Lateral movement allows an attacker to pivot all attacks through a compromised machine to other subnets within an organization. Let's imagine you're conducting a penetration test on a client's network. Their organization contains multiple subnets but they haven't informed you about the number of networks that actually exist. So, you start to scan the network to look for live hosts and vulnerabilities, and to discover the topology.
You've discovered and mapped the entire 10.10.10.0/24 network and you begin to exploit as many machines as possible. However, during your exploitation phase, you notice something interesting on a particular victim machine, and, on the Meterpreter shell, you execute the ipconfig command to view the IP configurations on the victim's machine:

In our scenario, Interface 11 is connected to the same subnet as our attacker machine, and Interface 18 is on another network. In some situations, if you attempt to access another subnet, a router or firewall may be configured to restrict access between different subnets for security purposes.
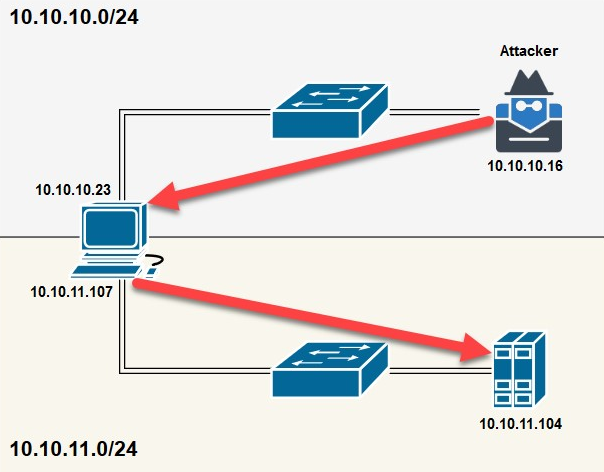
To get past security appliances and network access controls, the technique of lateral movement (pivoting) should be used. As the attacker, we can attempt to compromise a machine that is connected and is trusted on other subnets within the organization. Once we've set up pivoting or lateral movement, all our attacks will be sent through the victim machine and forwarded to the new target network, as shown in the following screenshot:
To perform lateral movement using Metasploit, observe the following instructions:
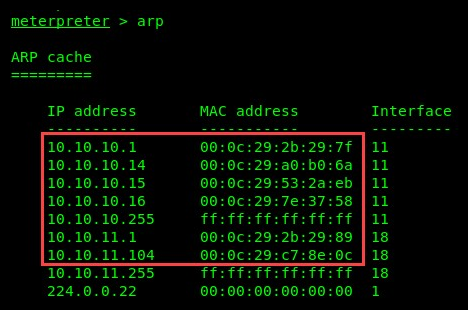
- Using the arp command on Meterpreter will display the ARP cache. In the following screenshot, there are two different networks connected to our victim:
- To enable lateral movement, execute the run post/multi/manage/autoroute command within Meterpreter, as shown in the following screenshot:

This will add a route to the additional networks and allow your attacker machine to send all its attacks to the victim machine (10.10.10.23) and forward them to the 10.10.11.0/24 network.
- To test lateral movement (pivoting), we can attempt to perform a NetBIOS scan on the 10.10.11.0/24 network from our attacker machine:

The following results prove that our attacker machine is able to perform scans and attacks on another subnet:

- Additionally, performing a TCP port scan on a target has proven fruitful since all attacks are sent through the 10.10.10.23 machine:
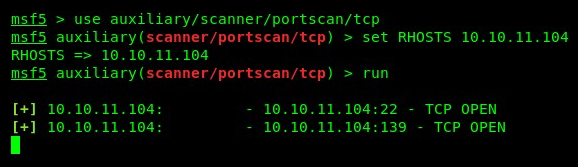
We can then target the new subnet.
During a penetration test, we may be tasked with discovering hidden or remote networks. For each system you have gained access to, be sure to check the ARP cache on the victim's machine and attempt to perform lateral movement throughout the network.
In the next section, we will take a look at using PowerShell to disable Windows Defender.
