In this section, we'll discuss how to configure your wireless security features on your access point and wireless router so that you can secure your network.
For this exercise, I am using a Linksys EA6350 wireless router. Please note that all wireless routers and access points have the same features within their management interface; however, the graphical user interface (GUI) for each manufacturer and device may vary.
Let's get started!
- You'll need to log in to your access point or wireless router.
- Once logged in, click on the Wireless tab within the user interface. Here, you'll be able to change the network name (SSID), set a complex password, set a security mode, and broadcast the SSID, as shown in the following screenshot:
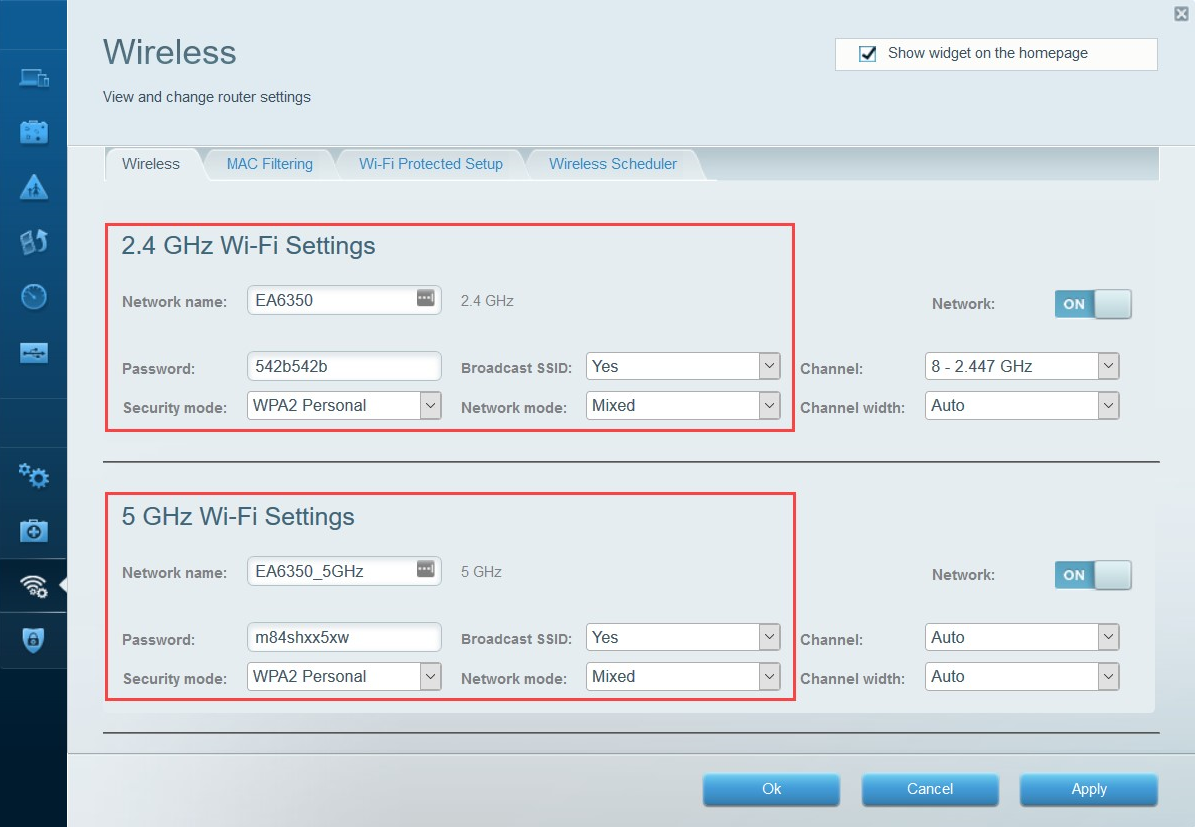
Using the following guidelines will assist in improving the security posture of your wireless network:
-
- Change the SSID (network name) to something that won't attract prying eyes.
- Hide (broadcast) the SSID.
- Create a complex password. If you're having difficulties, try using an online password generator.
Each modern access point and wireless router allows various security modes, such as the following:
-
- None: Disables authentication.
- WEP: Uses the WEP encryption standard.
- WPA Personal: Uses the WPA encryption standard and allows you to set a pre-shared key (PSK) on the access point. Therefore, any device that requires access to the wireless network will be required to provide the PSK.
- WPA Enterprise: This mode applies the WPA encryption standard, but note that the access point stores user credentials in WPA Personal. WPA Enterprise queries a central authentication, authorization, and accounting (AAA) server to verify user access on the wireless network.
- WPA2 Personal: Uses the WPA2 encryption standard.
- WPA2 Enterprise: Uses the WPA2 encryption standard with the AAA server.
You can choose to disable the SSID broadcast to cloak your network.
- Next, you should see another sub-tab that allows you to configure MAC filtering.
- Enable the MAC filtering feature. Once enabled, you'll have the option to add MAC addresses to an allow or deny list, as shown in the following screenshot:

- Lastly, disable the Wi-Fi Protected Setup feature, as shown in the following screenshot:
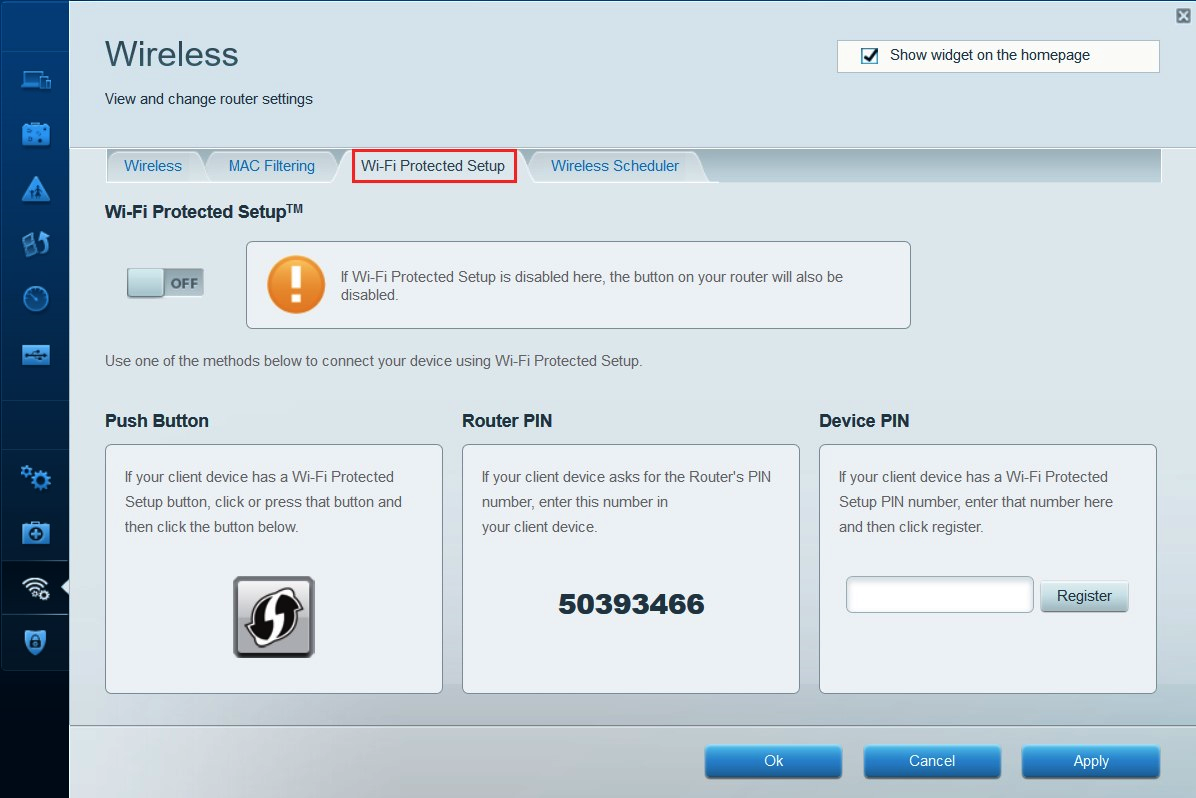
WPS has known security vulnerabilities and should not be used in secure environments.
Having completed this exercise, you are now able to configure and set up a wireless network. In the next section, we will look at the essentials of exploiting perimeter systems.
