dnsenum is a very simple and easy-to-use tool for enumerating and resolving DNS information for a given target. Additionally, it has the ability to automatically perform DNS zone transfers using the nameserver details:
- Open a new Terminal window and execute the dnsenum command. The Help menu appears, providing detailed descriptions of various operators/parameters and their use.
- Use the dnsenum zonetransfer.me command to perform DNS enumeration on the zonetransfer.me domain, as shown in the following screenshot:
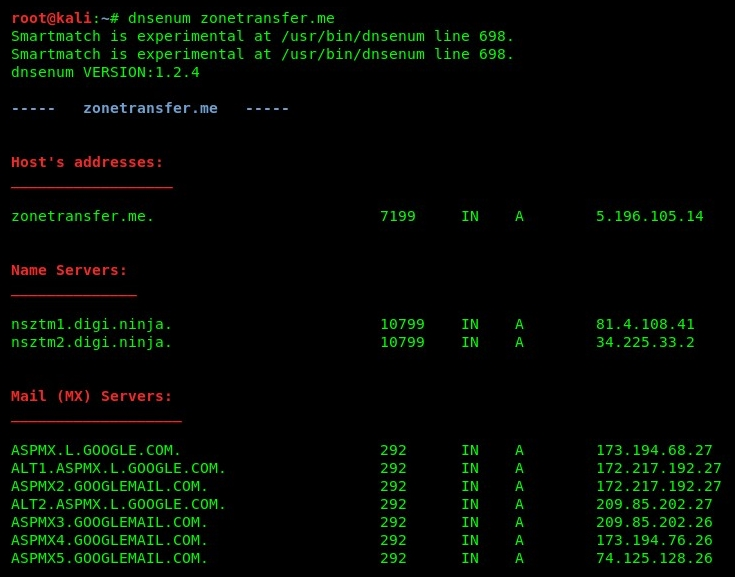
dnsenum
dnsenum will attempt to obtain all of the servers and hostnames for the given domain. We are able to obtain the nameservers, mail servers (used for email exchange), and IP addresses for each server and hostname found.
- dnsenum will attempt to perform a DNS zone transfer by querying the specific nameservers found during the enumeration process, as shown in the following screenshot:
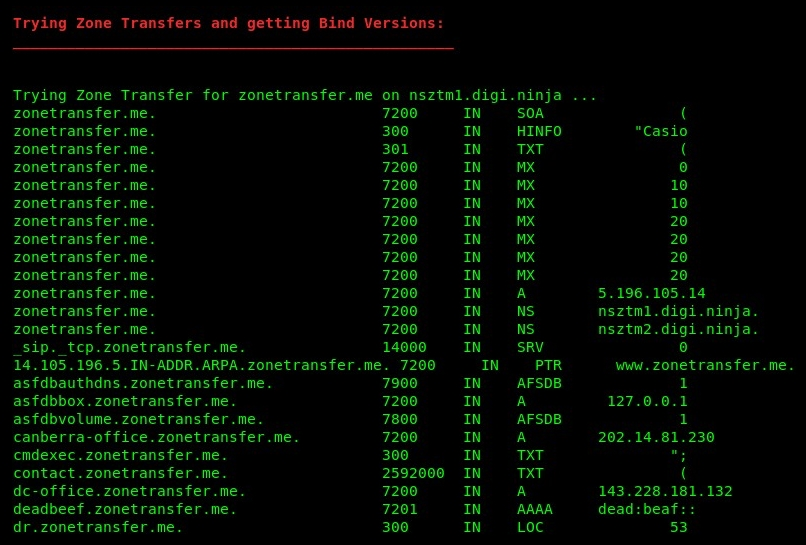
DNS zone transfer
As in the preceding snippet, the dnsenum tool was able to successfully extract/replicate the master zone records from the nsztml.digi.ninja nameserver. Using the information found, a penetration tester will have better insights into the target organization's (zonetransfer.me) internal and external network devices.
Access to sensitive information such as what we have found can potentially lead to a successful network breach in the target organization.
Up next, we will attempt to perform DNS analysis using a native Linux tool.
