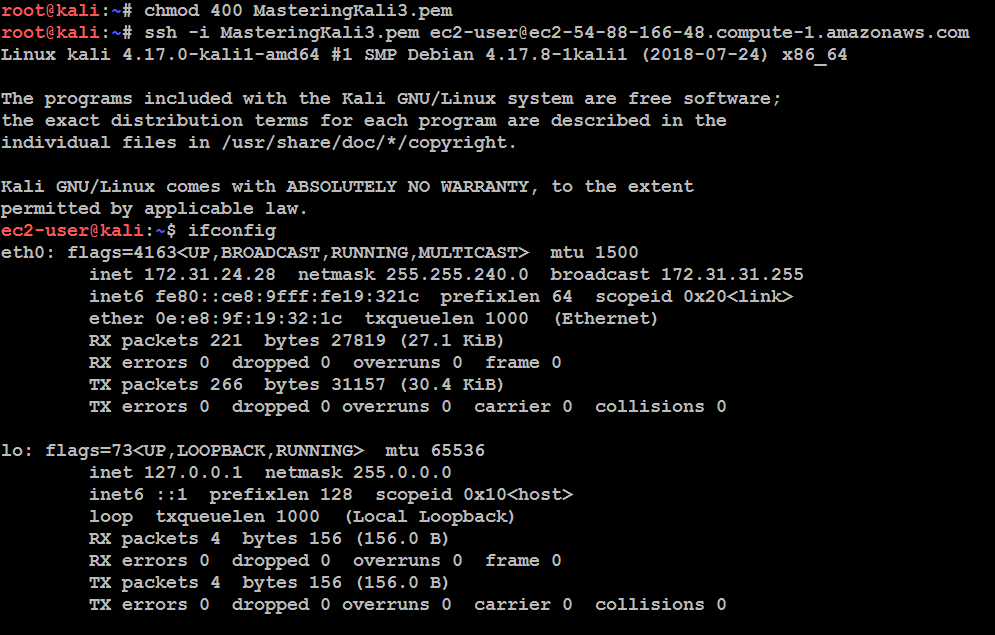
As usual, to use any AWS VM, you must create your own key pair in order to ensure the security of the environment. Then, you should be able to log in by entering the following command from your command shell. In order to use the private key to log in without the password, Amazon enforces the file permission to be tunneled. We will use the following commands to connect to the Kali Linux instance:
chmod 600 privatekey.pem
ssh -i privatekey.pem ec2-user@amazon-dns-ip
The following screenshot depicts the successful usage of Kali on AWS: