 Configuring byte offset and payload matching filters
by Charit Mishra, Yoram Orzach, James H Baxter
Wireshark Revealed: Essential Skills for IT Professionals
Configuring byte offset and payload matching filters
by Charit Mishra, Yoram Orzach, James H Baxter
Wireshark Revealed: Essential Skills for IT Professionals
- Wireshark Revealed: Essential Skills for IT Professionals
- Table of Contents
- Wireshark Revealed: Essential Skills for IT Professionals
- Credits
- Preface
- 1. Module 1
- 1. Getting Acquainted with Wireshark
- 2. Networking for Packet Analysts
- The OSI model – why it matters
- IP networks and subnets
- Switching and routing packets
- WAN links
- Wireless networking
- Summary
- 3. Capturing All the Right Packets
- Picking the best capture point
- Test Access Ports and switch port mirroring
- Capturing interfaces, filters, and options
- Verifying a good capture
- Saving the bulk capture file
- Isolating conversations of interest
- Using the Conversations window
- Wireshark display filters
- Filter Expression Buttons
- Following TCP/UDP/SSL streams
- Marking and ignoring packets
- Saving the filtered traffic
- Summary
- 4. Configuring Wireshark
- 5. Network Protocols
- The OSI and DARPA reference models
- Transport layer protocols
- Application layer protocols
- Summary
- 6. Troubleshooting and Performance Analysis
- Troubleshooting methodology
- Troubleshooting connectivity issues
- Troubleshooting functional issues
- Performance analysis methodology
- Top five reasons for poor application performance
- Summary
- 7. Packet Analysis for Security Tasks
- 8. Command-line and Other Utilities
- 2. Module 2
- 1. Introducing Wireshark
- 2. Using Capture Filters
- 3. Using Display Filters
- 4. Using Basic Statistics Tools
- Introduction
- Using the Summary tool from the Statistics menu
- Using the Protocol Hierarchy tool from the Statistics menu
- Using the Conversations tool from the Statistics menu
- Using the Endpoints tool from the Statistics menu
- Using the HTTP tool from the Statistics menu
- Configuring Flow Graph for viewing TCP flows
- Creating IP-based statistics
- 5. Using Advanced Statistics Tools
- Introduction
- Configuring IO Graphs with filters for measuring network performance issues
- Throughput measurements with IO Graph
- Advanced IO Graph configurations with advanced Y-Axis parameters
- Getting information through TCP stream graphs – the Time-Sequence (Stevens) window
- Getting information through TCP stream graphs – the Time-Sequence (tcp-trace) window
- Getting information through TCP stream graphs – the Throughput Graph window
- Getting information through TCP stream graphs – the Round Trip Time window
- Getting information through TCP stream graphs – the Window Scaling Graph window
- 6. Using the Expert Infos Window
- 7. Ethernet, LAN Switching, and Wireless LAN
- 8. ARP and IP Analysis
- 9. UDP/TCP Analysis
- Introduction
- Configuring TCP and UDP preferences for troubleshooting
- TCP connection problems
- TCP retransmission – where do they come from and why
- Duplicate ACKs and fast retransmissions
- TCP out-of-order packet events
- TCP Zero Window, Window Full, Window Change, and other Window indicators
- TCP resets and why they happen
- 10. HTTP and DNS
- 11. Analyzing Enterprise Applications' Behavior
- Introduction
- Finding out what is running over your network
- Analyzing FTP problems
- Analyzing e-mail traffic and troubleshooting e-mail problems – POP, IMAP, and SMTP
- Analyzing MS-TS and Citrix communications problems
- Analyzing problems in the NetBIOS protocols
- Analyzing database traffic and common problems
- 12. SIP, Multimedia, and IP Telephony
- Introduction
- Using Wireshark's features for telephony and multimedia analysis
- Analyzing SIP connectivity
- Analyzing RTP/RTCP connectivity
