NSE is one of the most powerful features within Nmap. It allows users to create and automate scripting to perform customized scans on a target device. By performing scans using various Nmap scripts, you can quickly detect whether your target is susceptible to a known vulnerability, malware, open backdoors, and so on.
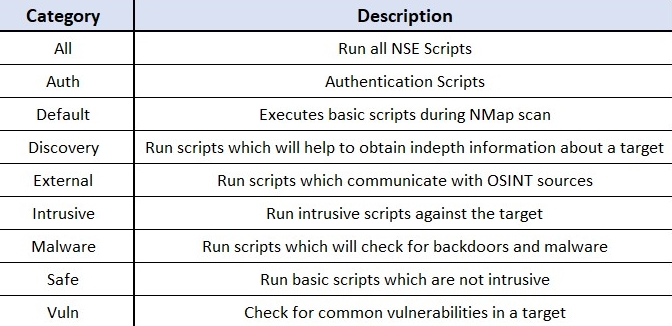
The following are the main categories of NSE scripts:
To execute an entire category of scripts, we can use the --script category command. The following snippet is an example of using the vuln category of scripts during an Nmap scan:
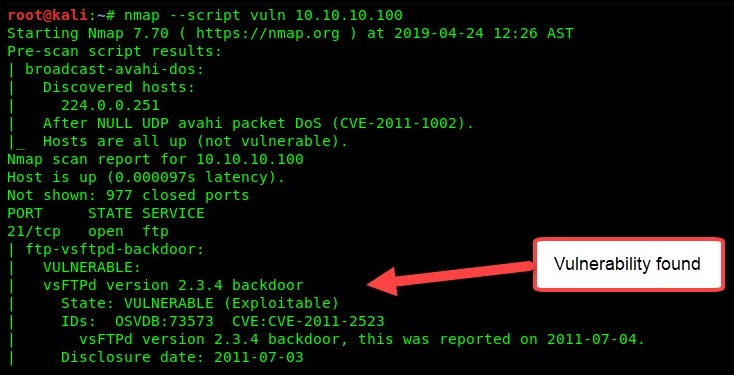
Running an entire category of scripts may not always be suitable for various situations. If you are performing a scan to search for systems that contain a specific vulnerability, such as vsFTPd 2.3.4 backdoor (CVE-2011-2523), you can use the following command:
nmap --script ftp-proftpd-backdoor target
Each NSE script is stored locally on Kali Linux in the /usr/share/nmap/scripts directory. However, you should become familiar with using NSE scripts, as this will help you to save time and find specific information about a target much more quickly. To help you to further understand NSE scripts, please visit the official NSE documentation website at https://nmap.org/nsedoc/. The repository contains a detailed description of each NSE script available.
Having completed this section on Nmap and NSE, let's now learn about Zenmap, the GUI version of Nmap.
