SQLi allows an attacker to insert a series of malicious SQL code/queries directly into the backend database server. This allows the attacker to manipulate records such as add, remove, modify, and retrieve entries in a database:
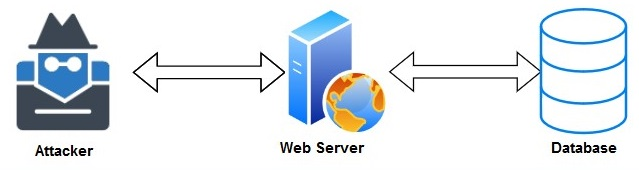
The attacker can leverage the vulnerability of web applications to bypass security controls and measures to gain entry to the database server/application. SQLi attacks are injected via the address bar on the web browser or the login portal of a website.
Next, we will discuss insecure deserialization.