- Troubleshooting scenarios for video and surveillance applications
- Troubleshooting scenarios for IPTV applications
- Troubleshooting scenarios for video conferencing applications
- Troubleshooting RTSP
- 13. Troubleshooting Bandwidth and Delay Problems
- 14. Understanding Network Security
- A. Links, Tools, and Reading
- 3. Module 3
- 1. Welcome to the World of Packet Analysis with Wireshark
- 2. Filtering Our Way in Wireshark
- 3. Mastering the Advanced Features of Wireshark
- 4. Inspecting Application Layer Protocols
- 5. Analyzing Transport Layer Protocols
- 6. Analyzing Traffic in Thin Air
- 7. Network Security Analysis
- 8. Troubleshooting
- 9. Introduction to Wireshark v2
- Bibliography
- Index
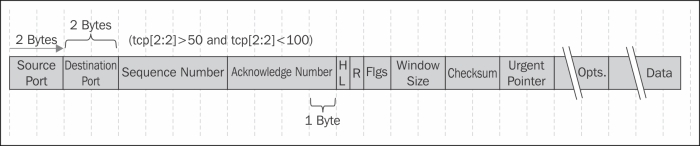
Byte offset and payload matching filters come to provide us with a flexible tool for configuring self-defined filters (filters for fields that are not defined in the Wireshark dissector and filters for proprietary protocols). By understanding the protocols that we work with and understanding their packet structure, we can configure filters that will watch a specific string in the captured packets, and filter packets according to it. In this recipe we will learn how to configure these types of filters, and we will also see some common and useful examples of the subject.
To configure byte offset and payload matching filters, start Wireshark and follow the instructions in the Configuring capture filters recipe in the beginning of this chapter.
- String matching filters comes to check a specific string in the packet header. It comes in the following format:
proto [Offset: bytes]
With this filter we can create filters for strings over IP, TCP, and UDP.
- For IP string-matching filters you can create the following filter:
ip [Offset:Bytes] - For matching application data, that is, to look into the application data that is carried by TCP or UDP, the most common uses of it are:
tcp[Offset:Bytes]Orudp[Offset:Bytes].
The general structure of offset filter is:
proto [Offset in bytes from the start of the header : Number of bytes to check]
Common examples for string matching filters are:
- For filtering destination TCP ports between 50 and 100, configure
(tcp[2:2] > 50 and tcp[2:2] < 100).Here we count two bytes from the beginning of the TCP header, and check the next two bytes to be lower than 100 and higher than 50.
- For checking TCP window size smaller then 8192, configure
tcp[14:2] < 8192.Here we count two bytes from the beginning of the TCP header, and check the next two bytes (the window size) to be less than 8192.

There's a nice string-matching capture filter generator in http://www.wireshark.org/tools/string-cf.html
You can also see additional filters in the tcpdump man pages:
- To print all IPv4 HTTP packets to and from port 80, (that is to print only packets that contain data, not, for example, SYN, FIN or ACK-only packets), configure the following filter:
tcp port 80 and (((ip[2:2] - ((ip[0]&0xf)<<2)) - ((tcp[12]&0xf0)>>2)) != 0). - To print the start and end packets (the SYN and FIN packets) of each TCP conversation that involves a non-local host, configure
tcp[tcpflags] & (tcp-syn|tcp-fin) != 0 and not src and dst net <localnet>. - To print IP broadcast or multicast packets that were not sent via Ethernet broadcast or multicast, configure
ether[0] & 1 = 0 and ip[16] >= 224. - To print all ICMP packets that are not echo requests/replies (that is, not ping packets), configure
icmp[icmptype] != icmp-echo and icmp[icmptype] != icmp-echoreply.
- There is a string calculator at http://www.wireshark.org/tools/string-cf.html.
It doesn't always provide working results, but it might be a good place to start from.
- Another interesting blog can be found on http://www.packetlevel.ch/html/txt/byte_offsets.txt.
-
No Comment