We recommend that before configuring a capture filter, you will carefully design what you want to capture, and prepare your filter for this. Don't forget—what doesn't pass the filter, will be lost.
There are some Wireshark predefined filters that you can use, or you can configure it yourself as described in the next recipe.
For configuring capture filters before starting with the capture, go through the following steps:
- For configuring a capture filter, click on the Show the capture options… button, second from the left, as shown in the following screenshot:

- The Wireshark: Capture Options window will open as you see in the following screenshot:
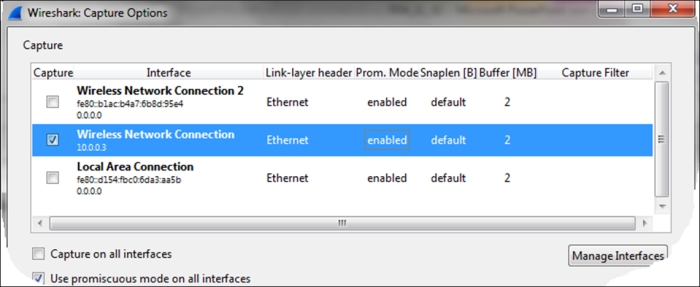
- Double-click on the interface on which you want to configure the capture filter (you can verify which interface is the active one, as described in Chapter 1, Introducing Wireshark).
- The Edit Interface Settings window will open up, as in the following screenshot:

- Now, we can configure the capture filters by simply writing the filter string in the Wireshark: Capture Filter window, or click on the Capture Filter: button; the following window will open:
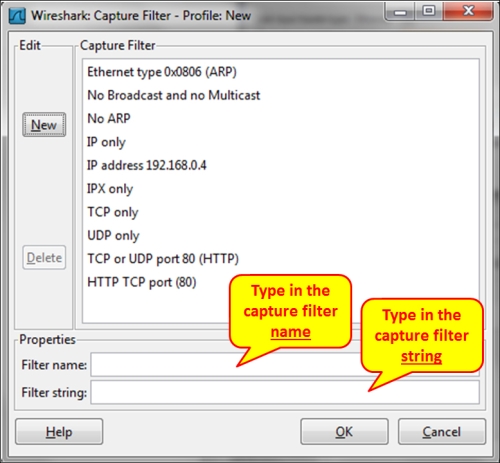
The Wireshark: Capture Filter window enables you to configure filters according to Berkeley Packet Filter (BPF). After writing a filter string, you can click on the Compile BPF button, and the BPF compiler will check your syntax, and if it's wrong you will get an error message.
In addition to this, when you type a filter string in the capture filter text box, and the filter string is correct, it will become green, and if not, it will become red.
The BPF filter only checks if the syntax is right. It does not check if the condition is correct. For example, if you type the string host without any parameter, you will get an error and the string will become red, but if you type host 192.168.1.1000, it will pass and the window will become green.
Tip
BPF is a syntax coming from the paper The BSD Packet Filter: A New Architecture for User-level Packet Capture by Steven McCanne and Van Jacobson from the Lawrence Berkeley Laboratory at Berkeley University from December 1992. The document can be seen at: http://www.tcpdump.org/papers/bpf-usenix93.pdf.
Capture filters are made out of a string containing a filtering expression. This expression selects the packets which will be captured and which packets will be ignored. Filter expressions consist of one or more primitives. Primitives usually consist of an identifier (name or number) followed by one or more qualifiers. There are three different kinds of qualifiers:
- Type: These qualifiers say what kind of thing the identifier name or number refers to. Possible types are
hostfor host name or address,netfor network,portfor TCP/UDP port, and so on. - Dir (direction): These qualifiers specify a particular transfer direction to and/or from ID. For example
srcindicates source,dstindicates destination, and so on. - Proto (protocol): These are the qualifiers that restrict the match to a particular protocol. For example,
etherfor Ethernet,ipfor Internet Protocol,arpfor Address Resolution Protocol, and so on.
Identifiers are the actual condition that we test. Identifier can be the address 10.0.0.1, port number 53, or network address 192.168.1 (this is an identifier for network 192.168.1.0/24).
For example, in the filter tcp dst port 135, we have:
dstis the dir qualifierportis the type qualifiertcpis the Proto qualifier
You can configure different capture filters on different interfaces:

This can be used when you capture traffic on two interfaces of a device, and want to check for different packets on the two sides.
The capture filters are stored in a file named cfilters under the Wireshark directory. In this file you will find the predefined filters, along with the filters you have configured, and you will be able to copy the file to other computers. The location of this directory will change depending on how Wireshark is installed and on what platform.
- The Wireshark Capture Filters are based on the
tcpdumpprogram. You can find the reference at http://www.tcpdump.org/tcpdump_man.html. - You can also find helpful information on the Wireshark manual pages at http://wiki.wireshark.org/CaptureFilters.
